Project overview
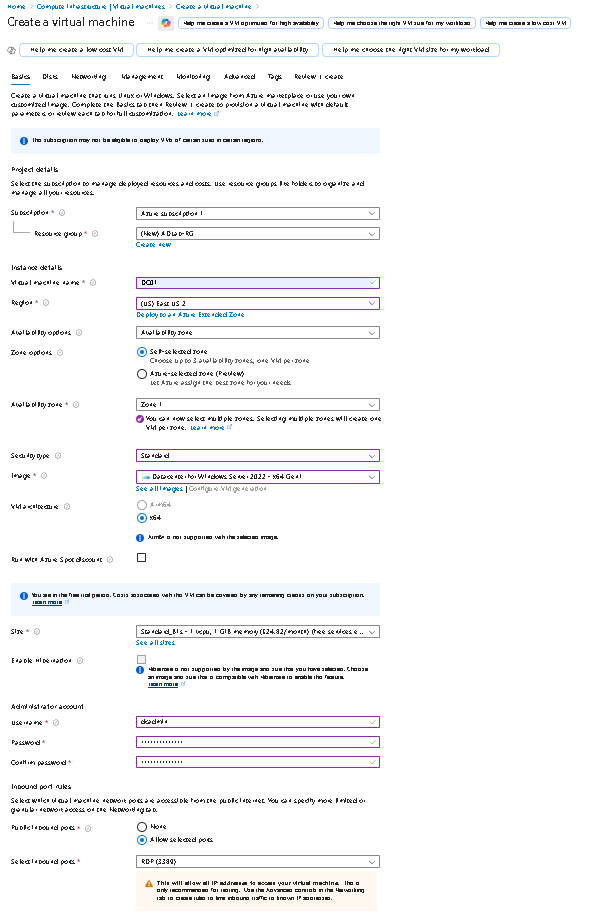
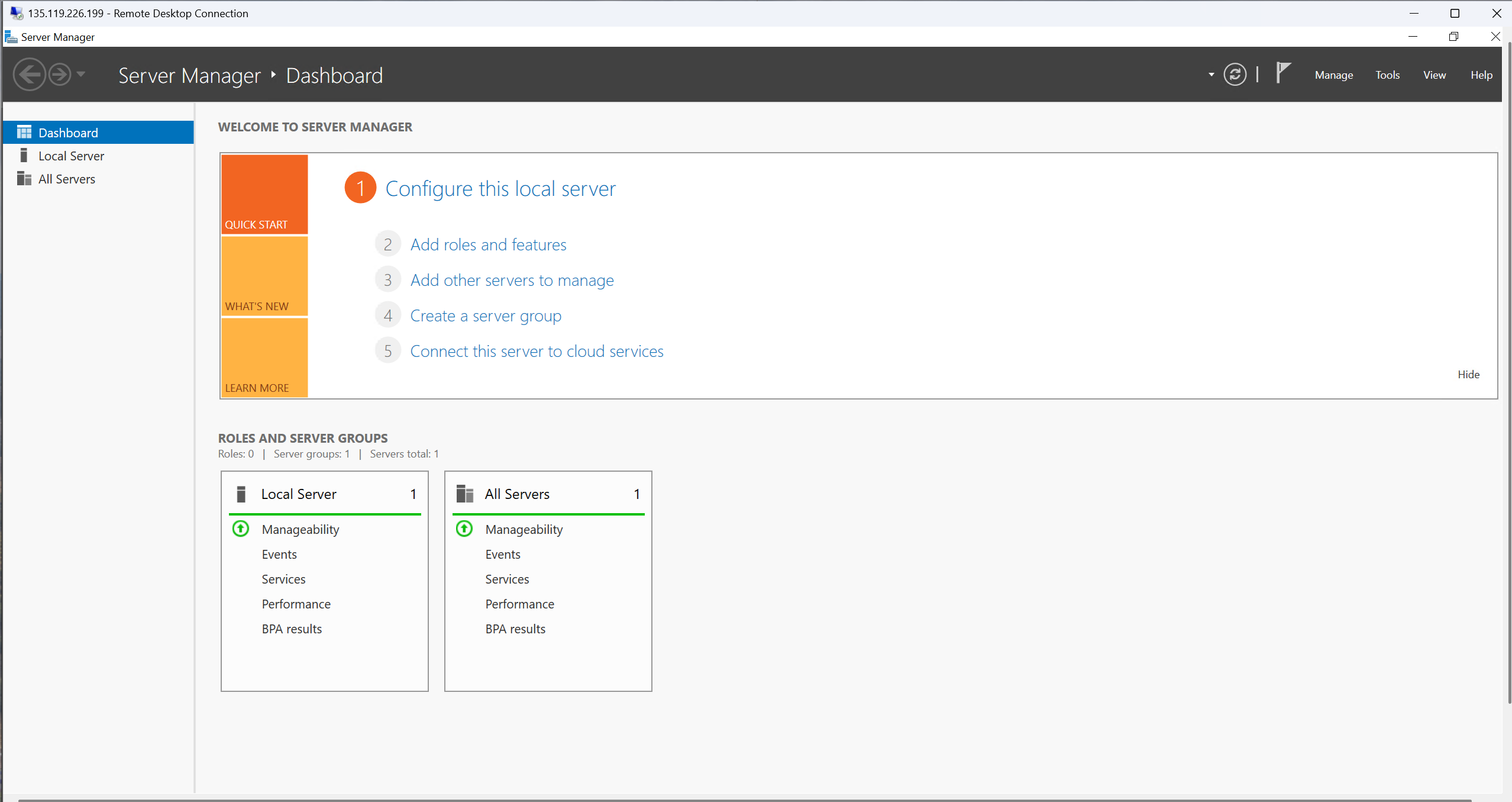
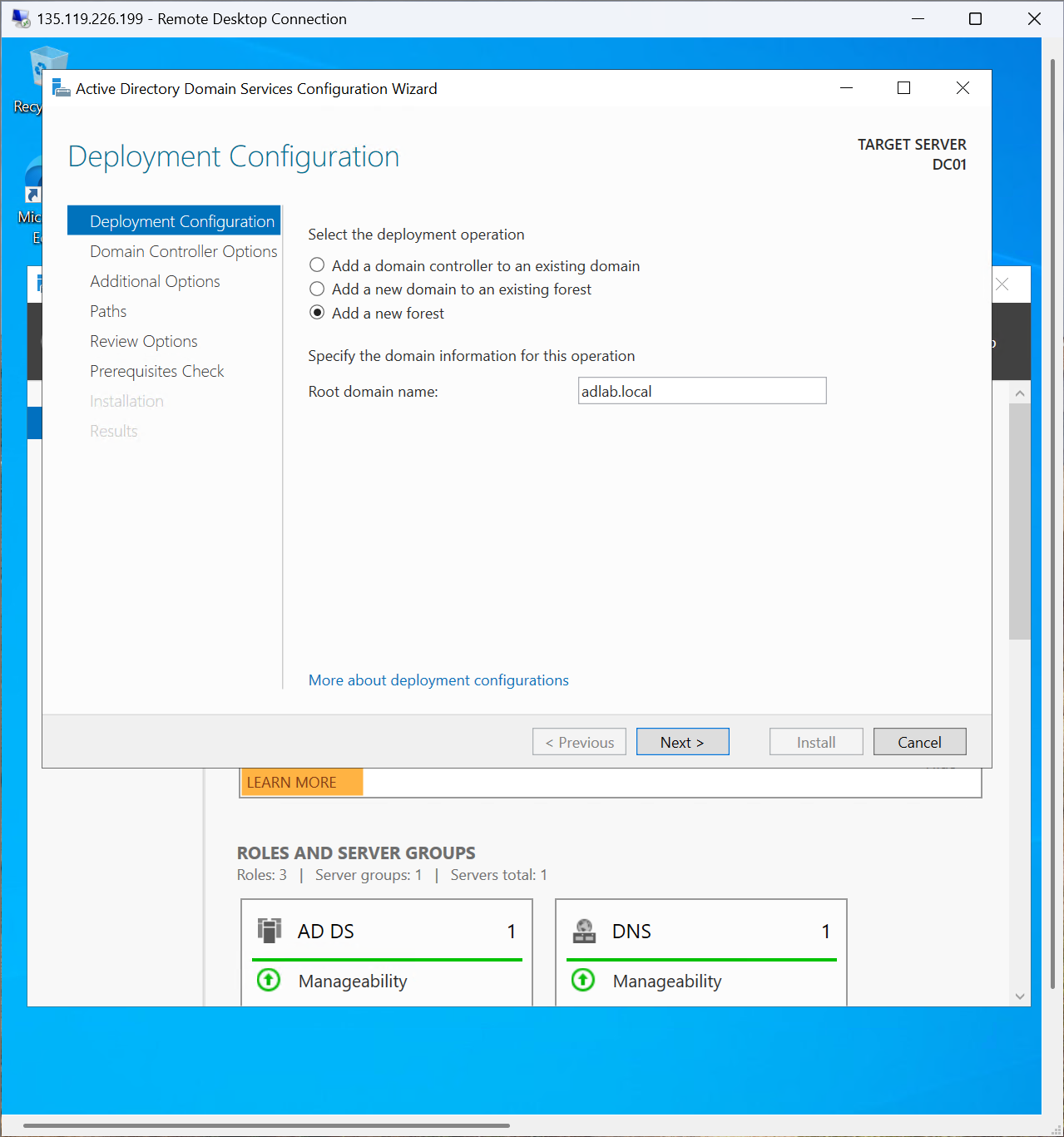
Provisioned a Windows Server 2022 VM in Azure, connected via RDP, and configured it
as DC01, the first domain controller for adlab.local.
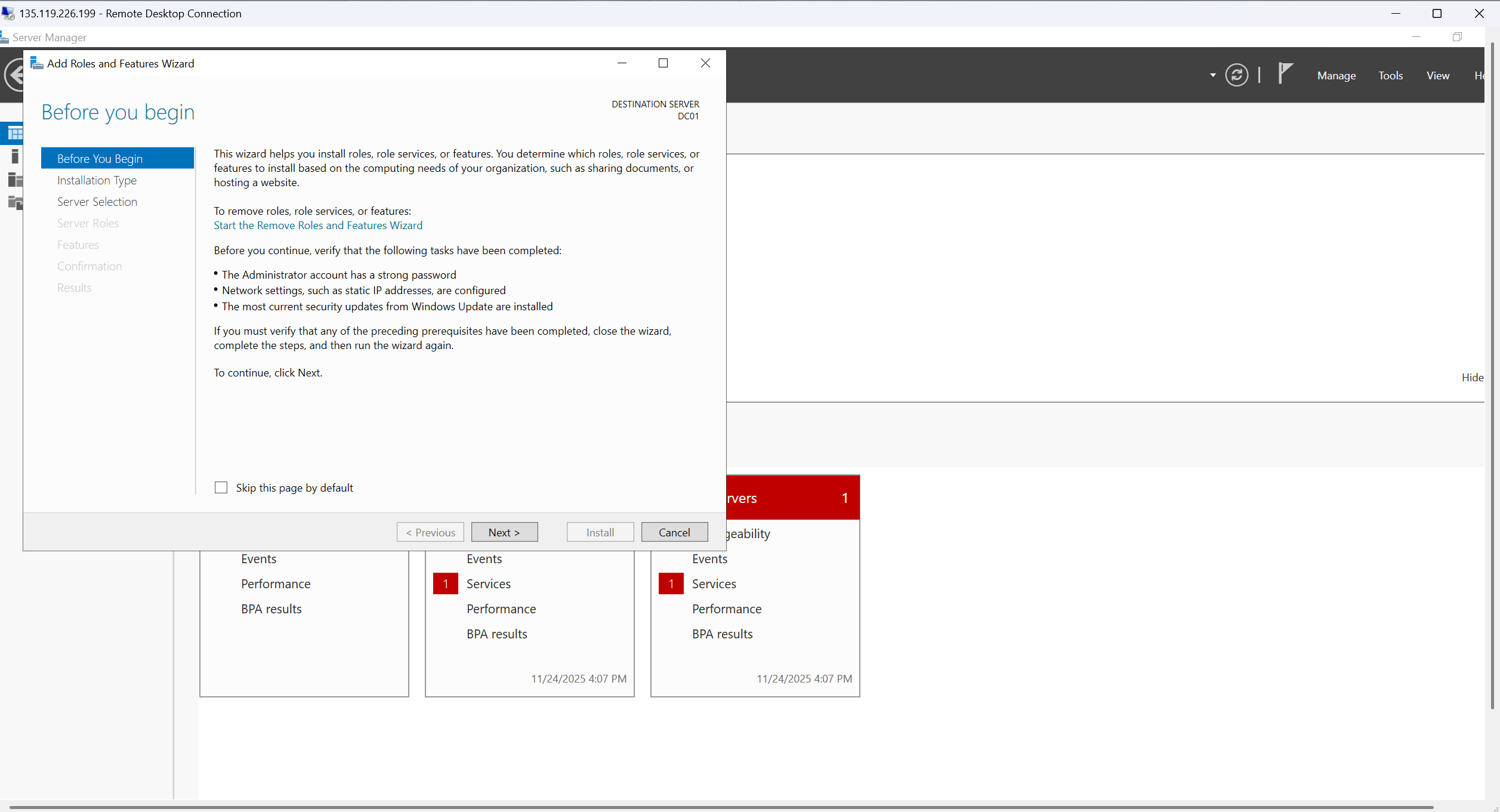
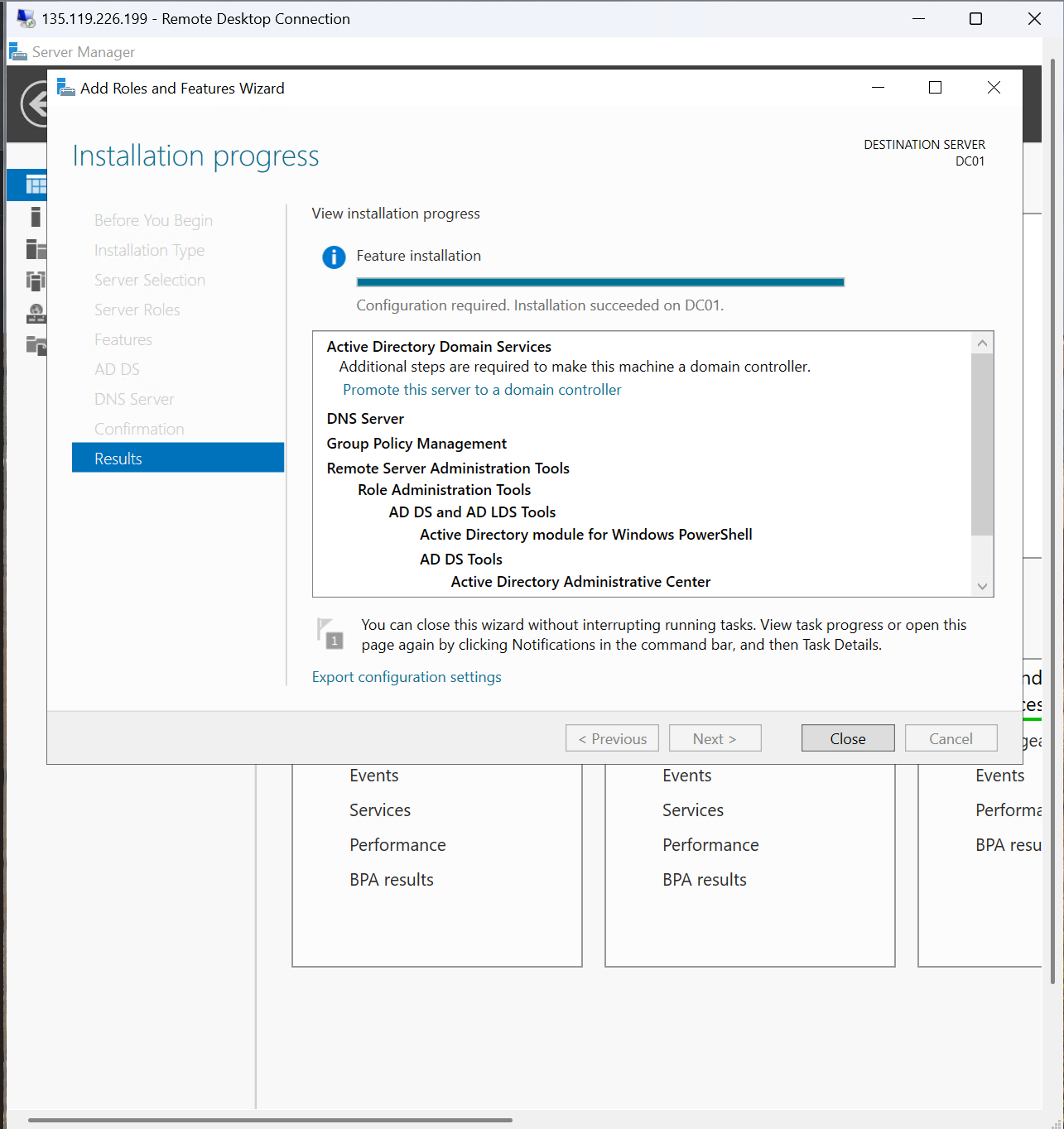
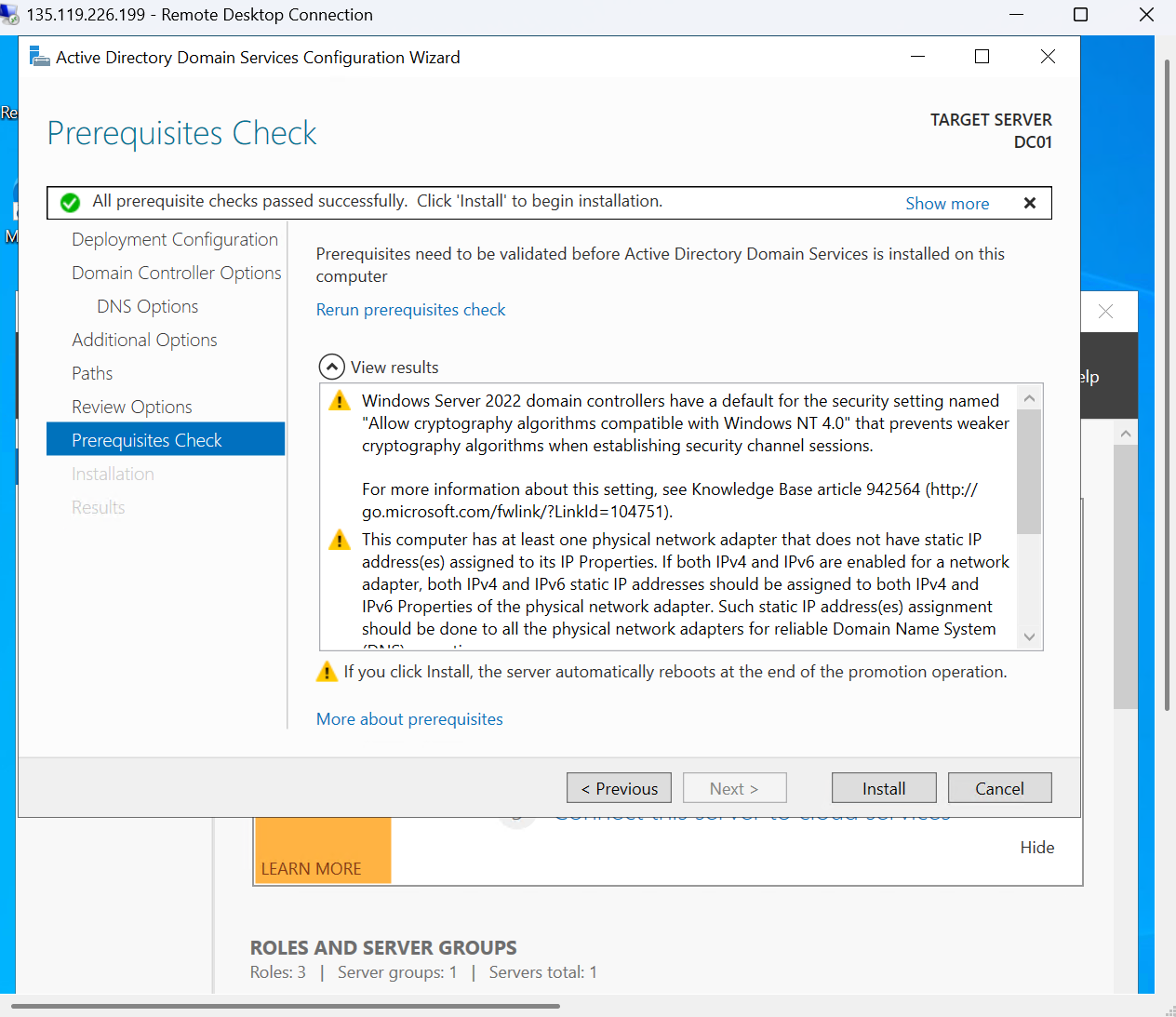
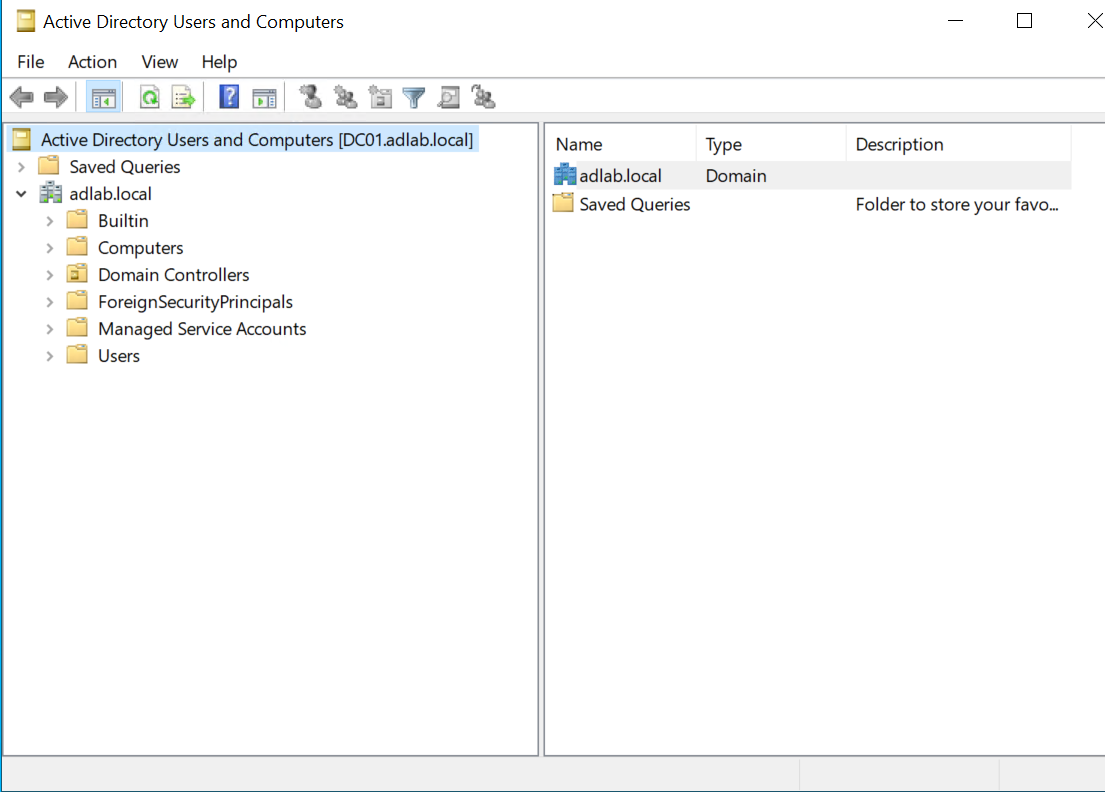
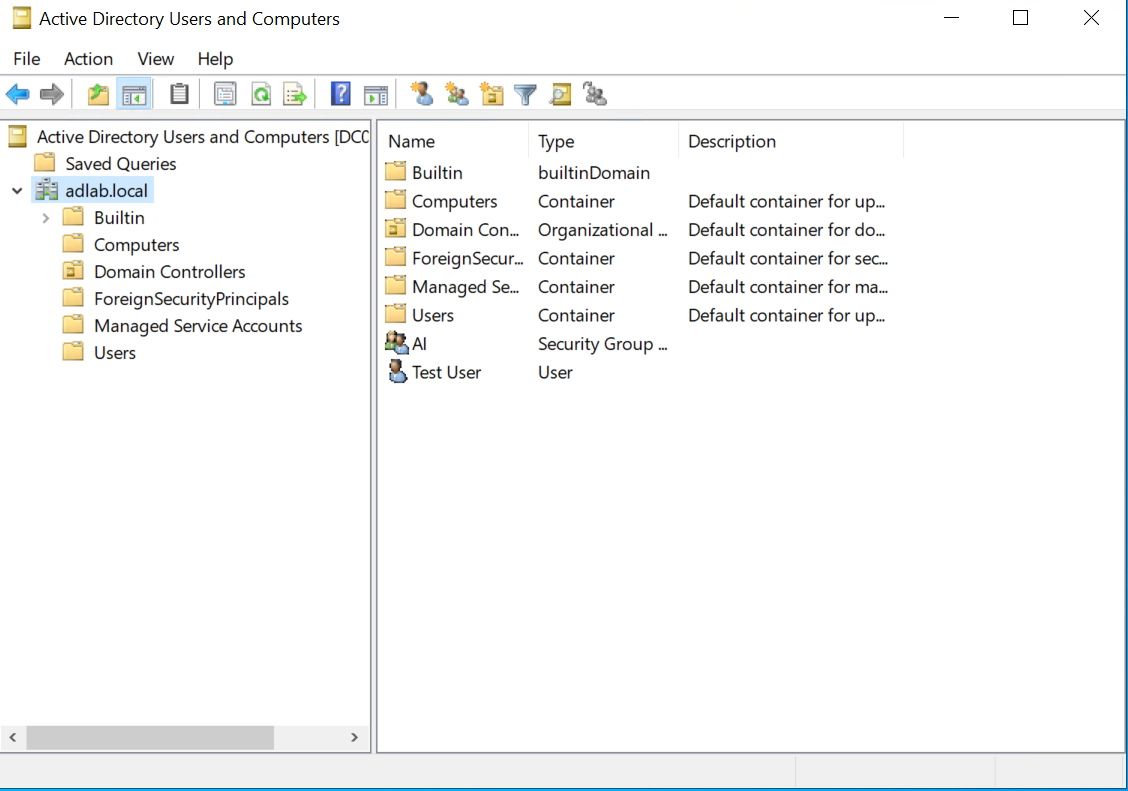
After installing AD DS and DNS, the server was promoted to a domain controller and
verified using Active Directory Users and Computers (ADUC).
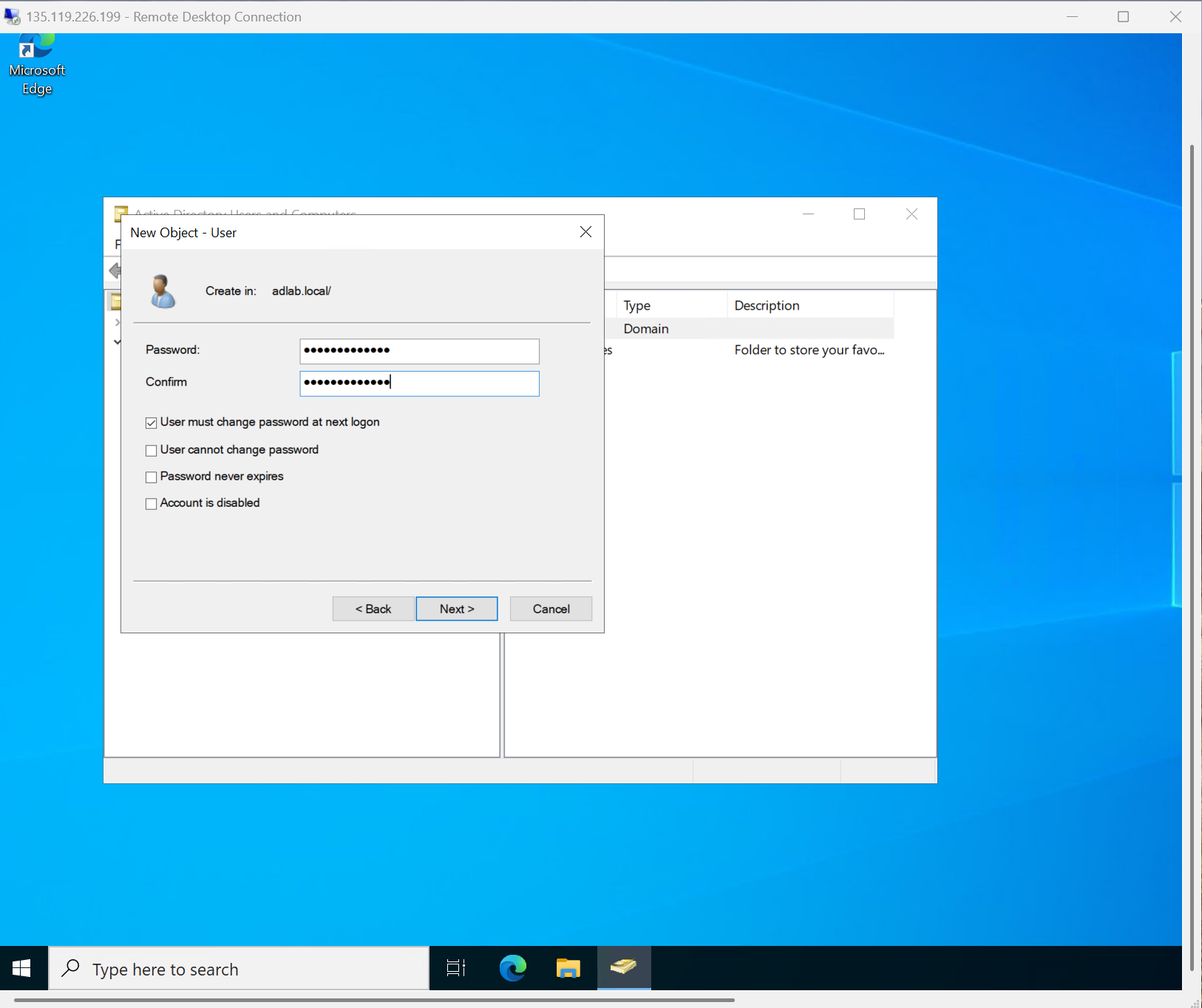
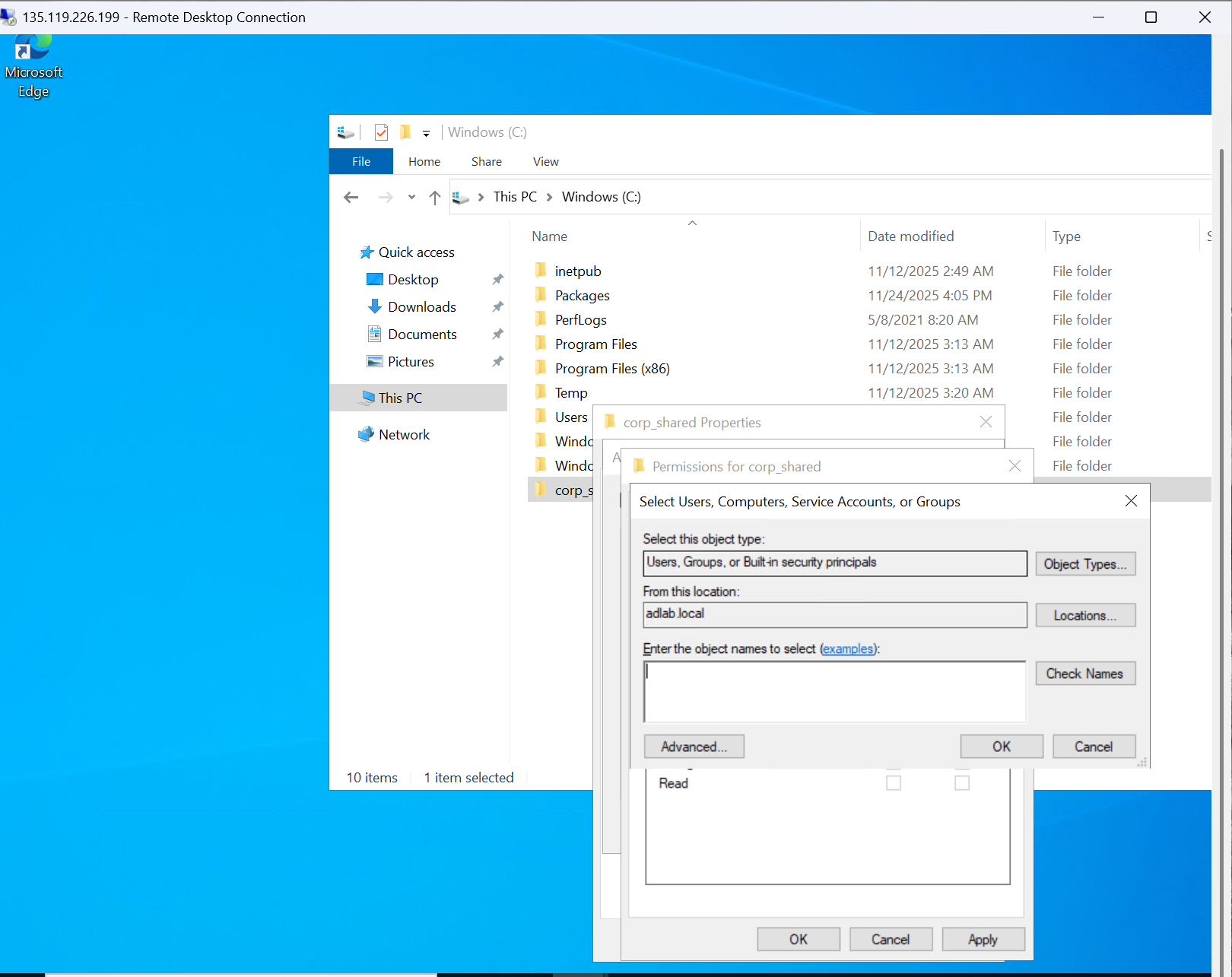
From there, the focus shifted to the identity lifecycle: creating a test user, designing a clean OU and group structure, and wiring up a shared folder that relies on group-based permissions — mirroring the daily tasks handled by entry-level IT and IAM teams.