Project overview
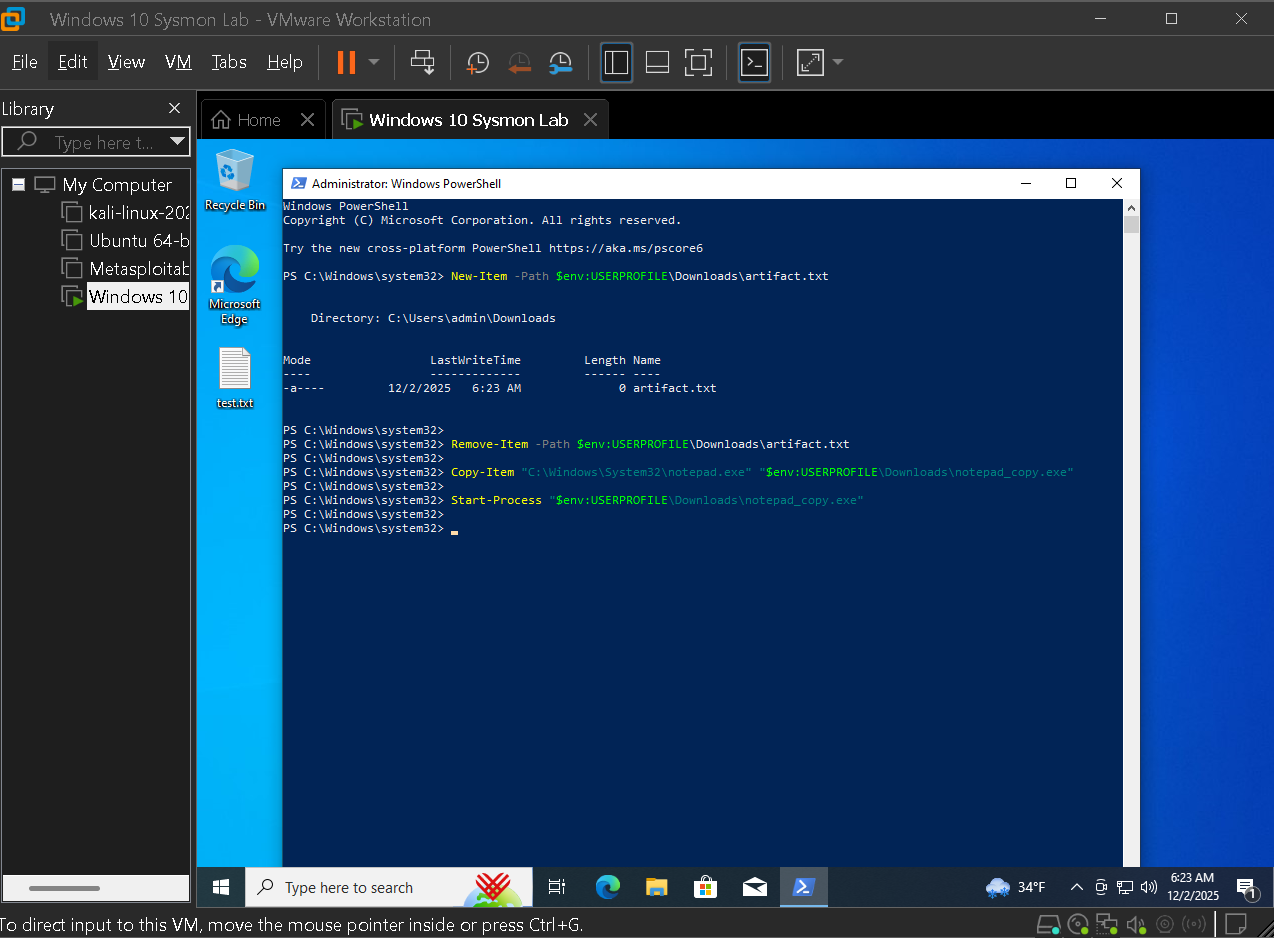
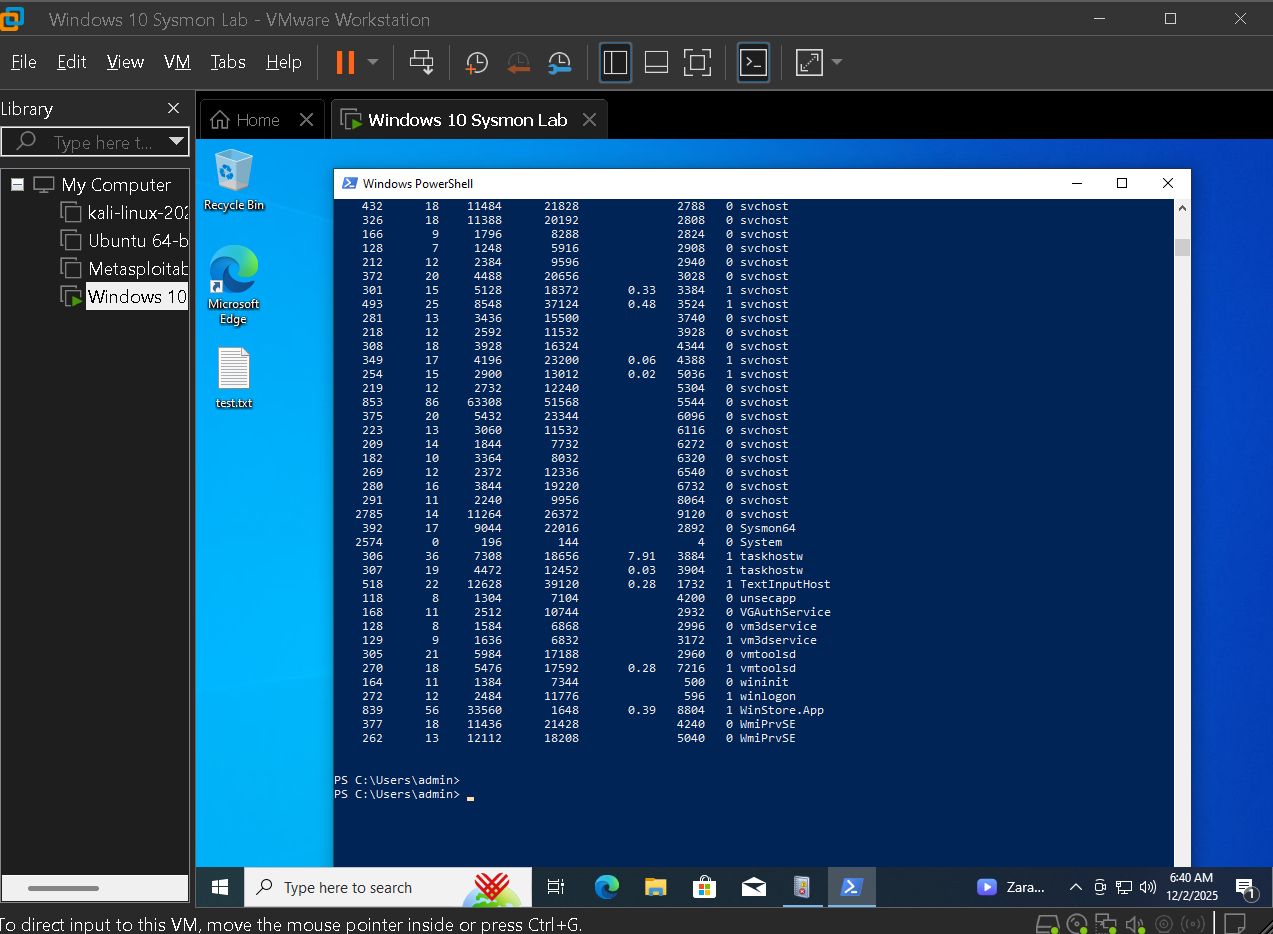
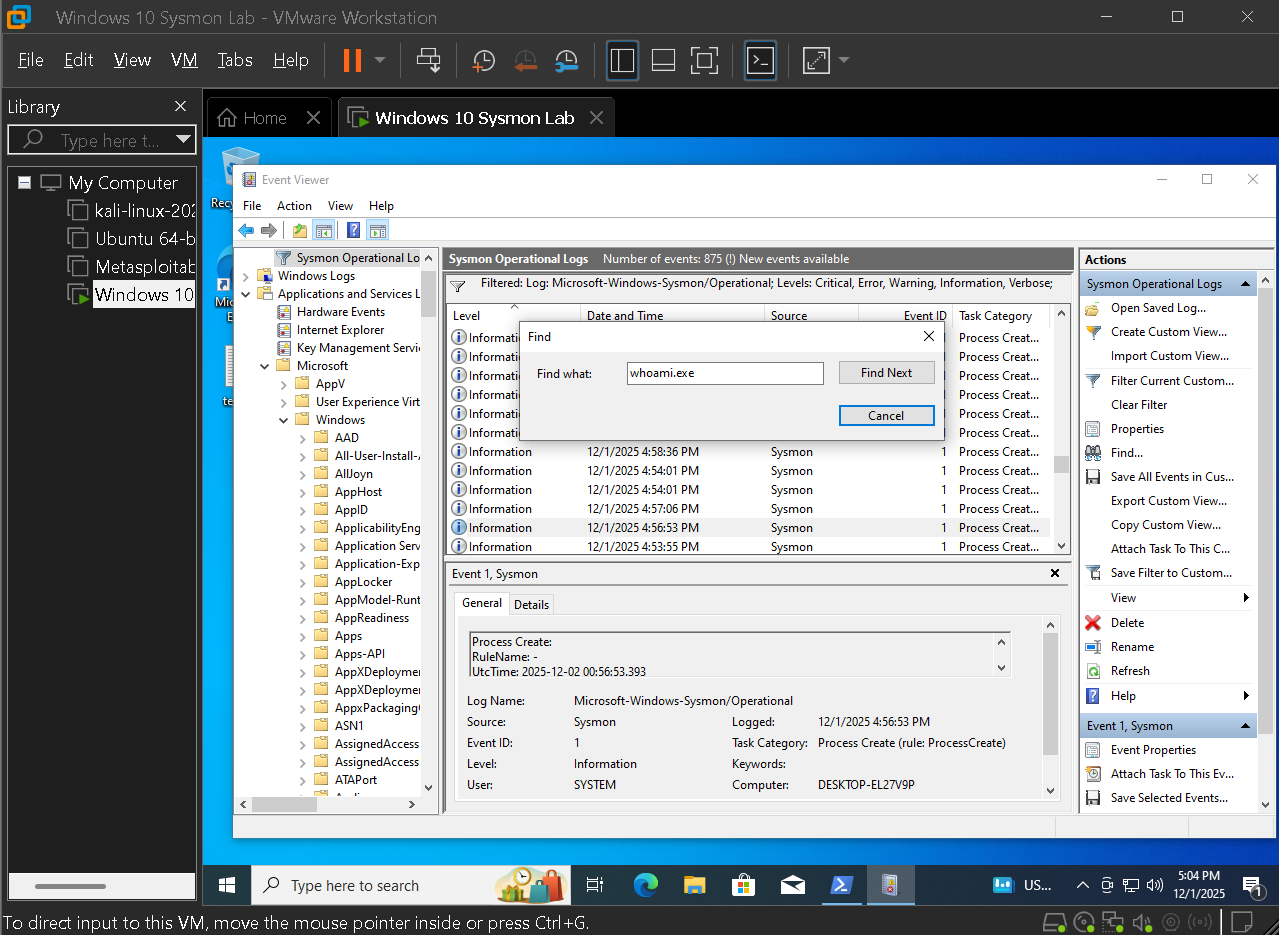
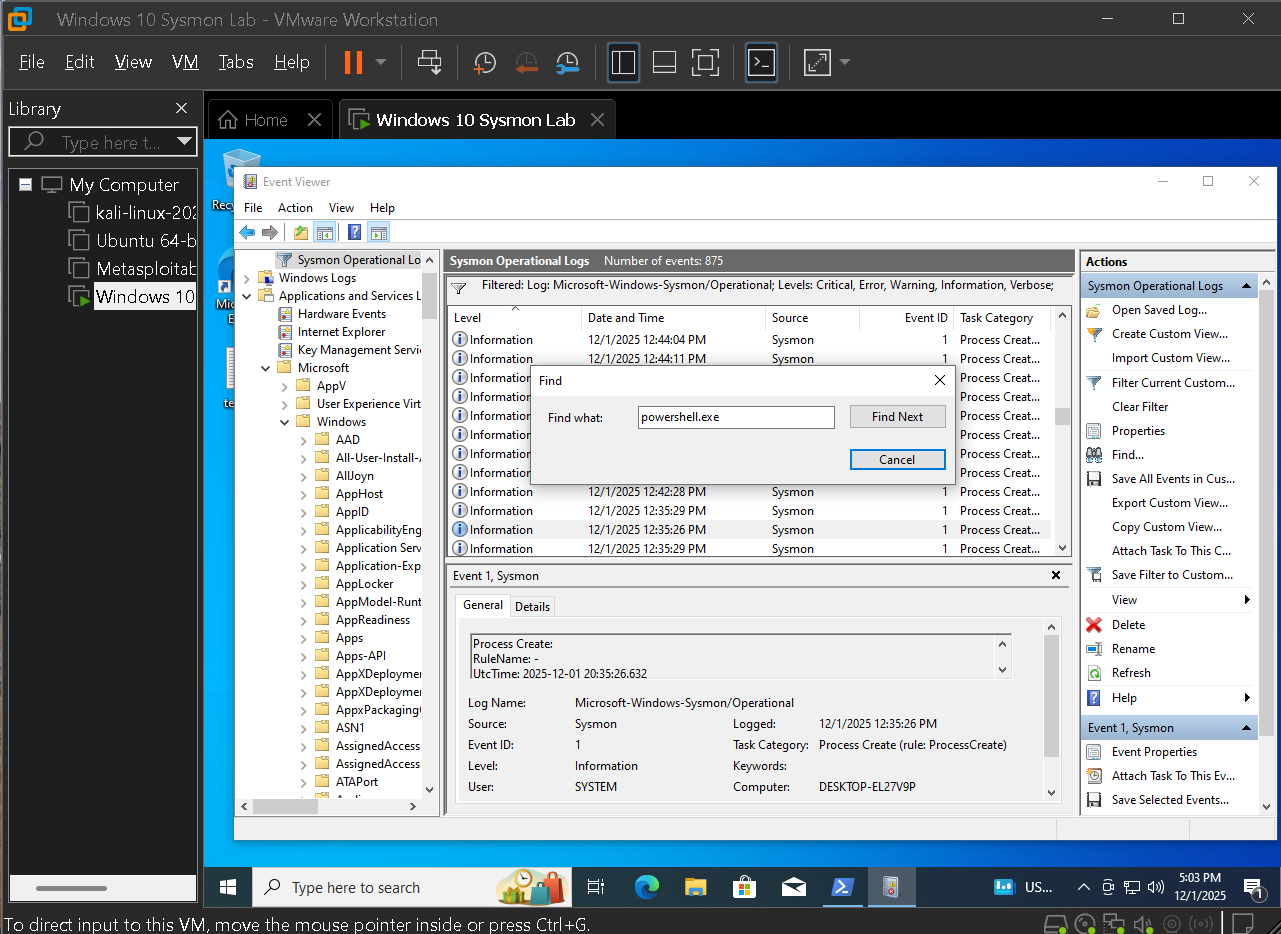
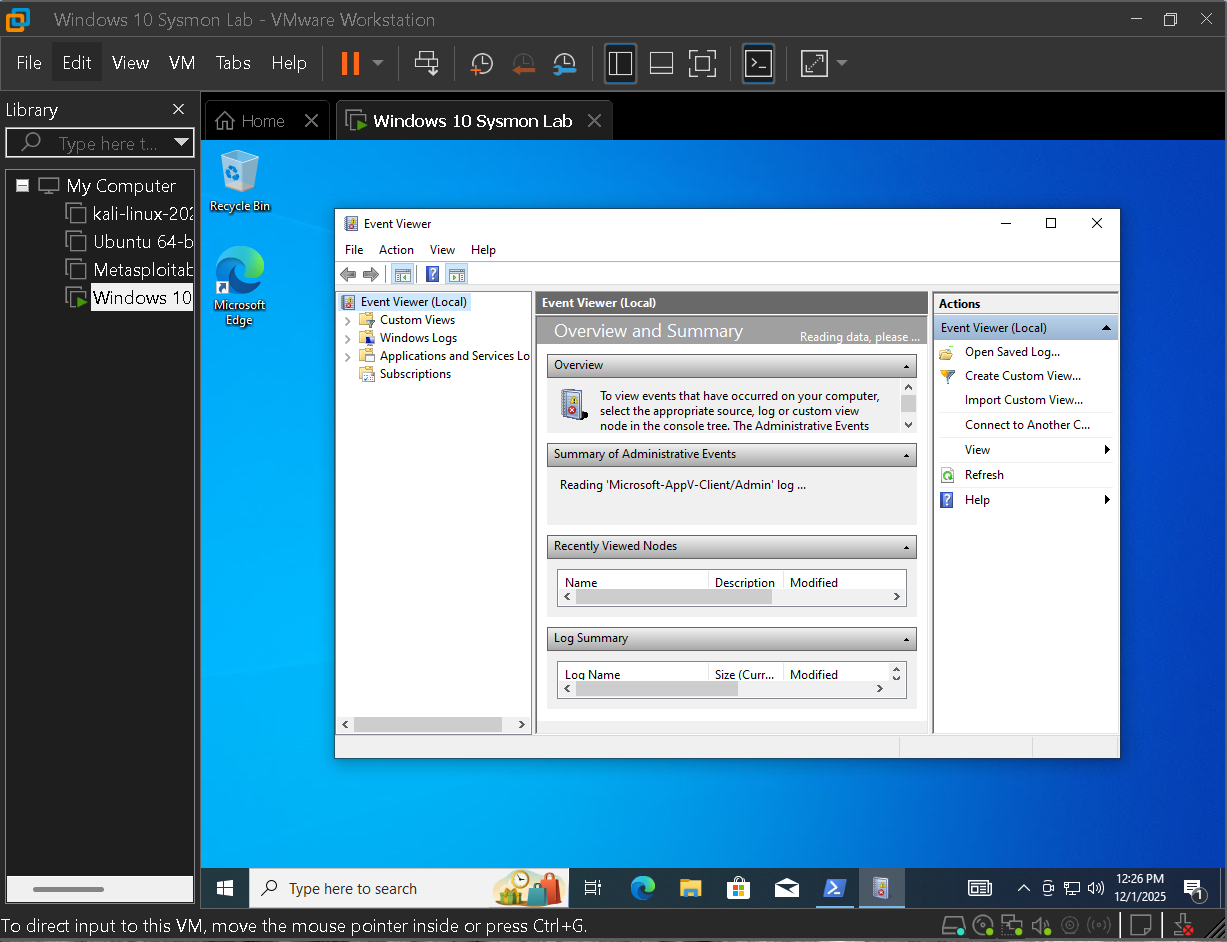
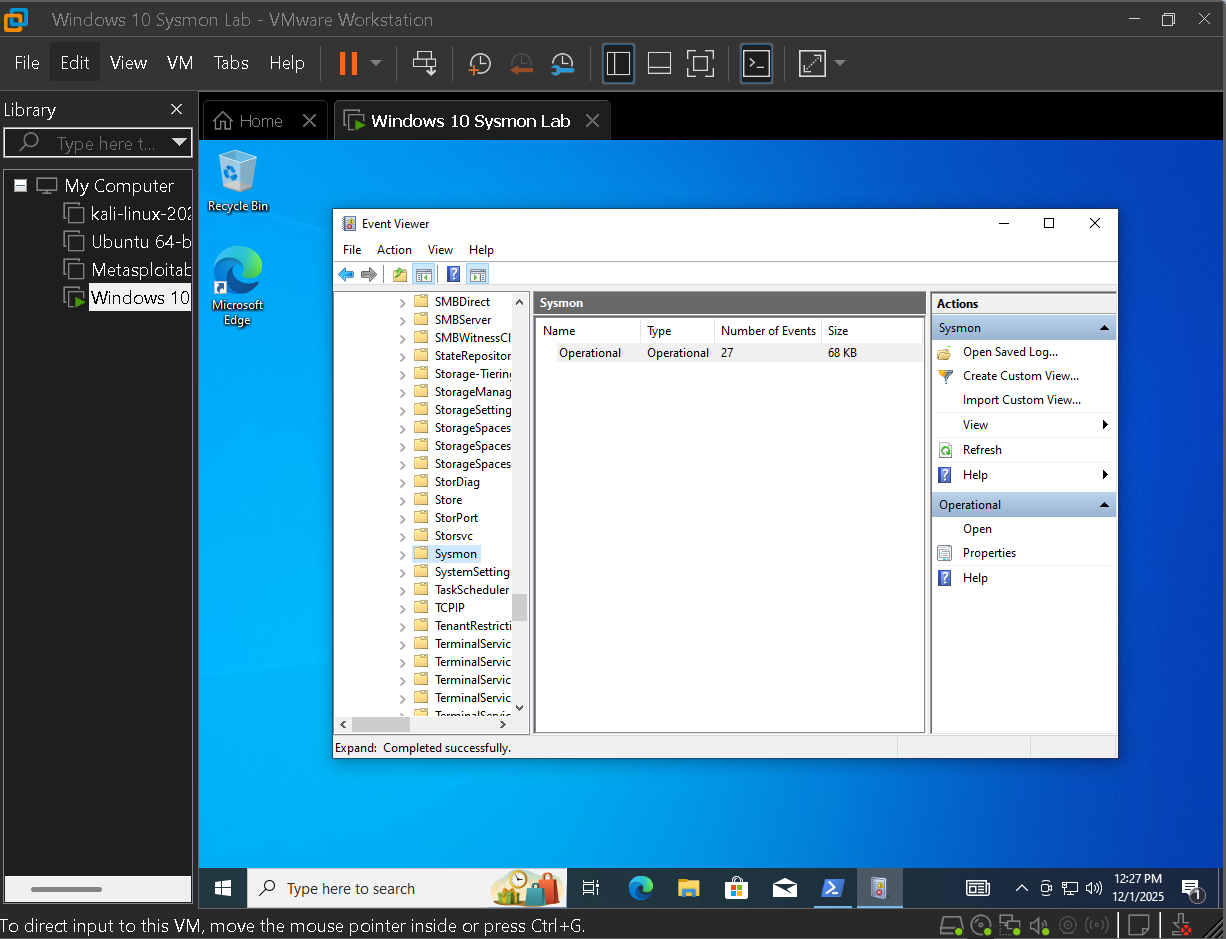
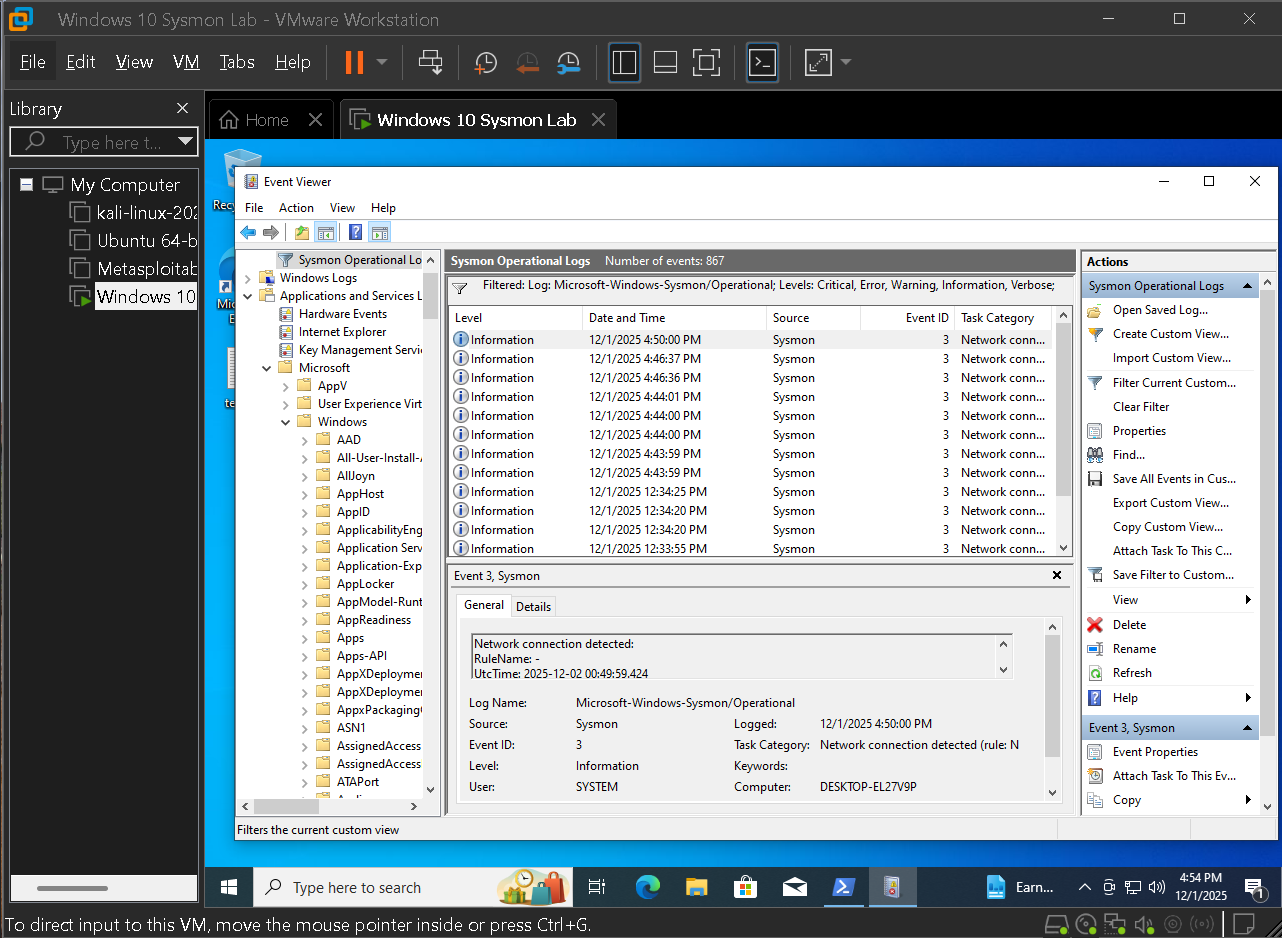
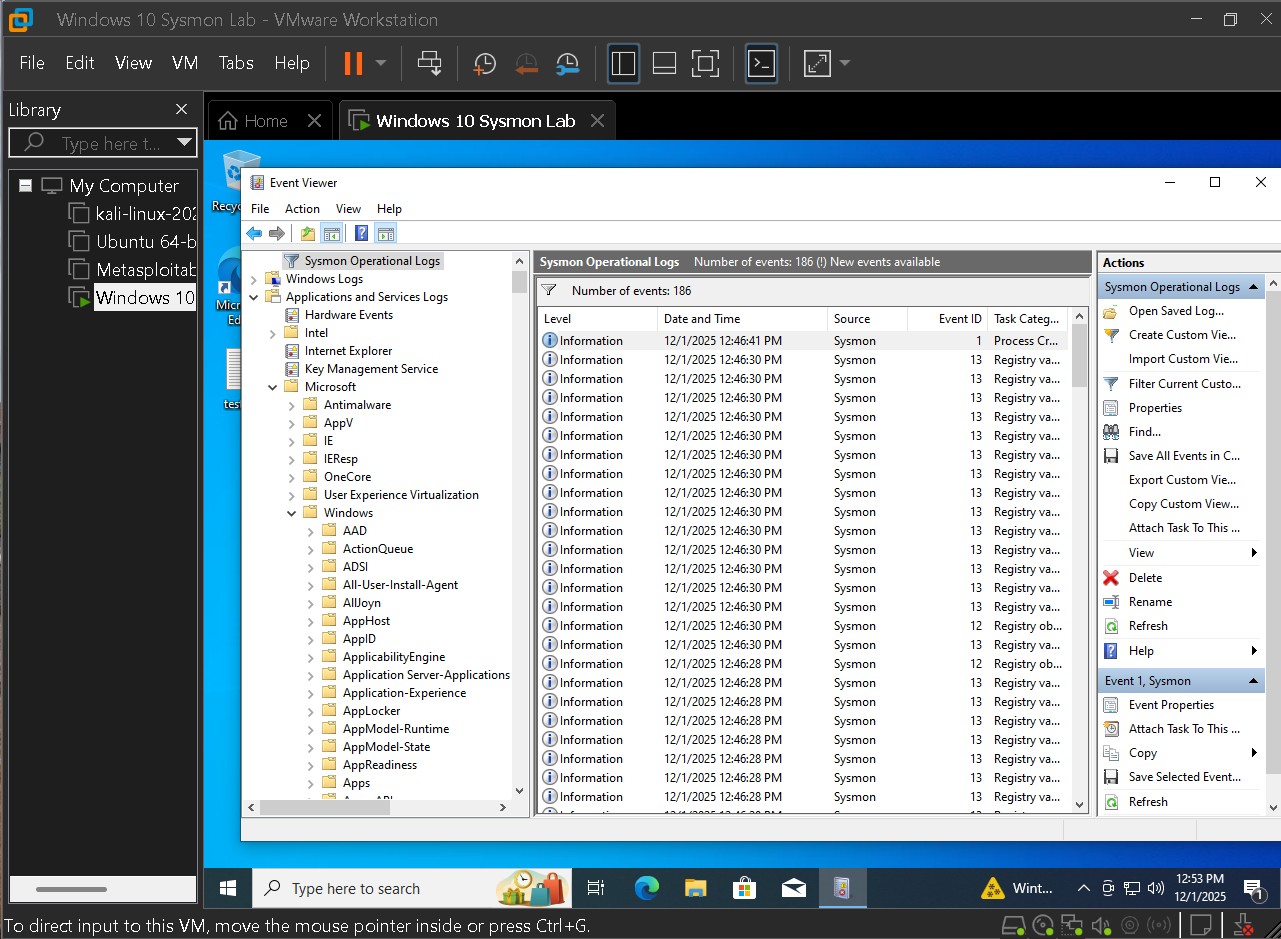
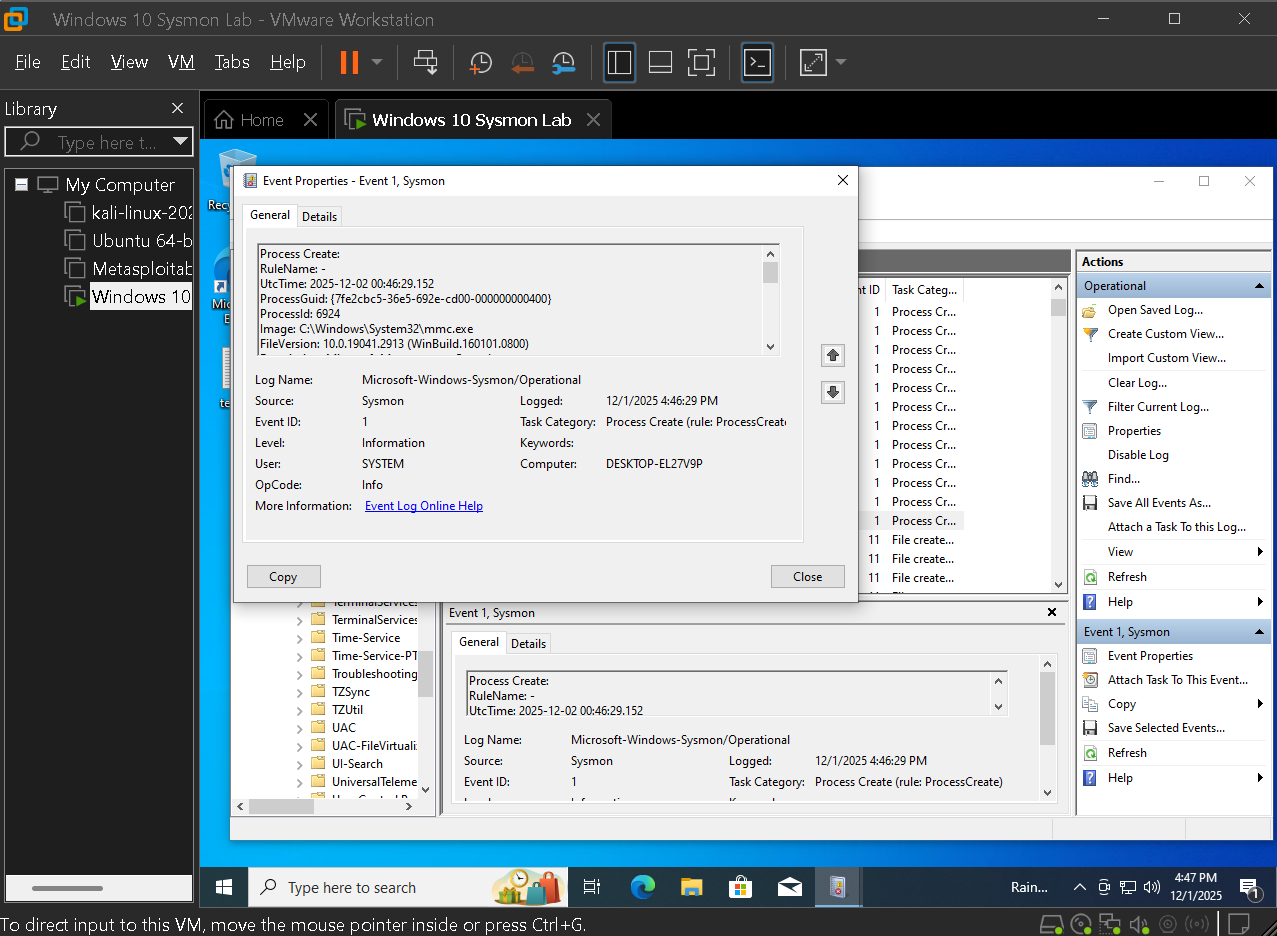
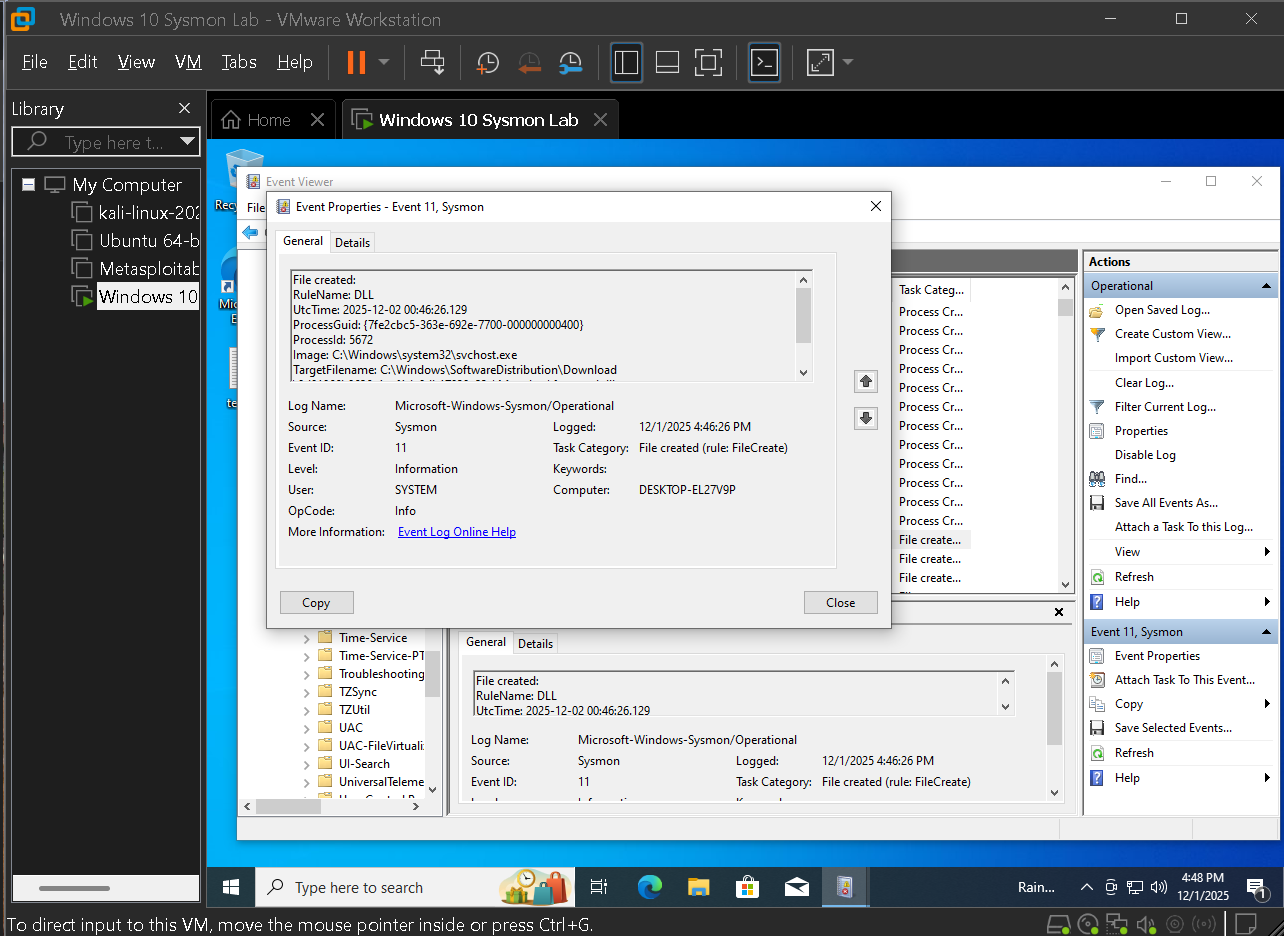
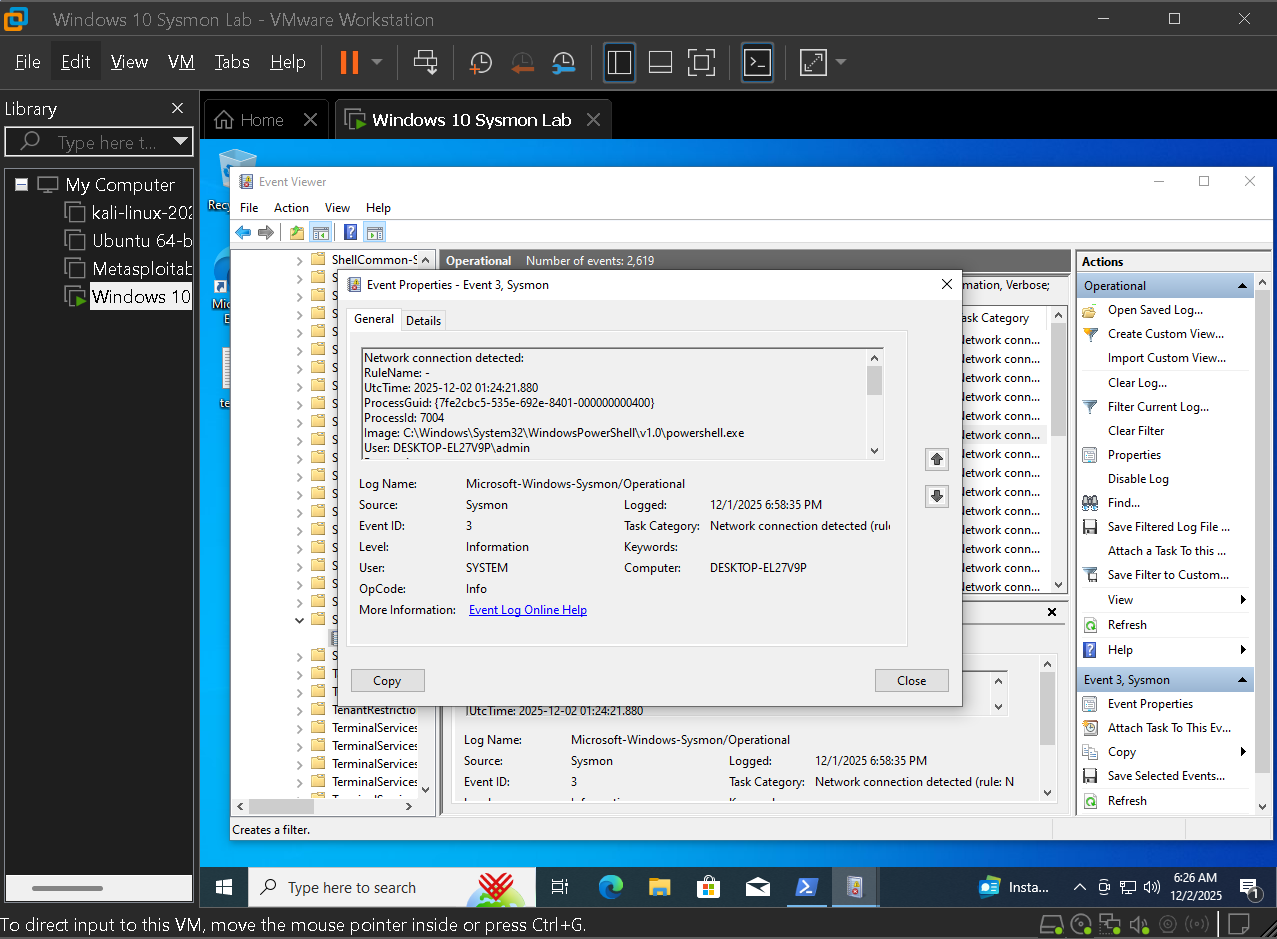
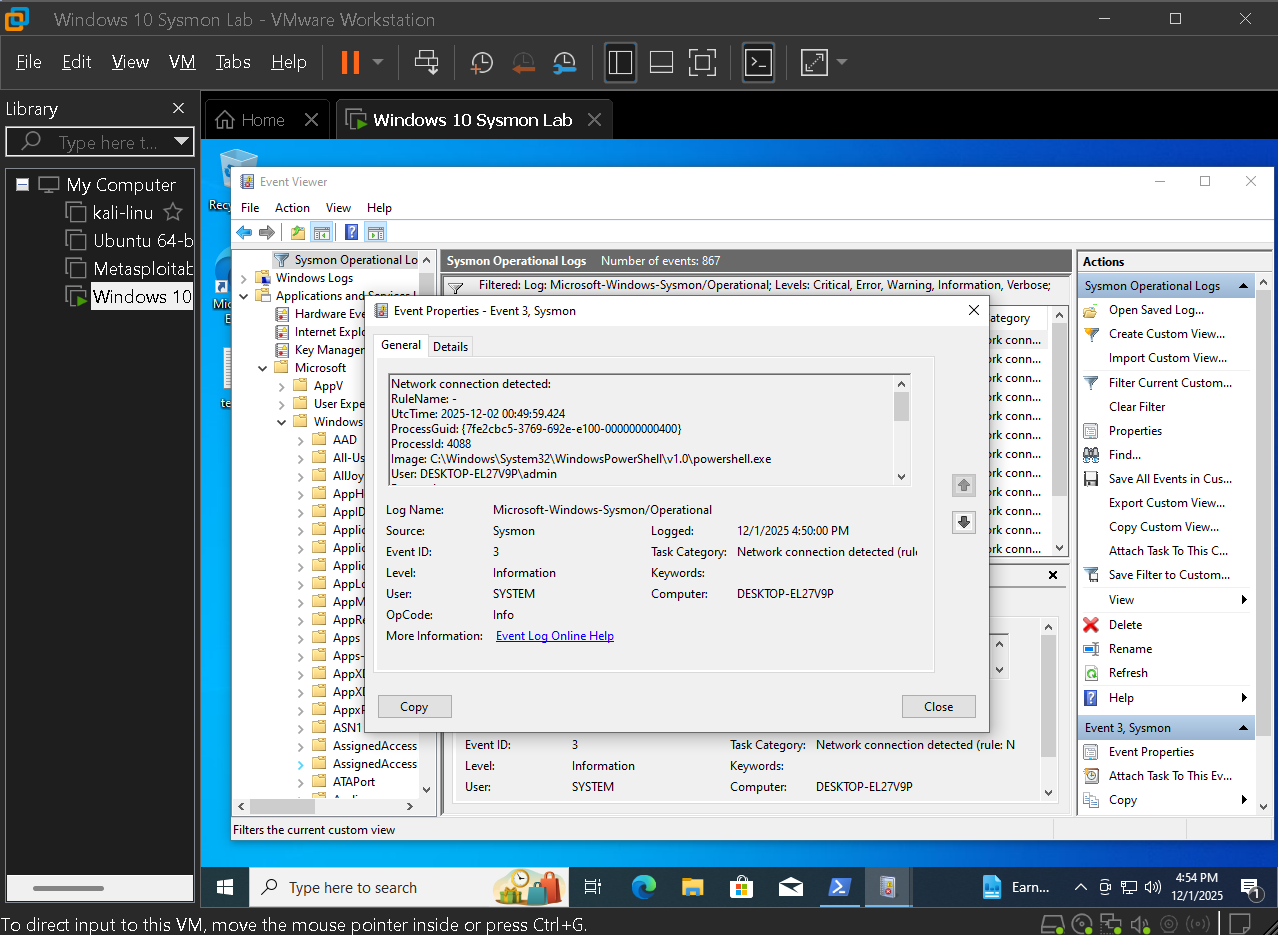
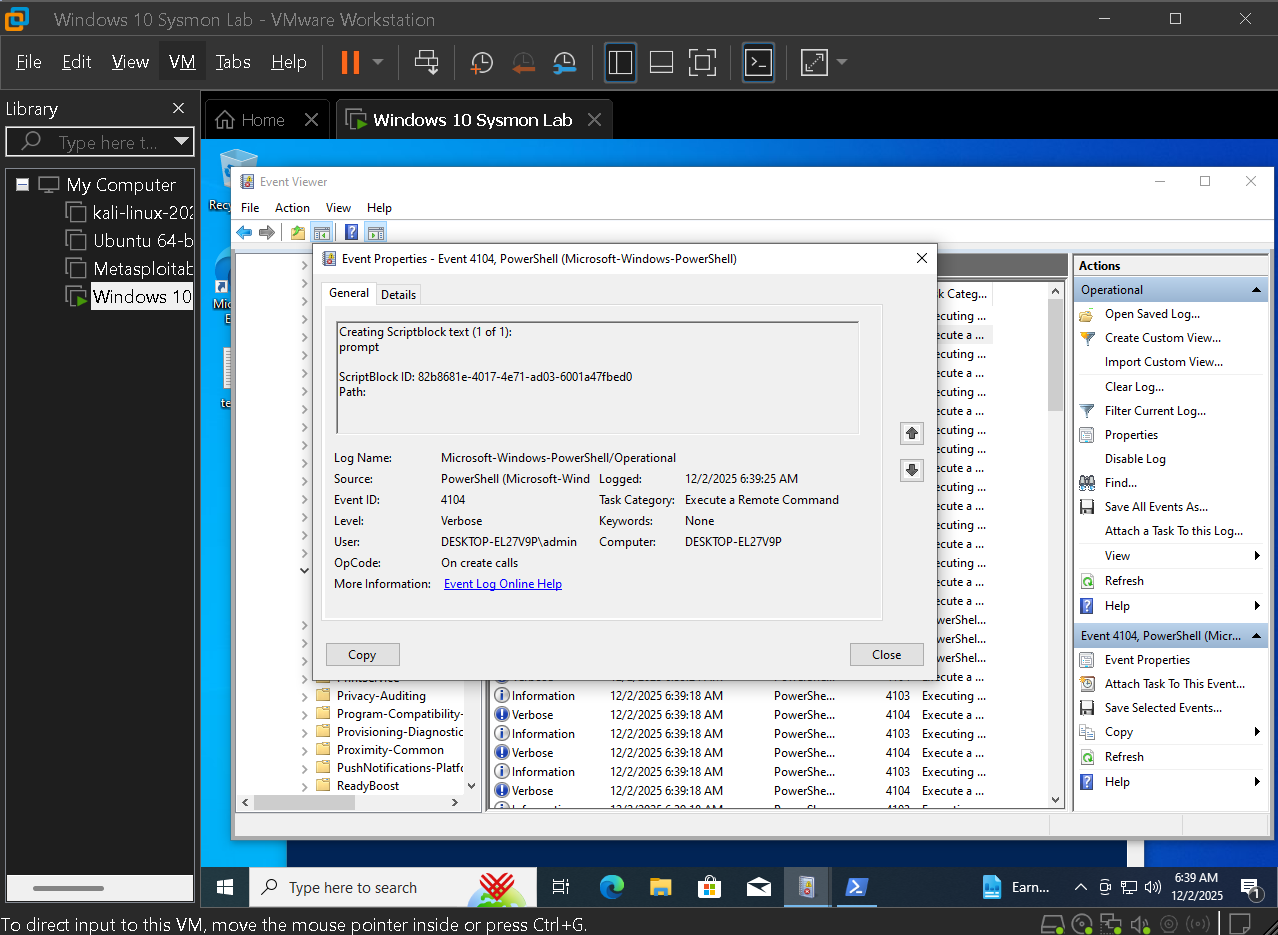
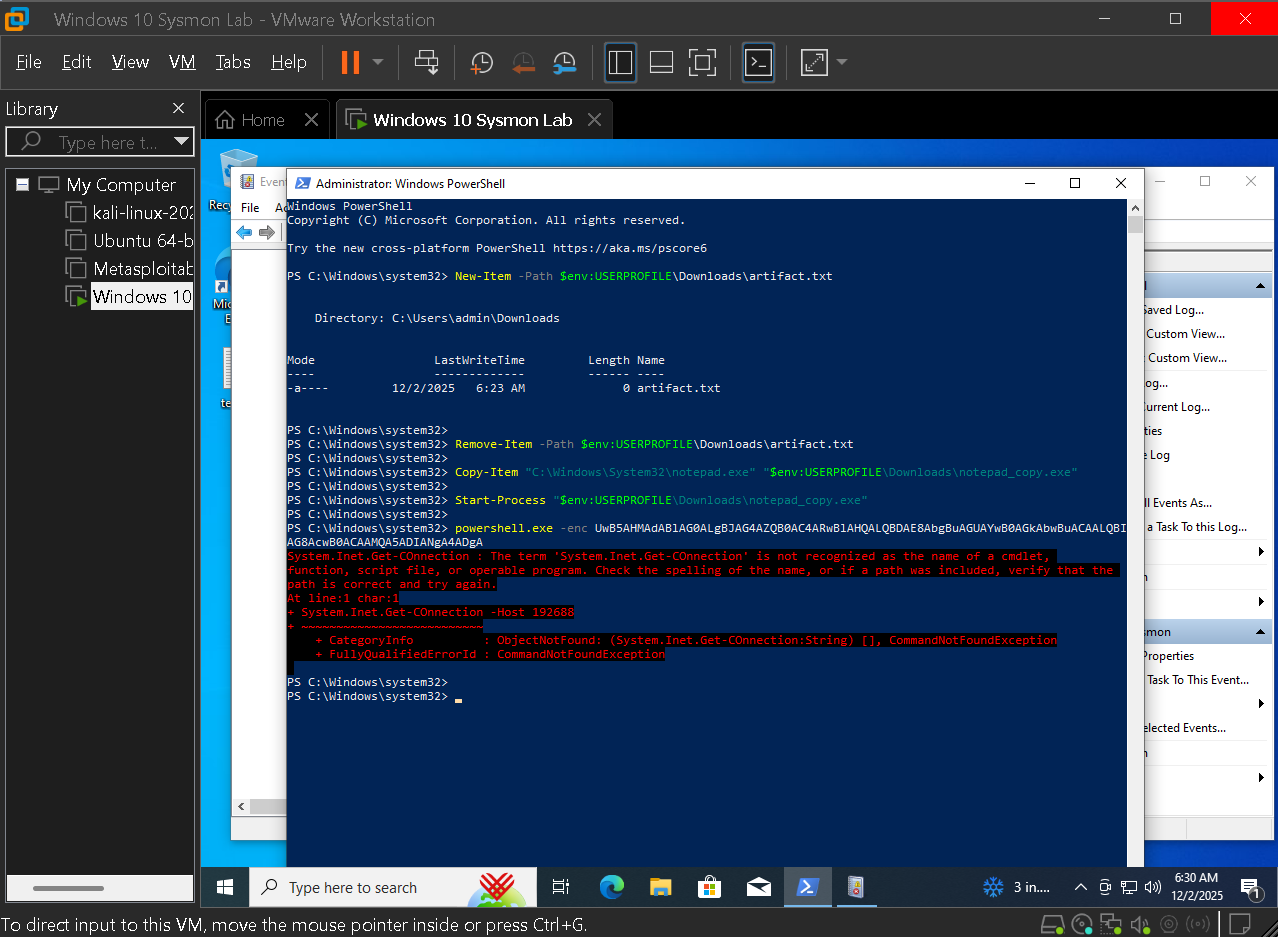
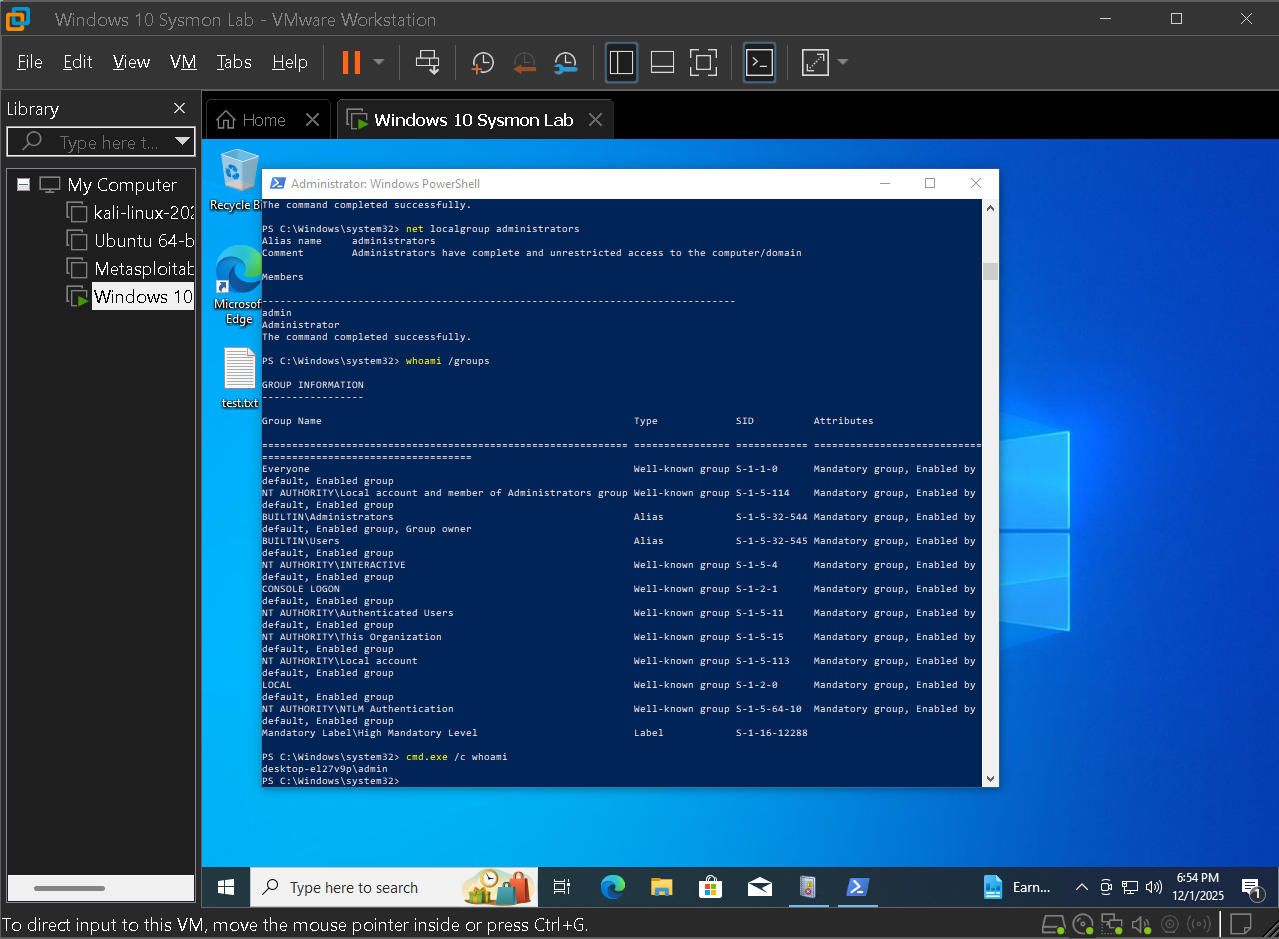
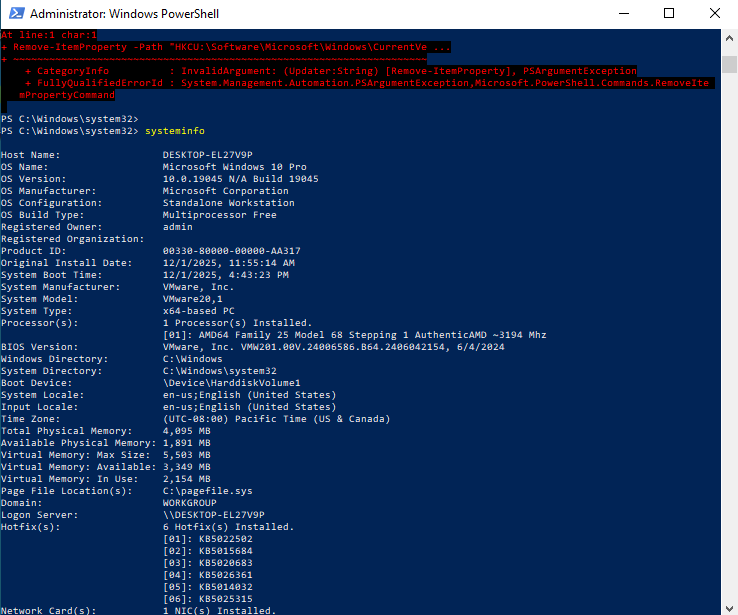
This lab was approached as if one Windows endpoint was assigned for monitoring as a junior SOC analyst. The objective was to prepare a clean baseline, add tuned logging with Sysmon, then follow how the host changes as simulated attacker behavior is introduced.
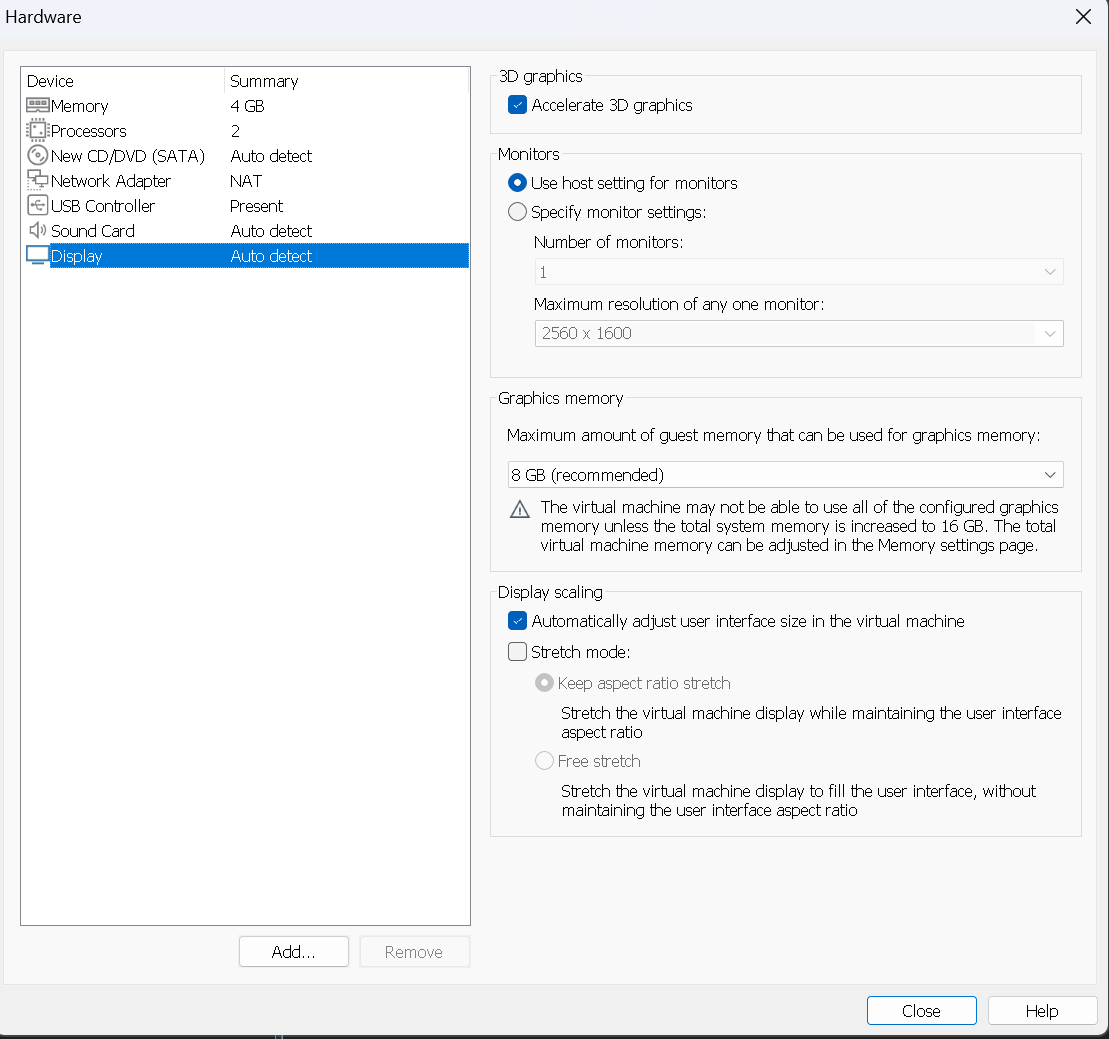
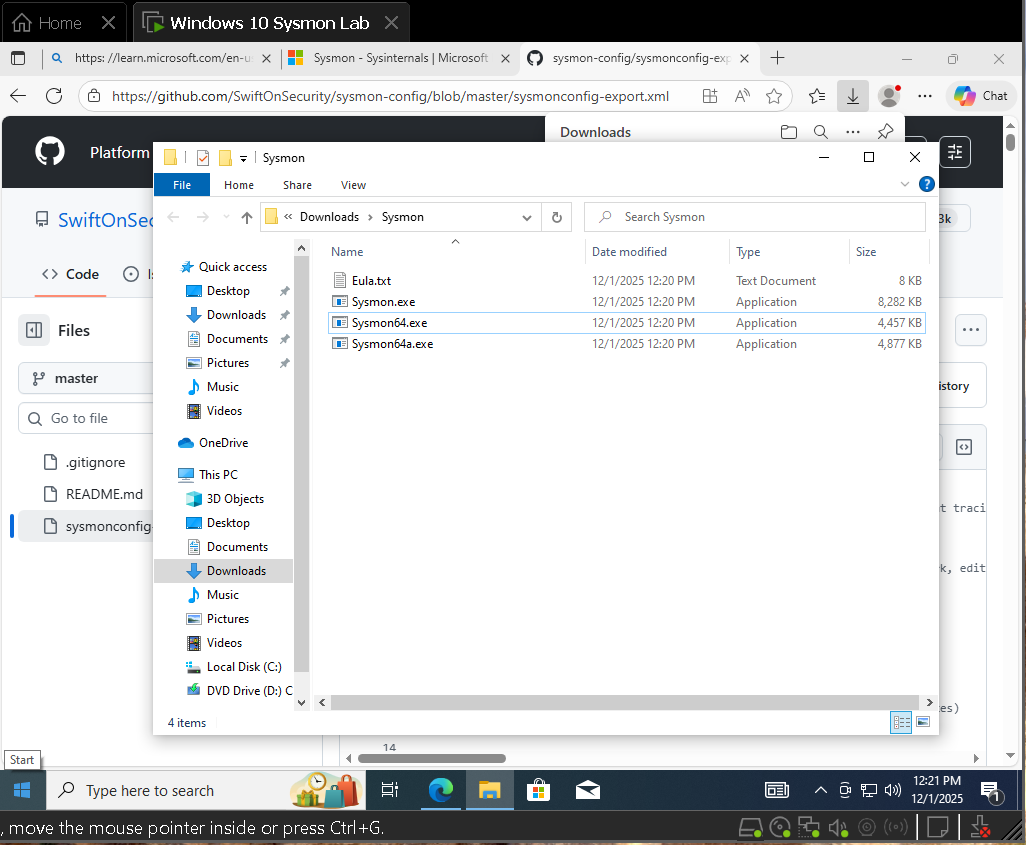
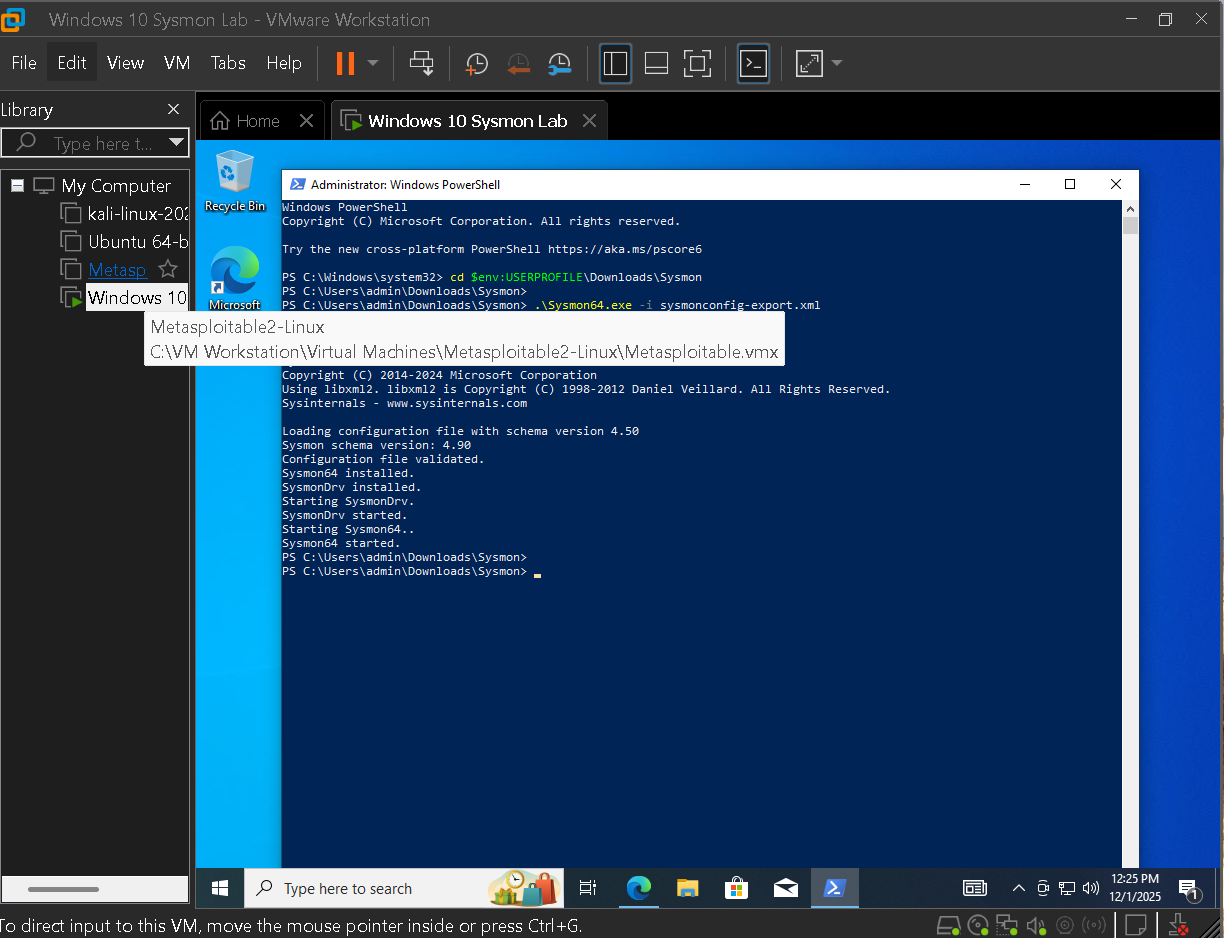
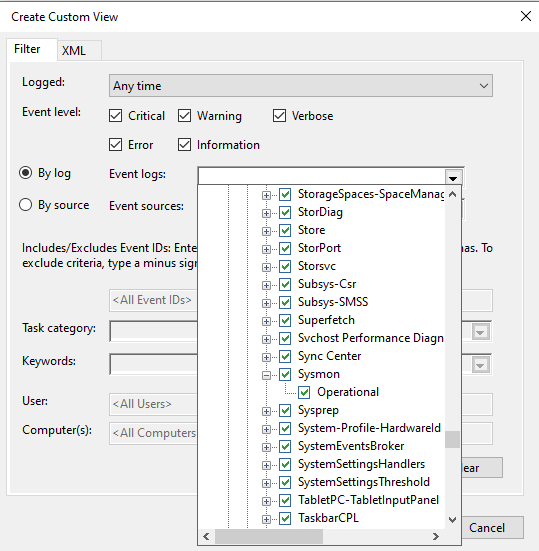
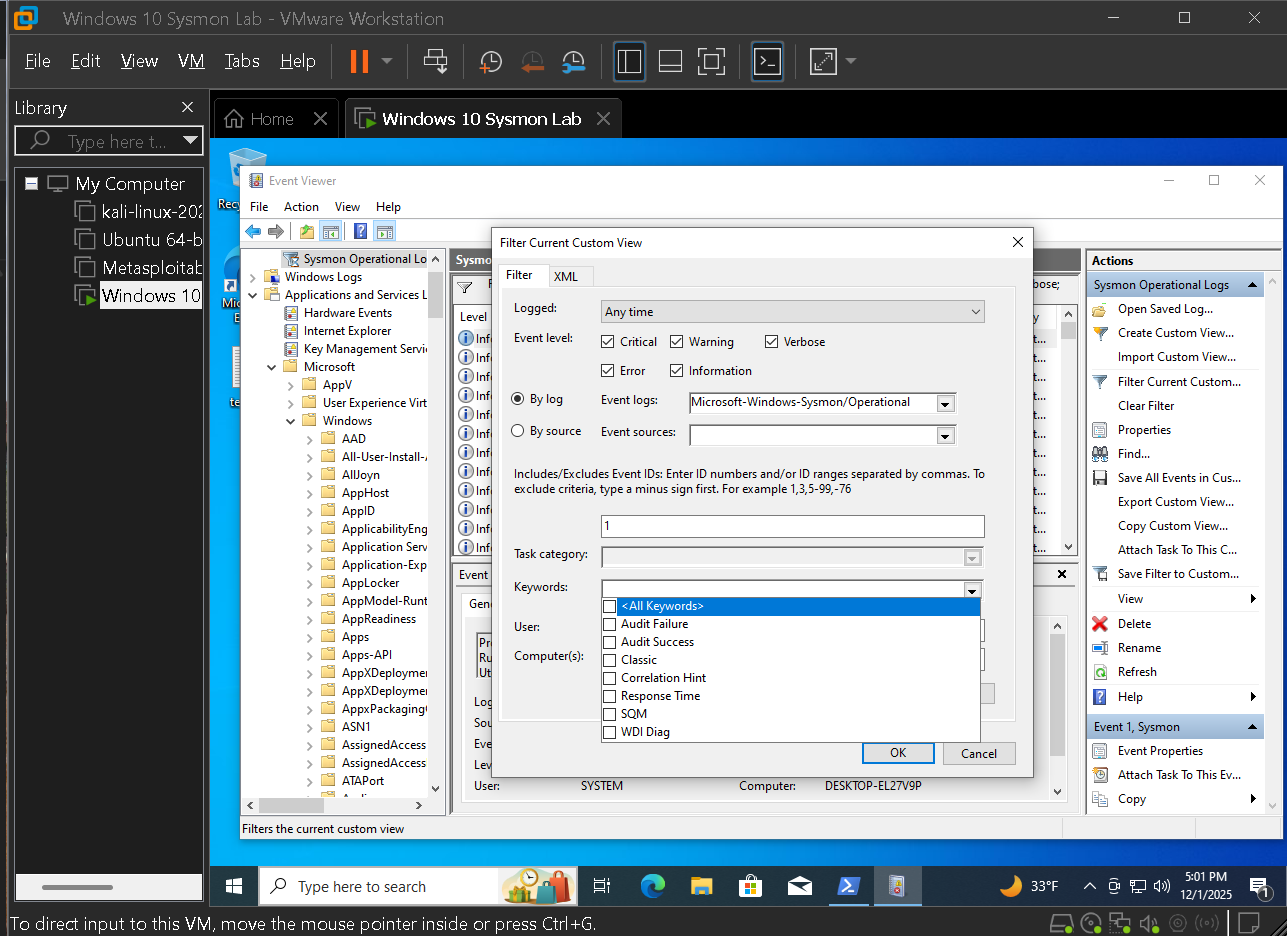
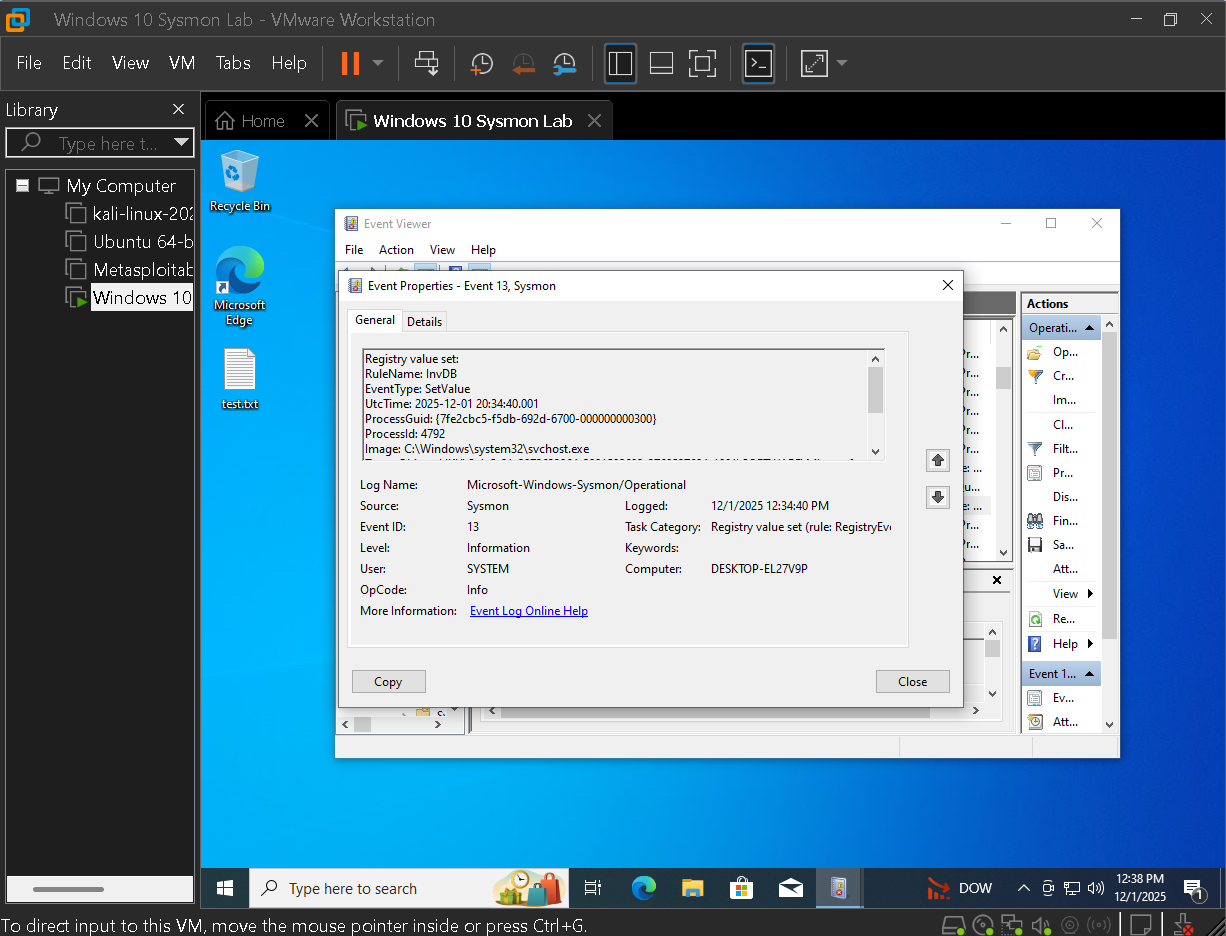
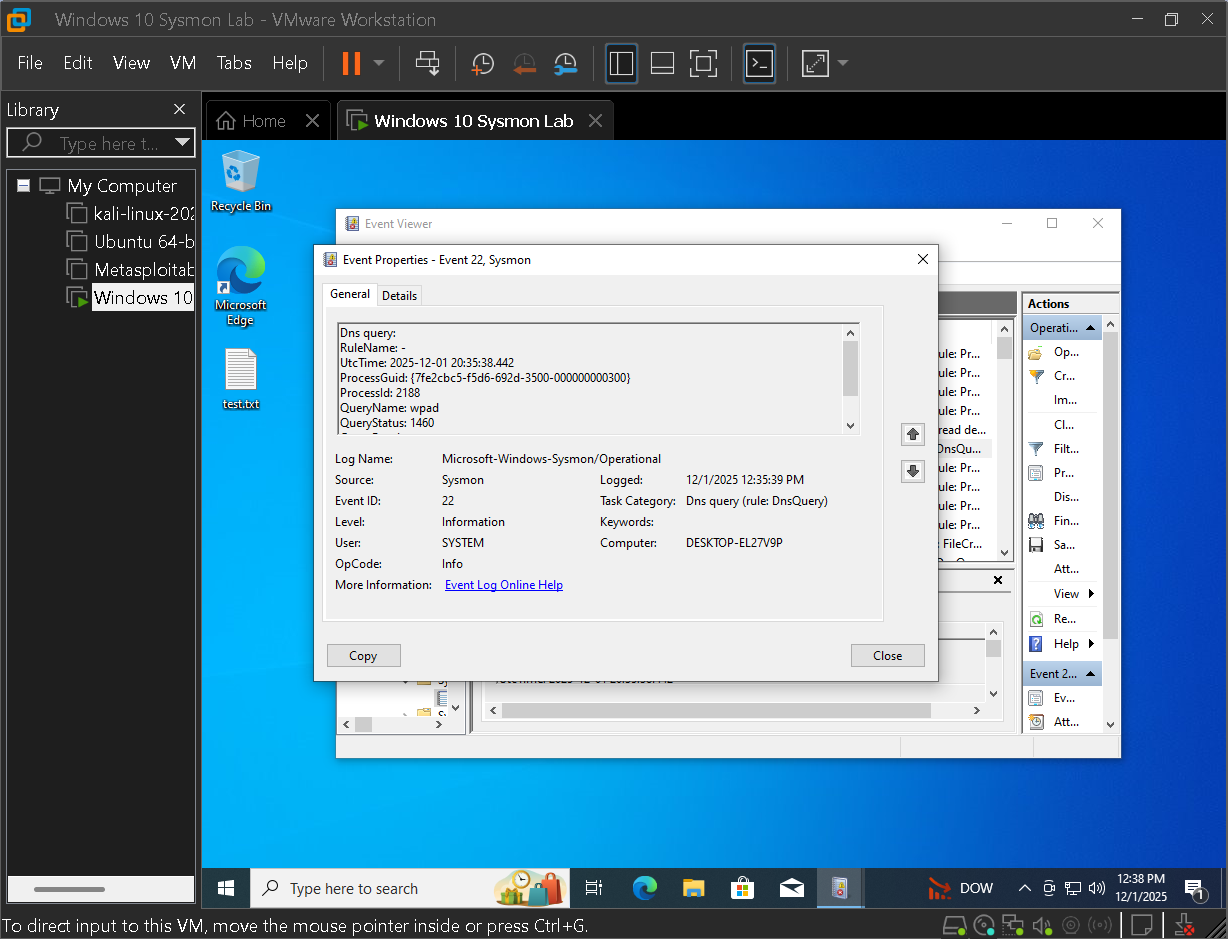
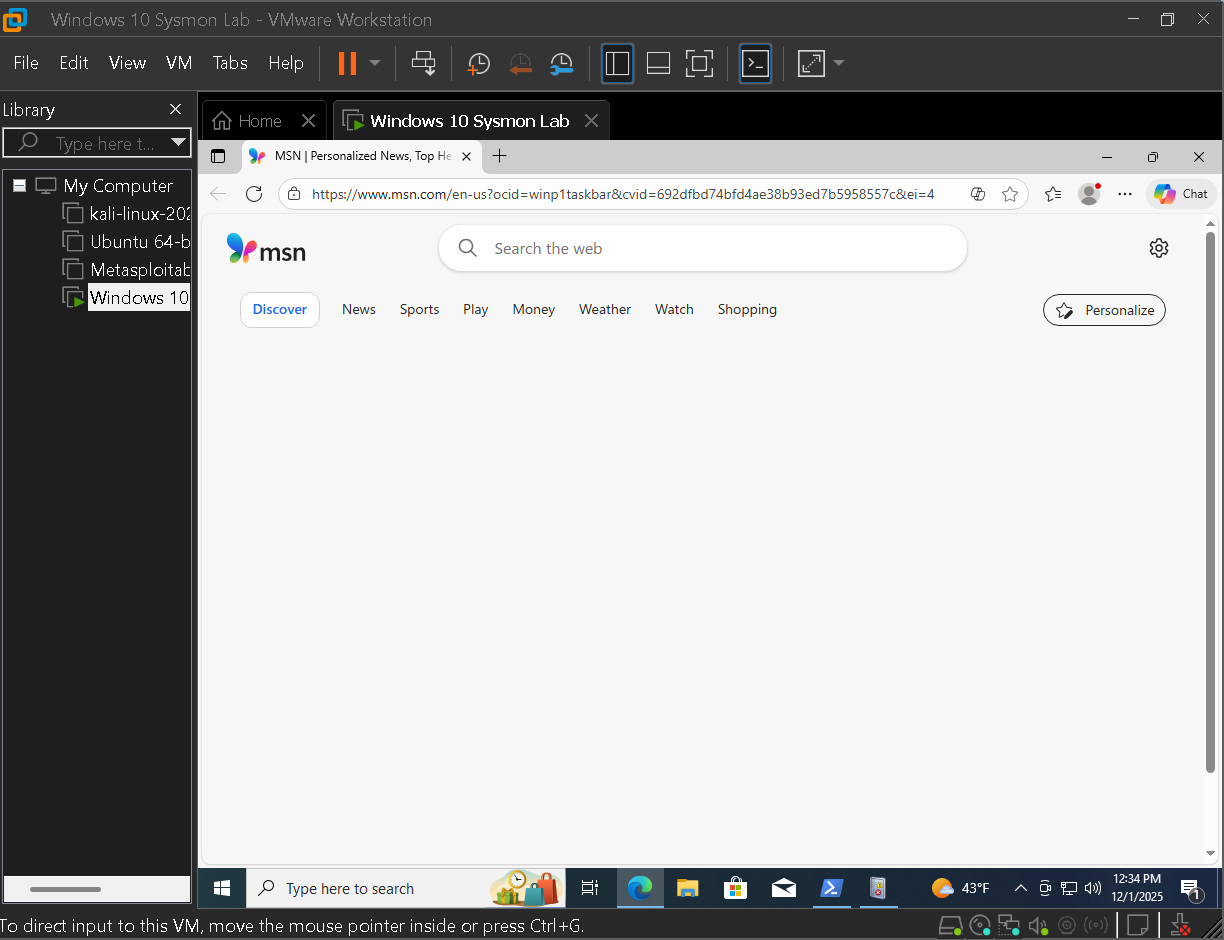
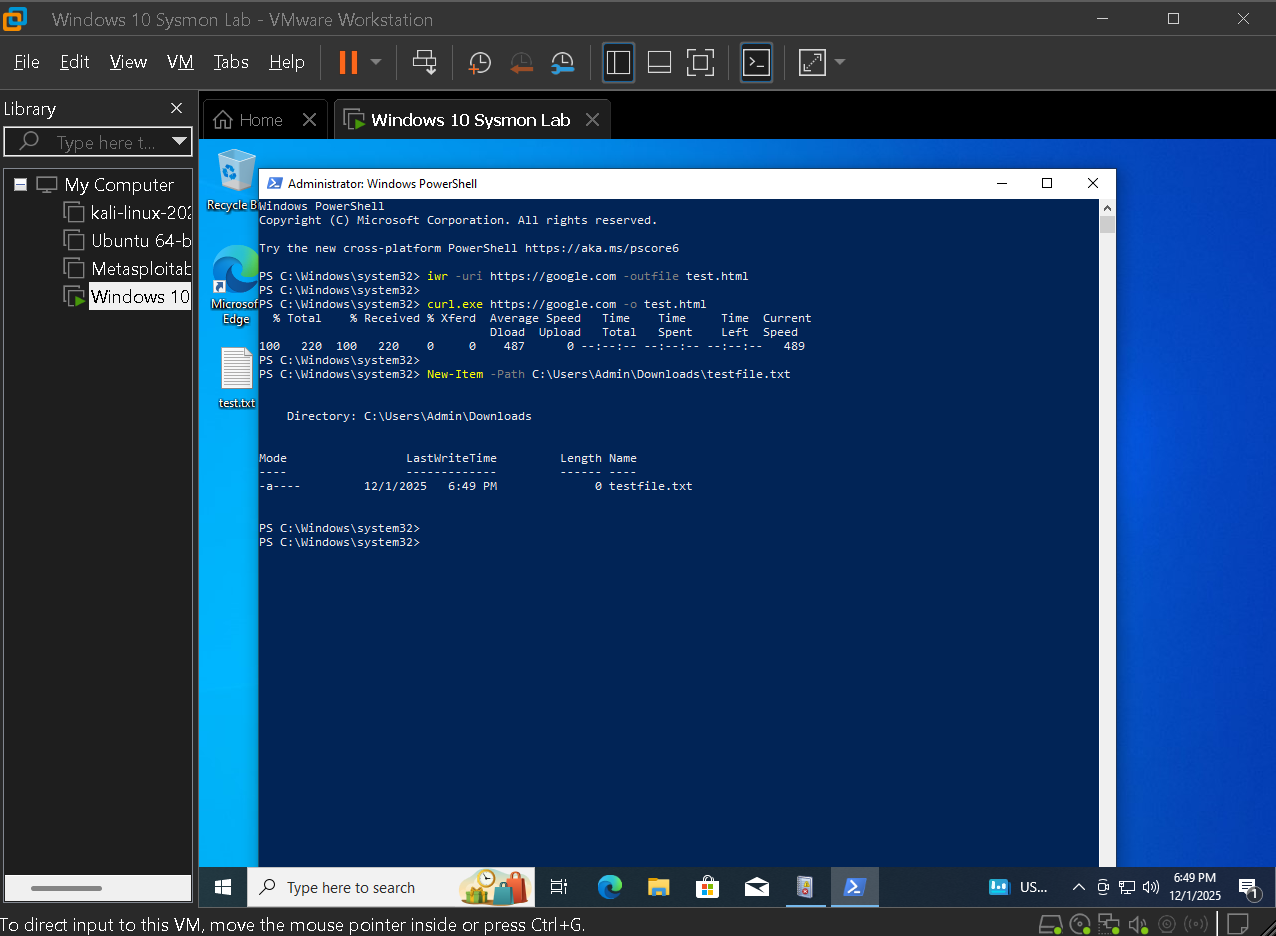
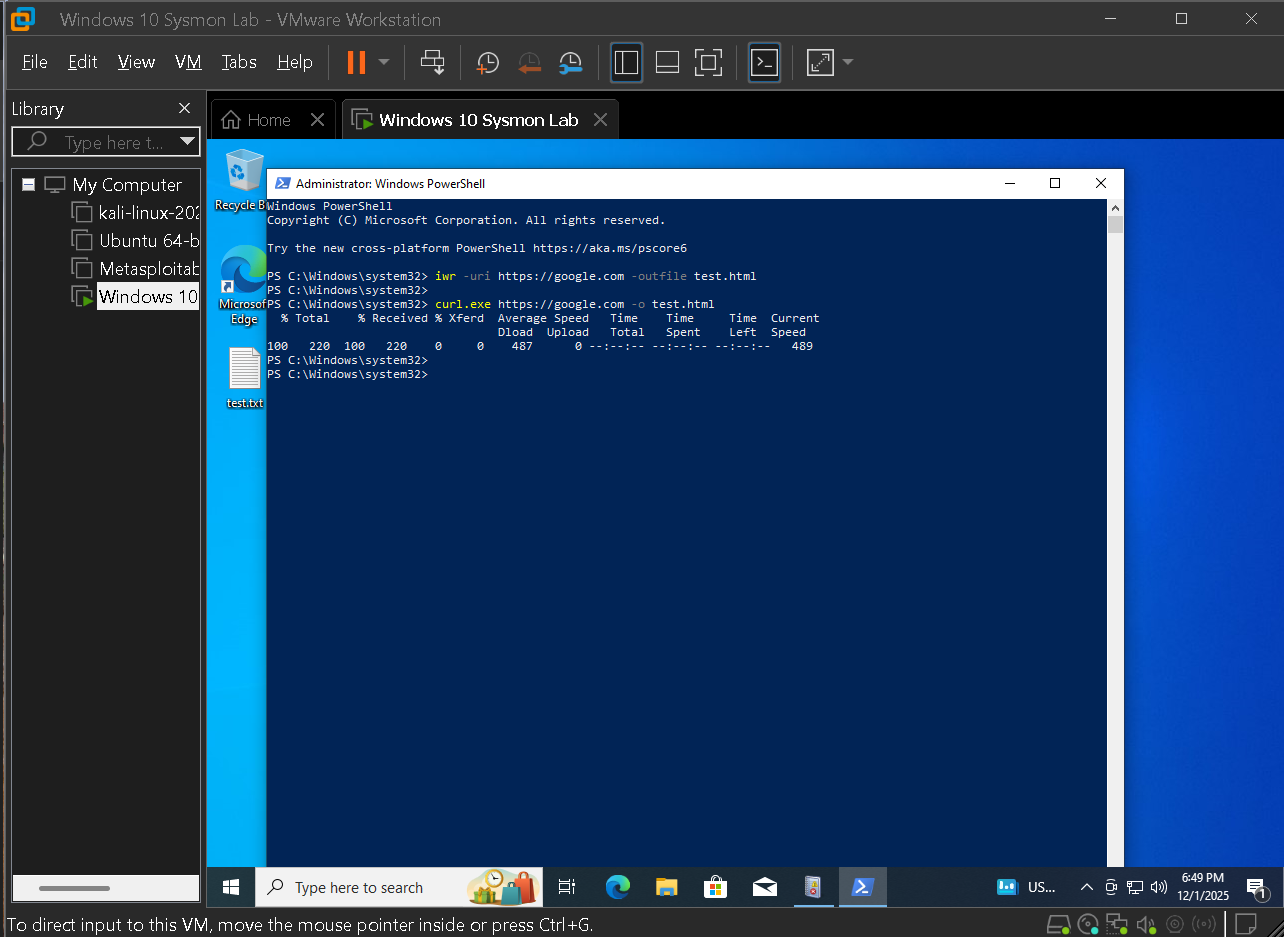
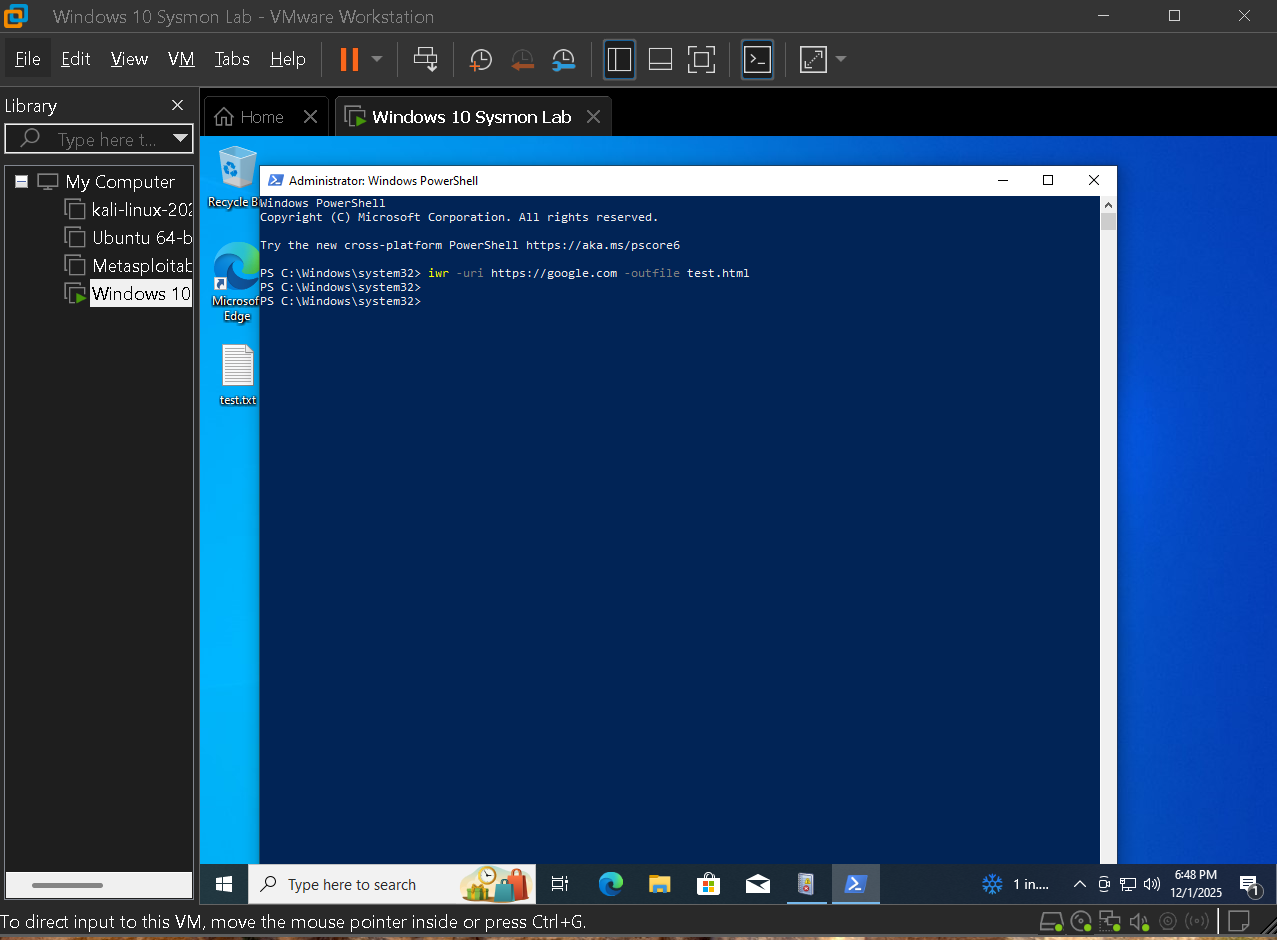
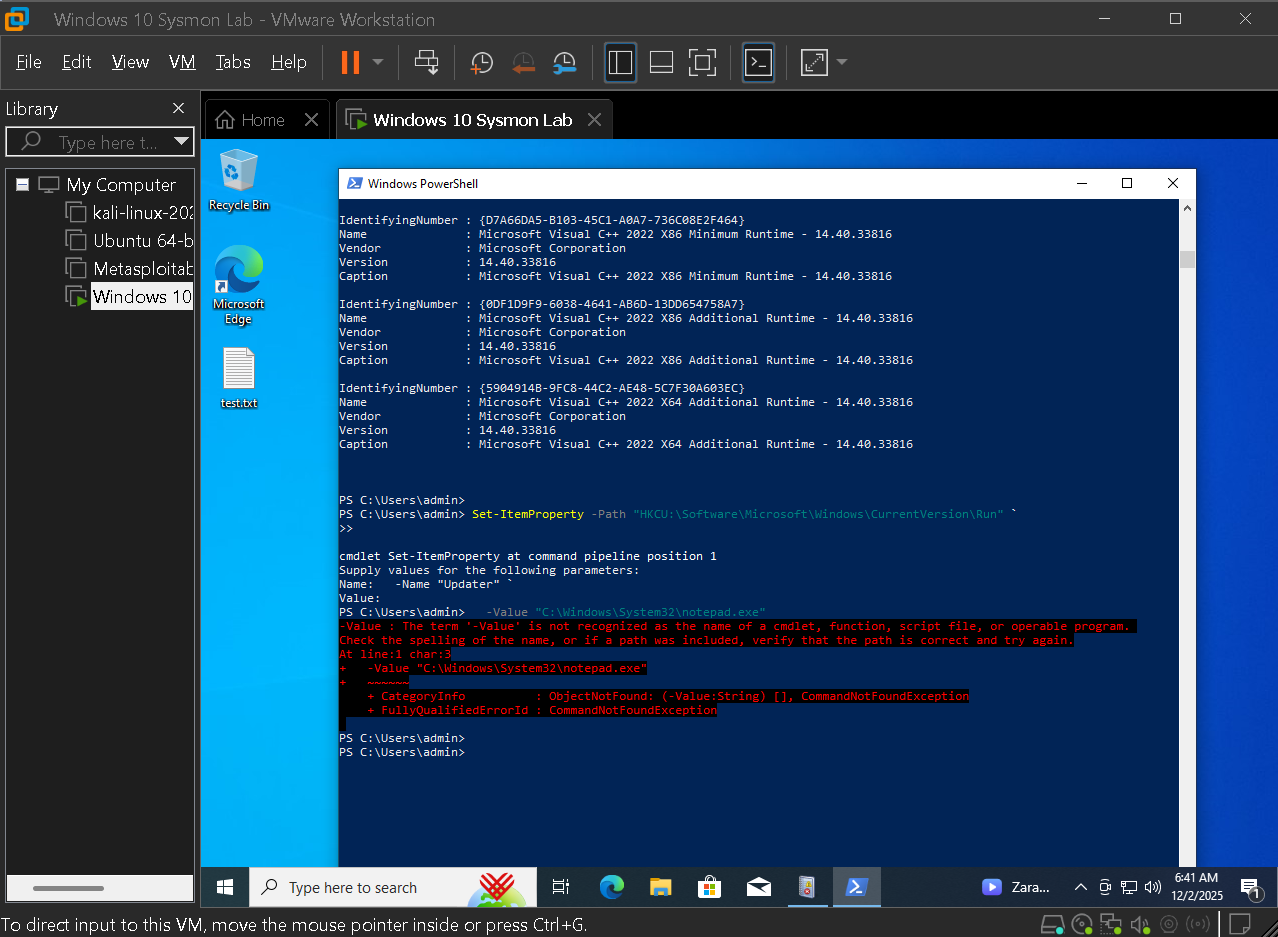
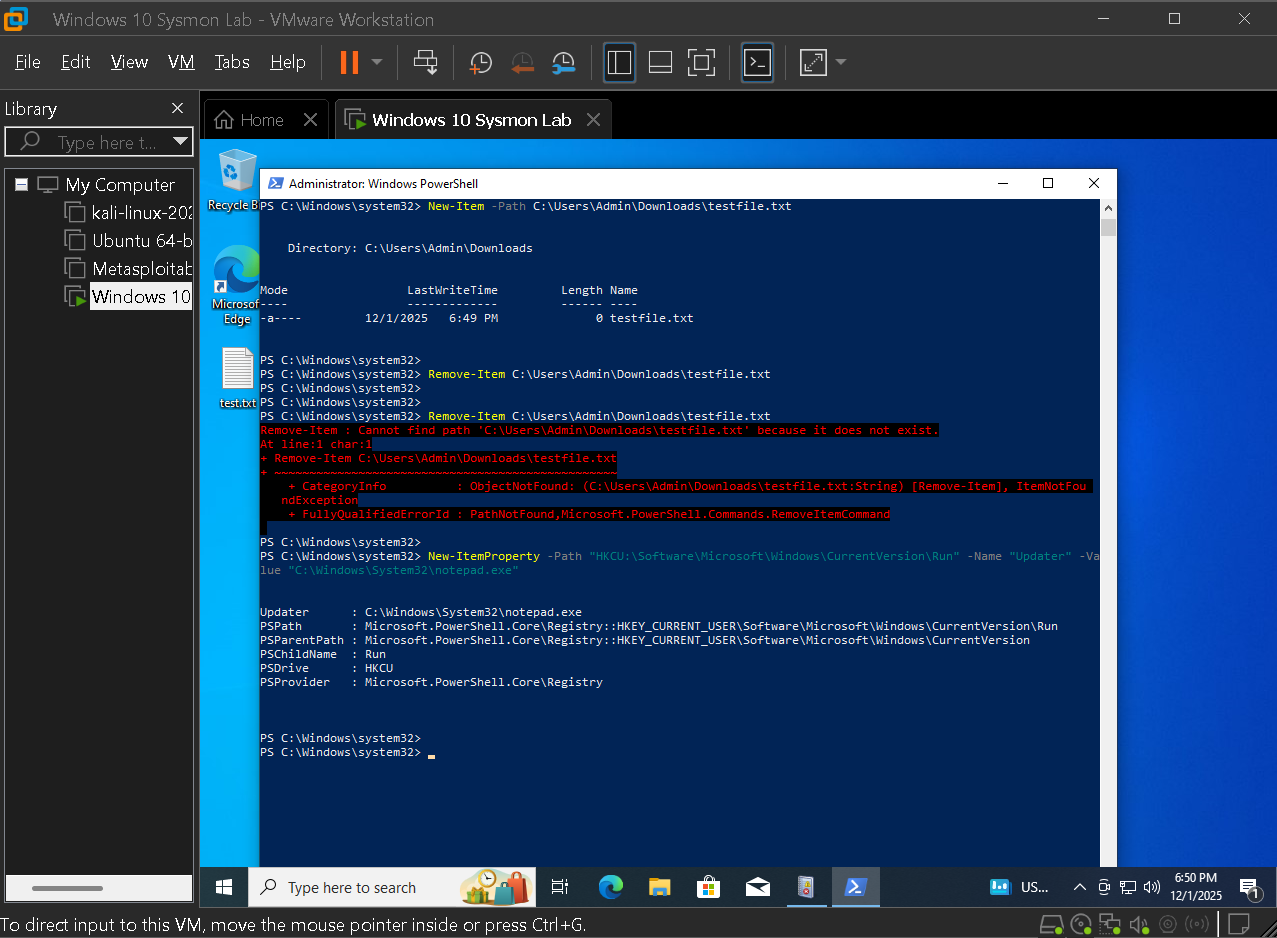
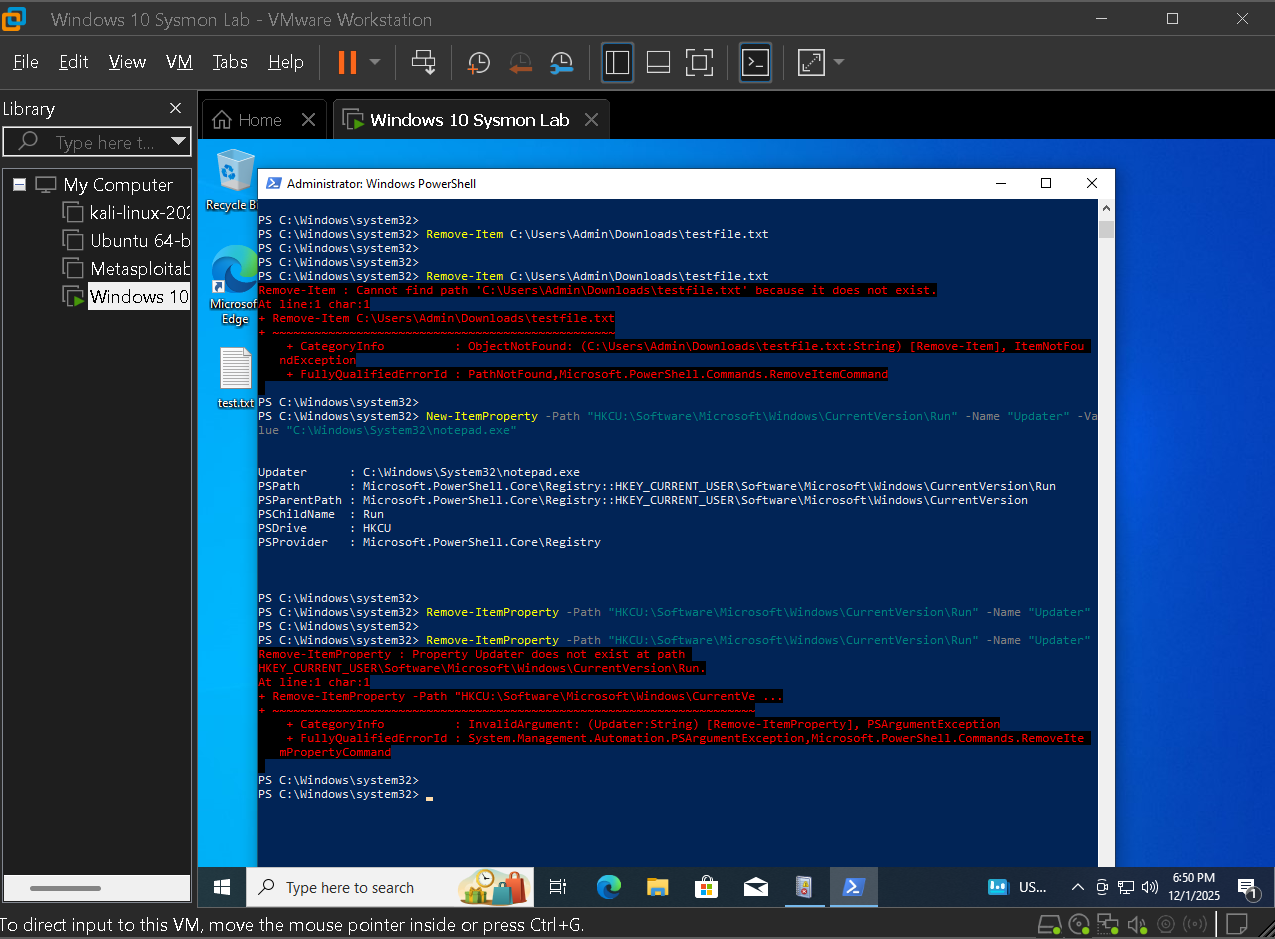
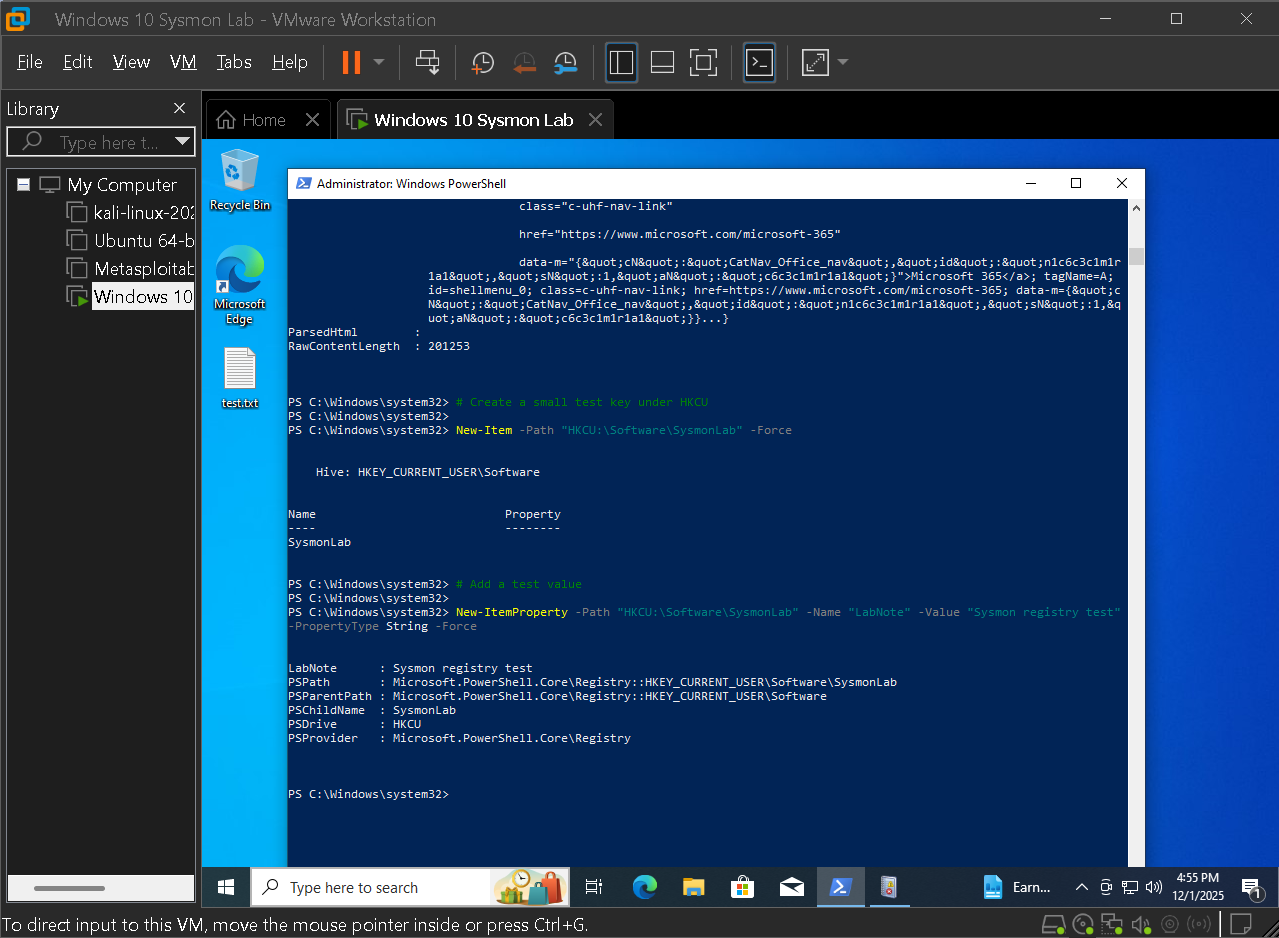
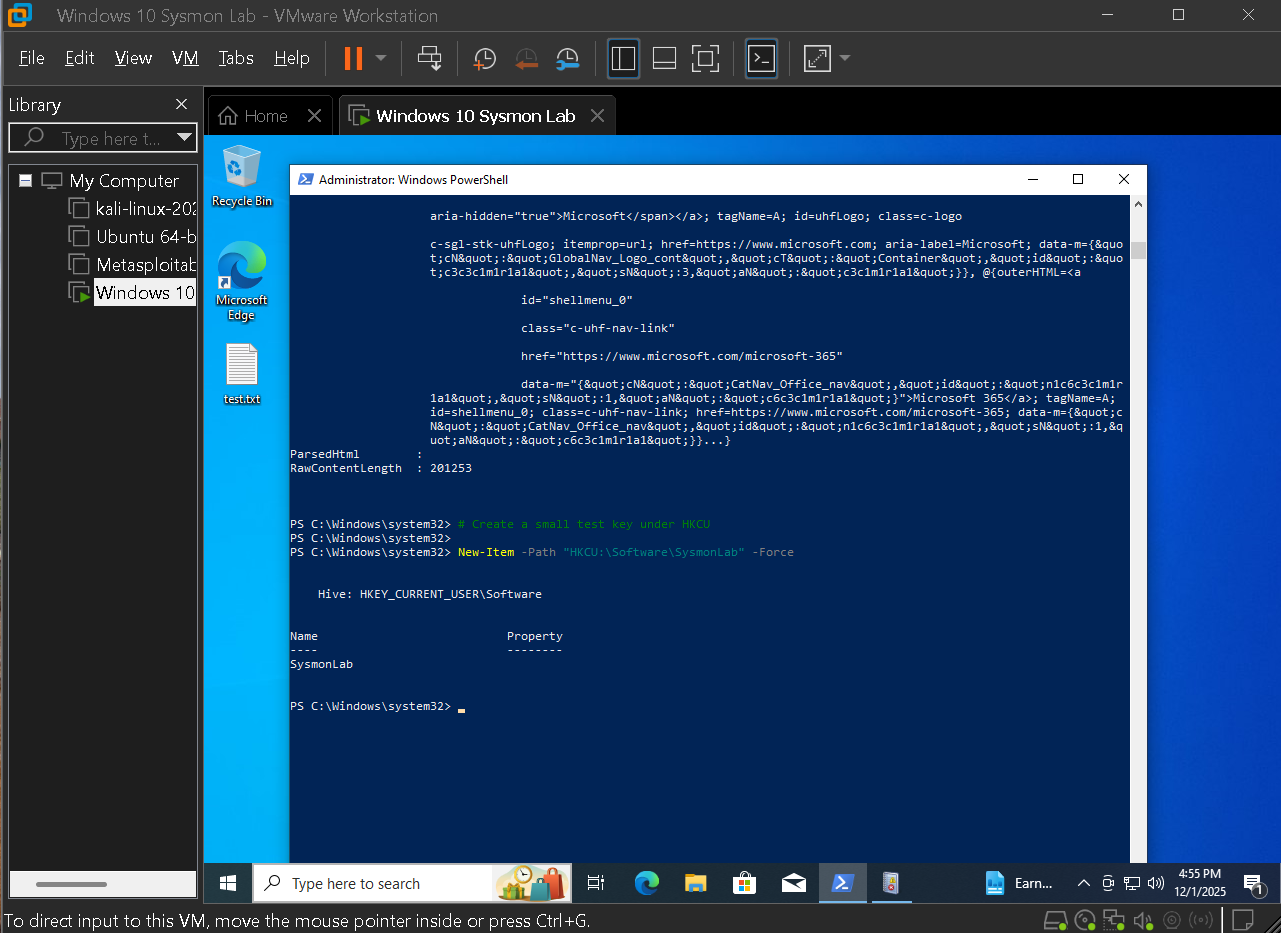
Starting from a fresh Windows 10 VM, privacy was locked down, the hardware profile was tuned, an analysis desktop was configured, and then Sysmon was deployed with a community configuration similar to what blue teams use in production. From there, high value event IDs were focused on and investigations that mirror real cases were walked through, such as LOLBin downloads, Run key persistence, encoded PowerShell commands, and command and control style traffic.